Feedback & Followups
- 🇺🇸 A good analysis of the US router ban that had just broken last time: The United States router ban, explained — www.theverge.com/…
- Reported as a Probably Breach last time: 1.2 million Crunchyroll users confirmed impacted by data breach — cyberinsider.com/…
- Following from the recent story that the iPhone 17 is the first commercial smart phone approved for handling NATO secrets, Apple have shared that they have found zero examples of an iPhone in lockdown mode being successfully compromised — appleinsider.com/…
- We discussed AirSnitch when it was revealed in February, and said it would take time for the industry to respond, we now have a significant response: D-Link releases security fixes to address AirSnitch Wi-Fi attack threat — cyberinsider.com/…
- 🇪🇺 Attempts by some in the EU to break End-to-End Encryption have taken a big hit: EU votes to block extension of rules allowing private message scanning — cyberinsider.com/…
- Context:
- The EU Commission and some countries have been trying to pass Chat Control for many years. This would force CSAM scanning and make End-to-End Encryption illegal.
- So far, all attempts to pass the bill have failed
- A temporary compromise was agreed upon that would allow tech companies to choose to break encryption to scan for CSAM by granting a time-limited exception to the GDPR (privacy regulation)
- This vote was intended to simply kick the can further down the road to allow more time to get Chat Control passed, but it failed!
- As of April 3, 2026, all companies continuing to voluntarily scan private messages for CSAM are probably breaching the GDPR, but they are continuing to do so — www.politico.eu/…
❗ Action Alerts
- Google fixes actively exploited Chrome zero-day flaw, update now — cyberinsider.com/…
- iOS 26.4 Fixes over 35 Security Issues on iPhones — www.macobserver.com/…
- iOS 18.7.7 and iPadOS 18.7.7 Now Available for Older iPhones and iPads — www.macobserver.com/…
- Addresses the vulnerabilities used in the recently revealed DarkSword exploit chain
- Apple was initially withholding these patches from devices that could upgrade to iOS 26 but had not done so, but have now reversed that stance — appleinsider.com/…
- Related: Apple Sends Lock Screen Alerts To — thehackernews.com/…
- ⚠️ Adobe Reader Users: Adobe Patches Actively Exploited Acrobat Reader Flaw — thehackernews.com/…
- ⚠️ Samsung Galaxy S25 Owners: Samsung Galaxy S25 ships browser vulnerable to RCE and XSS attacks — cyberinsider.com/…
- No fix yet, so change your default browser to Chrome or Firefox ASAP!
- ⚠️ TP-Link Archer NX Owners: TP-Link warns users to patch critical router auth bypass flaw — www.bleepingcomputer.com/…
- ⚠️ GIGABYTE Laptop & Motherboard Owners: GIGABYTE Control Center vulnerable to arbitrary file write flaw — www.bleepingcomputer.com/…
- A timely reminder that you must keep your Android device patched: Android rootkit NoVoice infects 2.3 million devices via Google Play apps — cyberinsider.com/… (No zero-days being used, just long-patched bugs in un-patched devices, some as old as 2016, none newer than 2021!)
- Related:
- Apple Issues Emergency XProtect Update for Sequoia and Tahoe Macs — www.macobserver.com/… (These happen silently & automatically, so no action required!)
- Microsoft now force upgrades unmanaged Windows 11 24H2 PCs — www.bleepingcomputer.com/… (Unmanaged means not under Mobile Device Management)
Worthy Warnings
- ⚠️ 🇺🇸 US Residents: US warns of Iranian hackers targeting critical infrastructure — www.bleepingcomputer.com/…
- Seriously consider keeping a few days of emergency supplies on hand 🙁
- ⚠️ Mac Users: New macOS stealer campaign uses Script Editor in ClickFix attack — www.bleepingcomputer.com/…
- ⚠️ Windows Users: Microsoft Warns of Whatsapp Delivered — thehackernews.com/…
- Don’t be socially engineered into running VBS files!
- A timely reminder that many Google ads remain malicious, and, that Mac users are being targeted: That Top Google Result for ‘Homebrew’ Could Infect Your Mac — appleinsider.com/…
- 🇺🇸 A reminder of why we need to be careful: FBI: Americans lost a record $21 billion to cybercrime last year — www.bleepingcomputer.com/…
- ⚠️ Perplexity Users: Perplexity’s “Incognito Mode” is a “sham,” lawsuit says — arstechnica.com/…
- This appears to have been verified technologically 🙁
- ℹ️ LinkedIn Users: there is a war-of-words between a company previously banned from LinkedIn for data scraping, and Microsoft, with the former claiming Microsoft is illegally spying on users, and Microsoft claiming they are protecting their services from abuse – court documents have been filed, but right now it’s a he-said-she-said more than anything else, so make up your own mind, or just monitor — www.bleepingcomputer.com/…
- Editorial by Bart: My gut feeling is there is probably a little truth on both sides, with the scanning definitely starting benignly, but I suspect some managers somewhere saw the power of the technique and instructed more plugins be monitored for, which is legal in the US where there are no privacy protections, but illegal in the EU.
Notable News
- 🇺🇸 US jury orders Meta to pay $375 million over child safety failures — cyberinsider.com/…
- Insightful Analysis: Meta’s Moment of Reckoning — om.co/… (“But here is where the parallel gets uncomfortable. Tobacco did not go away. It became Juul.” — Om Malik)
- 🇺🇸🧯 Court documents have shown that when presented with appropriate court orders, Apple will map anonymised Hide my Email addresses to Apple IDs — cyberinsider.com/…
- Editorial by Bart: This seems to have surprised some, but I can’t understand why — Apple have always, and will always, comply with court orders.
- It is utterly impossible for Apple not to know which users match to which address, otherwise, there would be no way for the email to arrive in the right inbox!
- Hide My Email is a tool for protecting you from app owners and website owners, nothing less, but also nothing more.
- 🇺🇸 FBI retrieved deleted Signal messages from iPhone notification database — cyberinsider.com/…
- Only possible because the FBI had full access to the phone
- Not a breach of Signal, literally read the notifications out of the OS, which needs to know them to show them!
- Editorial by Bart: Again, nothing shocking or scandalous here, this is just normal OS forensics!
- 🇬🇧 Apple Now Requires Age Verification in the UK with iOS 26.4 Update — www.macobserver.com/…
- Apple Age Verification is Failing for some: Here is What to Try — www.macobserver.com/…
- 🇸🇬 🇰🇷 Also rolled out in Singapore & South Korea — www.macobserver.com/…
- Microsoft’s rollout of tighter security for code signing Windows drivers has hit an unexpected snag, with some major open-source projects un-intentionally losing their keys, most notably WireGuard & VeraCrypt — www.bleepingcomputer.com/…
- Until this is resolved, the developers can’t release any updates, so it needs to be fixed before any critical vulnerabilities are found.
- A quick resolution looks likely with Microsoft appearing to respond constructively — “We’re taking this as an opportunity to review how we communicate changes like this and make sure we’re doing it better”
- Editorial by Bart: I see no sign of malice, and the intentions behind the change are definitely for the good of Windows security (compromised code signing keys are used to digitally sign a lot of malware these days)
- RowHammer attacks migrate from RAM to graphics memory, and there is a genuinely dangerous proof of concept — www.bleepingcomputer.com/…
- The specific attack can probably be fixed with a driver update from NVIDIA, and there is a work-around that cloud providers can use for now
- As with all RowHammer-like attacks, the real risk is on shared systems, not single-user systems like home systems
- An interesting side-effect of Apple’s unified memory architecture is that Macs don’t have to worry about this attack, since there is no graphics memory (and Apple are addressing regular RowHammer like the rest of the industry is).
- Longer-term, chip makers will need to revise their hardware to take account of this new technique
- Anthopic’s latest Mythos model is apparently so good at finding vulnerabilities that they are giving major tech companies advanced access so they can fix bugs before the model is released publicly — www.macobserver.com/… (Editorial by Bart: seems to be both good marketing and a genuine reflection of the model’s power)
- More major vendors are transparently submitting their services to audits:
- Independent audit confirms Cloudflare’s 1.1.1.1 resolver privacy claims — cyberinsider.com/…
- Malwarebytes VPNs audit uncovers critical flaws, fixes underway — cyberinsider.com/…
- “Malwarebytes has completed the first independent security audit of its Privacy VPN infrastructure, revealing a generally strong security posture alongside critical vulnerabilities that are fixed or in the process of remediation.”
- This was an extremely harsh audit — the starting assumption was that attackers were already in the network!
- None of the bugs still being worked on are show-stoppers that users need to worry about in the short-term
- WhatsApp ‘Private Inference’ pre-launch audit uncovered critical flaws — cyberinsider.com/… (and the flaws were fixed before launch!)
- Some nice product updates:
- Chrome rolls out hardware-bound session protection to combat infostealer malware — cyberinsider.com/…
- Windows-only for now
- An excellent protection against session hijacking — excellent use of TPMs (Windows Trusted Platform Module)
- Nice new features for Google enterprise users:
- Google rolls out Gmail end-to-end encryption on mobile devices — www.bleepingcomputer.com/…
- Google Drive ransomware detection now on by default for paying users — www.bleepingcomputer.com/…
- Proton unveils privacy-focused video conferencing service Meet — cyberinsider.com/…
- Have-I-Been-Pwned have announced major new features and simplifications of their paid plans, mostly for enterprise users, but one new feature is very welcome to home users — passkey support on the control panel — www.troyhunt.com/…🎉
Excellent Explainers
Palate Cleansers
- From Bart: 🎦 NASA Astronomy Picture of the Day for 6 April 2026: The Path of Artemis II — apod.nasa.gov/…
- The ultimate example of ‘skating to where the puck is going to be’!
- From Allison
- Gives Bart even more appreciation for the amazing human computers from the Hidden Figures movie (Find out more — en.wikipedia.org/…)
- 📊 Related: Allister Jenks shared this very apt cartoon with the star of Hidden Figures as the protagonist: @[email protected] on Mastodon: “#JoyScrolling #ArtemisII #HiddenFigures #Celebrat…”
- From Bart:
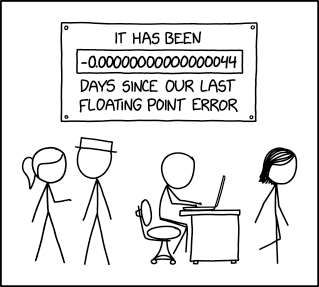
- 📊 XKCD 3228: Day Counter
- 🎧 The Sci-Fi & fantasy podcast Imaginary Worlds celebrated 300 episodes, and asked fans to support the show by sharing with friends – if the tag line “how we create them & why we suspend our disbelief” sounds intriguing, you’ll love this show — www.imaginaryworldspodcast.org/…
- 📊 XKCD 3228: Day Counter
Legend
When the textual description of a link is part of the link, it is the title of the page being linked to, when the text describing a link is not part of the link, it is a description written by Bart.
| Emoji | Meaning |
|---|---|
| 🎧 | A link to audio content, probably a podcast. |
| ❗ | A call to action. |
| flag | The story is particularly relevant to people living in a specific country, or, the organisation the story is about is affiliated with the government of a specific country. |
| 📊 | A link to graphical content, probably a chart, graph, or diagram. |
| 🧯 | A story that has been over-hyped in the media, or, “no need to light your hair on fire” 🙂 |
| 💵 | A link to an article behind a paywall. |
| 📌 | A pinned story, i.e. one to keep an eye on that’s likely to develop into something significant in the future. |
| 🎩 | A tip of the hat to thank a member of the community for bringing the story to our attention. |
| 🎦 | A link to video content. |

