John, AKA NASAnut in the live chatroom sends a spectacular gift to us. We’ll talk about a free Mac utility called Typeeto that lets you use your Mac as a Bluetooth keyboard for your iOS devices and AppleTV. Joe LaGreca gives us a review of the secure messaging service, Wire, with full instructions on how to install and configure it. I’ll tell you how I made fire, otherwise known as how I wrote an actual Mac application using Automator and bash shell scripts (you can download it here but make sure you read the Read Me!) We’re also joined by Bart Busschots for another session of Security Bits.
Hi this is Allison Sheridan of the NosillaCast Mac Podcast, hosted at Podfeet.com, a technology geek podcast with an EVER so slight Macintosh bias. Today is Sunday September 4, 2016 and this is show number 591.
 Sometimes when you start a new endeavor, you think you know what you’re getting into. Maybe you realize that it’s an unknown ahead but you at least have a vision. I went into podcasting because I had something to say and I thought maybe a few people would be interested in hearing my views on technology. That has turned out to be the case, but there was a very unexpected consequence. This podcast has heart. The heart wasn’t created by me, but by you. Over the years so many wonderful experiences for both Steve and me have come from the caring and thoughtfulness of the NosillaCastaways.
Sometimes when you start a new endeavor, you think you know what you’re getting into. Maybe you realize that it’s an unknown ahead but you at least have a vision. I went into podcasting because I had something to say and I thought maybe a few people would be interested in hearing my views on technology. That has turned out to be the case, but there was a very unexpected consequence. This podcast has heart. The heart wasn’t created by me, but by you. Over the years so many wonderful experiences for both Steve and me have come from the caring and thoughtfulness of the NosillaCastaways.
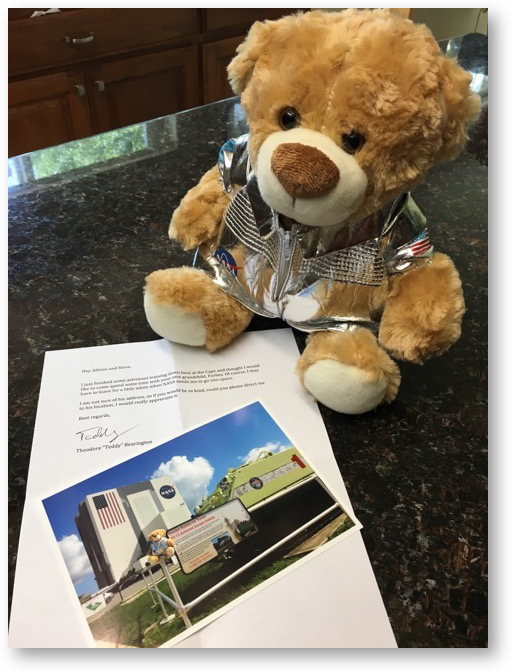
This week we received the most wonderful gift. John, also known as NASAnut in the live chatroom sent a package to us. There were three things in the package. The first was a photo of the iconic NASA Vehicle Assembly Building. Sitting on the railing in front of the building was a small teddy bear. The second thing in the box was this letter from Teddy:
Hey Allison and Steve,
I just finished some astronaut training down here at the Cape and thought I would like to come spend some time with your new grandchild, Forbes. Of course, I may have to leave for a little while when NASA needs me to go into space.
I am not sure of his address, so if you would be so kind, could you please direct me to his location, I would really appreciate it.
Best regards, Teddy
Theodore “Teddy” Bearington
And the third thing in the box, you’ve probably figured out by now, was Teddy himself, wearing a shiny silver astronaut suit! He’s got the NASA emblem on the front, a Space Shuttle patch on his right arm, and a US flag on his right arm. He’s absolutely adorable. I can’t believe how thoughtful and kind it was of John to send this on to us.
I am forever grateful for all of the kindness of of the NosillaCastaways, from teddy bears for our grandson to sausage grinders for my mantel. You guys are amazing.
Chit Chat Across the Pond
This week on Chit Chat Across the Pond, Bart is back for installment 20, where we take our first baby step outside of his JavaScript playground. He shows us how using the Console in any modern browser, you can change the way a browser page looks to you (not changing the original content. It’s great fun and an easier one of his lessons!
I want to give a shout out to Daniel El Travis who tweeted that he was inspired by Bart Busschots’ and my Taming the Terminal series. He posted a video of how he used the terminal to query a giant database from the Missouri Department of Corrections. He’s in there grepin’ and using regular expressions and everything. It’s awesome! I put a link in the shownotes to his awesome video on youtu.be/…. He even says in the video that he’s not a not a computer programmer and that he’s pretty proud of himself for doing this. THAT’S the power that Bart is giving us with demystifying these things. Thanks Daniel, that was so cool!
Blog Posts
Use Your Mac as a Bluetooth Keyboard for iOS and AppleTV with Typeeto
Secure Messaging with Wire from Joe LaGreca
Next up let’s listen to a listener review from Joe LaGreca about the secure messaging system Wire.
The text of Joe’s reviews including instructions including screenshots are available at: docs.google.com/…
I installed Wire per Joe’s instructions but I tested to see if I could do the installation of Wire without giving up my cell phone number. Turns out you can, so I registered instead with just my email address. I don’t give out my cell number but obviously my email address is everywhere. It’s an interesting platform, and I’m curious to see if it will take off. I’m in there so if you want to chat, see if you can find me by email!
DropShadow App Made With Automator and ImageMagick
Security Bits pre-correction
Before I play Security Bits, I want to make an adjustment to something you’ll hear me say. Bart highlights a Naked Security article about a paper presented at the Usenix conference by researchers from the University of North Carolina. In their paper they describe how they were able to use publicly available photos from social media sites to create 3D renderings of faces in order to spoof facial recognition software for logins. When Bart tells me about it, you’ll hear me say that I wondered about the Windows facial recognition (called Windows Hello) that Rod Simmons showed me.
I posted the Naked Security article in the SMR Podcast Facebook group and Joel Rushworth said that this technique wouldn’t work on Windows Hello because Microsoft uses infrared sensors in their solution. I decided to do some digging. I followed the link in the Naked Security Post to the original research paper and on page 509 I found this paragraph:
Infrared Illumination: Microsoft released Windows Hello as a more personal way to sign into Windows 10 devices with just a look or a touch. The new interface supports biometric authentication that includes face, iris, or fingerprint authentication. The platform includes Intel’s RealSense IR-based, rather than a color-based, facial authentication method. In principle, their approach works in the same way as contemporary face authentication methods, but instead uses an IR camera to capture a video of the user’s face. The attack presented in this paper would fail to bypass this approach because typical VR displays are not built to project IR light; however, specialized IR display hardware could potentially be used to overcome this limitation.
So when you hear Bart and me saying facial recognition can’t be trusted, we were wrong in the case of Microsoft Hello. Very cool to hear and be corrected in our thinking!
Security Bits with Bart Busschots
Important Security Updates
- Reminder – Apple have released iOS 9.3.5 to patch a trio of bugs that were being exploited in the wild through a malware toolkit that is for sale to governments (Allison covered the story very well last week) – arstechnica.com/…
- RELATED – Apple have pushed out security updates for OS X 10 (Yosemite & El Capitan) and Safari to address three 'Trident' bugs patched in iOS 9.3.5 last week – arstechnica.com/…
Important Security News
- The Washington Post reveal the 98 data points FaceBook try to fill out in their user profiles – www.washingtonpost.com/…
- RELATED – an article outlining some disturbing 'edge cases' in FaceBook's People you may Know feature – nakedsecurity.sophos.com/…
- There is another new attack against HTTPS (and anything else that use TLS like OpenVPN). It relies on the fact that sysadmins tend to keep old cypher suites enabled for backwards compatibility – in this case, old 64bit cyphers like 3DES are the culprits. The attack is called Sweet32, and again, is one for sysadmins to fix rather than users to panic about – nakedsecurity.sophos.com/…
- CA congressman Ted Lieu is pushing for the US FCC to tackle the vulnerabilities in the SS7 protocol that make it possible for attackers to hijack and intercept cellphone numbers, calls, SMS messages, and data (thanks to listener Lynda for the tip on this) – arstechnica.com/…
- Sony add 2 Step Validation to the PlayStation Network (PSN) – nakedsecurity.sophos.com/…
- Apple, Google & others join with the FTC to try curb the flood of unsolicited robocalls in the US – www.wired.com/…
- Hacking tools belonging to the NSA-affiliated hacking group The Equation Group have been leaked, having been found lying around on an infected router. This is seen as evidence that the NSA cannot keep secret backdoors secret – www.macobserver.com/…
- RELATED – the hacking tool allowed the NSA to compromise a large array of commonly used Cisco routers for a decade, allowing them to eves drop on network traffic, and even to see into VPN sessions terminating on infected routers. Initially it was believed the vulnerability only existed on older PIX routers, but that has been found to be false, and it affects much more recent routers too – arstechnica.com/… & arstechnica.com/…
- WhatsApp have updated their privacy policy, and users who do not take action will have their phone numbers shared with FaceBook. You can opt out though, but they didn't make it easy or obvious – www.macobserver.com/…
- The Mac BitTorrent client Transmission was infected with Malware yet again (5 months since the last time). A version of the app published on the app's official website on August 28th was found to bundle the OSX/Keydnap malware, and, to be digitally signed with Transmission's code signing key. The infected app was quickly removed, but anyone who downloaded the app on the 28th or 29th of August could well be infected with the malware – www.intego.com/…
- Yahoo settle a law suit that could have been a big deal for companies who make their money by scanning email so they can target ads, and get a settlement that basically amounts to no change – emails must hit the inbox or sent box before they are scanned, rather than being scanned before they arrive all the way – nakedsecurity.sophos.com/…
- Two different studies find that we humans are just terrible at this security thing:
- 87% of people ignore security warning messages – nakedsecurity.sophos.com/…
- 56% of email users, and 40% of FaceBook users click on links from unknown senders – nakedsecurity.sophos.com/…
Notable Breaches
- US clothing chain Eddie Bauer announced that it removed malware from POS terminals in all of it's 350+ stores, and that those terminals had probably been stealing credit and debit card numbers during the first six months of 2016 – krebsonsecurity.com/…
- A number of forums run by gaming company Epic have been breached – nakedsecurity.sophos.com/…
- Opera has se-set the passwords of all 1.7m users of its sync service, which syncs browser data, including passwords, between devices. Opera also recommend changing all passwords synced through the service – nakedsecurity.sophos.com/…
- A dump of 68M DropBox email addresses and salted & hashed passwords from 2012 has surfaced – DropBox are forcing password re-sets on affected accounts – arstechnica.com/…
- Kimpton Hotels officially acknowledged that malware had infected some of the POS terminals in their hotels and restaurants from 16 February to 7 July 2016 – krebsonsecurity.com/…
- 43m Usernames and password from a 2012 breach of last.fm have surfaced, and because the passwords were hashed with the obsolete MD5 algorithm, they have been cracked, so we can scoff at how terrible many of them were – arstechnica.com/… & nakedsecurity.sophos.com/…
Suggested Reading
- Allison sent me a link to a very cool Mac app that should provide some defence against malware called Little Flocker – it's like Little Snitch, but for file access instead of network access – www.zdziarski.com/…
- A great post from Intego that gives short human-friendly definitions of common terms like Malware, Virus, Trojan etc. – www.intego.com/…
- 5 tips to keep your kids safe online as they go back to school – nakedsecurity.sophos.com/…
- The US Federal Trade Commission (FTC) has issued an alert on securing personal information when using rental vehicles – www.us-cert.gov/…
- A nice tutorial on using Find My iPhone/Mac from TidBITS – tidbits.com/…
- Security researchers use a 'handful' of photos to create a 3D model of a face that can trick facial recognition systems – nakedsecurity.sophos.com/…
- A coalition of tech companies and groups has joined the fight against the plan to harvest social media account names at the US border with an open letter than explains why it would be ineffective, expensive, and a gross invasion of privacy – nakedsecurity.sophos.com/…
- A new way to abuse vulnerabilities – short trade on them, then publish the news to drive the stock down and profit – arstechnica.com/…
- After attacks on a number of state election boards in the US, the FBI warn there could be more on the way – arstechnica.com/…
- RELATED – State Officials say the FBI told them Russians were responsible for the attacks on the Arizona state elections board – arstechnica.com/…
- USBee – software developed by security researchers that turns any USB thumb drive into a (slow) radio transmitter which can exfiltrate data at about 80bytes per second – arstechnica.com/…
- NY Governor Quomo announces that the NY DMV's improved facial recognition is succeeding in detecting fraudulent applications, and helping keeping dangerous drivers off the road, with more than 1,000 arrests – nakedsecurity.sophos.com/…
- Another blunder by a CA casts further doubt on the effectiveness of the public key infrastructure (PKI) – nakedsecurity.sophos.com/…
- Researchers improve the RowHammer attack to make it more effective, and to allow it to target VMs on shared cloud hosting with vulnerable RAM chips – arstechnica.com/…
That’s going to wind this up for this week. Don’t forget to send in your Dumb Questions, comments and suggestions by emailing me at [email protected], follow me on twitter @podfeet. Check out the NosillaCast Google Plus Community and our Facebook group at podfeet.com/facebook. If you want to join in the fun of the live show, head on over to podfeet.com/live on Sunday nights at 5pm Pacific Time and join the friendly and enthusiastic NosillaCastaways. Thanks for listening, and stay subscribed.
