Followups
- Instapaper comes back to the EU at last — www.macobserver.com/…
- Facebook is refusing to comply with a GDPR data request, so a complaint has been lodged with the Irish Data Protection Commissioner (DPR). The DPR has opened an investigation, but has said the case is likely to get escalated from Ireland to the European Data Protection Board. This will be a really important test case to watch — nakedsecurity.sophos.com/…
Security Medium — 🇺🇸 Forced Smartphone Decryption Breaches 5th Amendment to US Constitution
The US Appeals Court in Indiana (only level below the US Supreme Court) has ruled that forcing a user to decrypt their encrypted smartphone violates the 5th amendment to the US constitution (self incrimination). IMO the ruling is noteworthy for two reasons.
Firstly, the ruling recognises that a smartphone is effectively an extension of our brain, and that makes it very special indeed:
A modern smartphone, with its central purpose of connecting its owner to the Internet and its ability to store and share incredible amounts of information in ‘the Cloud’ of online storage, is truly as close as modern technology allows us to come to a device that contains all of its owner’s conscious thoughts, and many of his or her unconscious thoughts, as well. So, when the State seeks to compel a person to unlock a smartphone so that it may search the phone without limitations, the privacy implications are enormous and, arguably, unique.
Secondly, the ruling lays down a set of legal tests it recommends courts apply ‘for resolving decryption requests from law enforcement authorities’. The Indiana Lawyer summarised this structure as follows:
- Requiring the decryption of data should be recognized as data recreation and, thus, strictly limited.
- Law enforcement will have legitimate need of encrypted data in some instances.
- Law enforcement requests that are identified as bona fide emergencies should be supported by “a warrant that describes the other imminent crime(s) suspected and the relevant information sought through a warrant.”
- Law enforcement should be required to seek digital data through third parties in non-emergency situations.
- Fourth Amendment exceptions and state analogues should be inapplicable or strictly limited in “the search and seizure of digital data stored on devices owned or controlled by that defendant, or from ‘Cloud’ subscriptions that defendant owns or uses.”
Finally, I want to draw attention to the word I bolded in the opening paragraph – encrypted. I’m not a lawyer, but from my reading of the ruling it seems clear it only applies to encrypted phones:
We consider [the plaintif]’s act of unlocking, and therefore decrypting the contents of her phone, to be testimonial not simply because the passcode is akin to the combination to a wall safe as discussed in Doe. We also consider it testimonial because her act of unlocking, and thereby decrypting, her phone effectively recreates the files sought by the State.
So, if you’re not encrypting your phone yet, here’s yet another reason to do it!
Links:
- Naked Security’s excellent summary of the ruling — nakedsecurity.sophos.com/…
- A summary of the ruling from The Indiana Lawyer — www.theindianalawyer.com/…
Notable Security Updates
- Adobe released a critical out-of-band patch for the Creative Cloud desktop app — www.us-cert.gov/…
Notable News
- Apple have removed the popular app Adware Doctor from the Mac App Store after it was found to be sending users browser history and other data to servers in China. It seems Apple were very slow off the mark though, the app and its developer had a longer history of sketchy behaviour — daringfireball.net/…
- In addition to recently introducing 2FA, Instagram have announced two new features to help users distinguish real content from fake content – About this Account will show information about a user’s activity, and there will be a process for getting Verified badges — nakedsecurity.sophos.com/…
- A previously secret data-sharing deal between Google and MasterCard has been revealed. This allows Google to link real-world purchases to ad views online. Neither company informed their customers/users, and while Google point out that user can technically opt out, the setting is obscure and not clearly labelled (Editorial by Bart while Google can say they technically allow users to opt out, the setting is so well obfuscated it may as well not exist, and besides, since they didn’t announce this deal, how were users supposed to know there was even something they might want to opt out of? IMO this just stinks to high-heaven) — www.bloomberg.com/… & nakedsecurity.sophos.com/…
- Mozilla will move to disabling ad-tracking by default in FireFox by putting measures in place to block cross-site tracking and browser fingerprinting — nakedsecurity.sophos.com/…
- Mozilla’s post announcing and explaining their new approach — blog.mozilla.org/…
- Related: Firefox finally casts Windows XP users adrift — nakedsecurity.sophos.com/…
- The latest Chrome update makes it even more cumbersome to run Flash, it really is nearing its long-over-due demise! — nakedsecurity.sophos.com/…
- Google cracks down on tech support scams by forcing advertisers wishing to advertise such services to go through advanced validation before their ad will be accepted — nakedsecurity.sophos.com/…
- Windows 10 support extended again: September releases now get 30 months — arstechnica.com
Suggested Reading
- PSAs, Tips & Advice
- ⭐️ Security researchers warn of the danger of Safari’s default setting which opens ‘safe’ files automatically on download – TL;DR, disable the setting! (Preferences > General > Open “safe” files after downloading) — www.loopinsight.com/…
- ⭐️ FYI: As of September 2018, Microsoft Office 365 Updates Will Require 10.12 Sierra — tidbits.com/…
- ⭐️ Fail safe vs. fail secure: What everyone gets wrong about backups — www.imore.com/…
- ⭐️ 159: iPhone SECURITY TIPS You Need to Know! — Vector with Rene Ritchie — Overcast — overcast.fm/…
- How to create and add a child account to Family Sharing — www.imore.com/…
- 🇺🇸 PSA: Robo Call Asks AT&T PIN and Social Security Number — www.macobserver.com/…
- What To Actually Evaluate When Choosing Privacy Applications for Mac — www.macobserver.com/…
- How to Tell If an Online Article is Real, Fake or a Scam — www.intego.com/…
- Notable Breaches & Privacy Violations
- ⭐️ A very damaging hack of the British Airways website has led to the compromise of tens of thousands of credit cards, including the 3-digit verification codes — www.telegraph.co.uk/…
- ⭐️ 🇺🇸 Hackers Steal T-Mobile Customer Data, Including Passwords — tidbits.com/…
- ⭐️ 🇺🇸 Charter Security Flaw Just Exposed Customer Data for Millions — www.macobserver.com/…
- ⭐️ Air Canada resets 1.7 million accounts after app breach — nakedsecurity.sophos.com/…
- ⭐️ 🇺🇸 Social Security numbers exposed on US government transparency site (foia.gov) — nakedsecurity.sophos.com/…
- Hacked stalking app (TruthSpy) reveals victims’ photos, texts and location info — nakedsecurity.sophos.com/…
- For 2nd Time in 3 Years, Mobile Spyware Maker mSpy Leaks Millions of Sensitive Records — krebsonsecurity.com/… & Mobile spyware maker mSpy leaks millions of records – AGAIN — nakedsecurity.sophos.com/…
- A bug in the popular Magento eCommerce platform has allows a credit-card-stealing malware campaign to proliferate — nakedsecurity.sophos.com/…
- Chinese hotel chain’s customer data on Dark Web – 500M records for $50K — nakedsecurity.sophos.com/…
- 🇺🇸 Fiserv Flaw Exposed Customer Data at Hundreds of Banks — krebsonsecurity.com/…
- News
- 🇺🇸 Proposed US law would require President to act against overseas hackers — nakedsecurity.sophos.com/…
- Microsoft obliquely acknowledges Windows 0-day bug published on Twitter — arstechnica.com
- Five Eyes Countries Want to Avoid Public Encryption Debate — www.macobserver.com/…
- Middle East Espionage Involves Hacking Macs — www.macobserver.com/…
- 🇬🇧 How refusing to give police your Facebook password can lead to prison — nakedsecurity.sophos.com/…
- Security Researchers have found flaws in two smart access control systems – iStar Ultra & IP-ACM Ethernet Door Module — nakedsecurity.sophos.com/…
- Thousands of unsecured 3D printers discovered online — nakedsecurity.sophos.com/…
- Apple Will Create a Global Law Enforcement Web Portal — www.macobserver.com/…
- Google releases free AI tool to stamp out child sexual abuse material — nakedsecurity.sophos.com/…
- Ungagged Google warns users about FBI accessing their accounts — nakedsecurity.sophos.com/…
- Microsoft Authenticator app launches for Apple Watch in public preview — www.imore.com/…
- Opinion & Analysis
- ⭐️ Why Yahoo scanning user email is no cause for panic — nakedsecurity.sophos.com/…
- ⭐️ A Honeypot Guide: Why Researchers Use Honeypots for Malware Analysis — www.intego.com/…
- ⭐️ What it’s like to live under the Google Advanced Protection Program — www.imore.com/…
- ⭐️ Browser Extensions: Are They Worth the Risk? — krebsonsecurity.com/…](https://krebsonsecurity.com/2018/09/browser-extensions-are-they-worth-the-risk/)
- Propellor Beanie Territory
- ⭐️ Can ‘sonar’ sniff out your Android’s lock code? — nakedsecurity.sophos.com/…
- Security researchers demo a proof-of-concept attack that reads the content of a screen by listening to the sounds it emits — nakedsecurity.sophos.com/…
- How one man could have pwned all your PHP programs – nakedsecurity.sophos.com/…
- System Administrators: Prepare Your Institution for iOS 12 and macOS Mojave — www.macobserver.com/…
- US Cert warns of the dangers of combing dynamic DNS with the WPAD protocol — www.kb.cert.org/…
Palate Cleansers
- A wonderful example of how Apple sweats the details – the emoji of a lock will not show in the Safari title bar because it could make an insecure page seem secure — www.loopinsight.com/…
- With this new product, Lego will teach your kid how to code — www.imore.com/…
- Funny, but also disturbing:
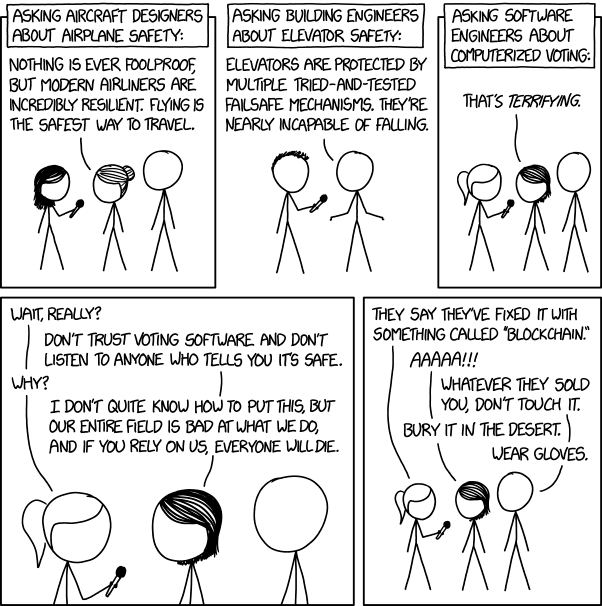 xkcd.com/…
xkcd.com/…


I saved this post quite a while ago and just got around to reading it. I have to disagree with your last premise about unlocking a phone vs. decrypting said phone. My view is that the very nature of unlocking is essentially the same as giving testimony. Again, the fifth amendment may apply here. Hard to say without seeing more of the legal briefings.