Security Medium 1 — Human Review of Voice Assistant Recordings
The Guardian newspaper started what turned out to be a far-ranging controversy be reporting that when Apple said they kept anonymised Siri recordings for analysis, that analysis included grading by human beings. Specifically, by outside contractors.
One of the types of problematic interaction the reviewers were helping Apple deal with was accidental triggers. In other words, they were reviewing snippets of content from those times when Siri would just randomly wake up when you didn’t intentionally trigger the feature by saying the wake-word.
Contractors described hearing deeply personal information while reviewing snippets including medical discussions, legal advice, and even possible criminal conspiracies in the making.
Technically speaking Apple did not violate their privacy policy or public statements, but we all seem to have assumed that the analysis we knew was happening was being done by computers, not humans, and we definitely didn’t assume it was being done by humans who don’t work directly for Apple.
The story soon grew legs, and it became clear this is not just an Apple thing, but that all the major voice assistants use humans (we’d known Amazon did this before, and that there were horrible abuses going on with those recordings). It also seems this is bigger than just voice assistants, Skype’s real-time translation service also apparently relies on human review of clips, as may Cortana.
The end-result is that all the major voice assistants (Apple, Google & Amazon) have suspended their human review programs. Apple have said that they will add a setting to allow users to use Siri but opt out of human review. (I’ve found no further details on the situation with Skype/Cortana so I presume human review continues at Microsoft.)
In the end, we’ve ended up with a better future for Siri, and I’m sure Google and Amazon will follow suit before they un-suspend their review services too.
Links
- The original report: Apple contractors ‘regularly hear confidential details’ on Siri recordings — www.theguardian.com/…
- Accidental Siri recordings may reveal your private information — www.imore.com/…
- Siri records fights, doctor’s appointments, and sex (and contractors hear it) — arstechnica.com
- Listening in: Humans hear the private info Siri accidentally records – Naked Security — nakedsecurity.sophos.com/…
- Germany Orders Google to Stop Human Review of Voice Recordings — www.macobserver.com/…
- Apple suspends Siri voice grading, future update will allow users to choose — www.imore.com/…
- Apple and Google temporarily stop listening to Siri and OK Google queries — arstechnica.com
- Amazon will let you opt out of human review of Alexa recordings — www.theverge.com/…
- Your Skype Translator calls may be heard by humans — nakedsecurity.sophos.com/…
- How to delete your data from Siri on your iPhone, iPad, and Mac — www.imore.com/…
- 🎧 Vector with Rene Ritchie: Why People Are Freaking Out Over Siri Privacy — overcast.fm/…
Security Medium 2 — Beware of Privacy-Invading Browser Plugins
A major report by the Washington Post in conjunction with security researchers have shone a light on a long-standing avenue of abuse — browser plugins.
JavaScript within web pages is sandboxed. It can’t interact with the underlying OS, its interactions with the browser are extremely limited, and it can’t access information in tabs from other websites that are open at the same time.
Browser plugins are different. They are still sandboxed very heavily, but in a much larger playground! They can have some interaction with the underlying OS, though that’s very tightly controlled. What’s much more important to understand is that they have a lot of free rein within the browser. The whole point of a plugin is to add new functionality to the browser, so this is not just sensible, it’s essential. This is absolutely a feature, and definitely not a bug!
Browser plugins can see all the tabs you have open, and can see into them and interact with the HTML, CSS & JavaScript within them. Browser plugins can also make their own network connections, so they can communicate directly with servers on the internet. Again, if plugins couldn’t do this they wouldn’t be able to do their thing! Imagine if the 1Password plugin couldn’t use a local socket to talk to the master 1Password app to access usernames and passwords, and if it couldn’t interact with web pages to write the usernames and passwords into the text boxes. What use would it be? What use would any plugin be if it couldn’t interact with the contents of your tabs?
1Password is using the access plugins have as users expect. It does what it promises to do, and nothing more. There is of course nothing stopping less scrupulous developers adding code to their plugins that does things users are not expecting!
What this means is that installing a plugin is an act of trust. You are trusting that the developer who wrote the plugin has your best interests at heart, and that they’re being completely honest in the plugin’s description.
Unsurprisingly, it turns out many are not 🙁
This is yet another follow the money story. The existence of free plugins from for-profit companies should raise red flags in all our minds. How are they making money from these plugins?
Well, one of the ways developers can monetise their plugins is to collect and sell browsing data. Plugins can see every URL you go to, how long you stay there, and how actively you interact with each page. They even know what buttons and links you pushed while on the page. This is a positive gold-mine for the ad industry, so of course there is a market for this information 🙁
What the Washington Post found is that this type of privacy abuse is absolutely rampant, affecting millions of users every day, and that this kind of bad behaviour is not limited to obscure developers, but affects many popular free plugins.
The bottom line is very simple — every time you install a plugin, you are trusting the author, so be conscious of that, and only install plugins you have a good reason to trust. Perhaps they are by a developer you trust, or, perhaps they have been recommended by a person or site you trust.
The days of just installing any plugin on a whim are over, or at least they should be!
Links
- The original Washington Post report: I found your data. It’s for sale. — www.washingtonpost.com/…
- Browser plug-ins peddled personal data from over 4m browsers — nakedsecurity.sophos.com/…
Security Medium 3 — 🇺🇸 🇨🇦 The Capital One Breach
Capital One announced that their systems have been hacked and that attackers accessed customer data and data on people who merely applied for credit cards from Capital One.
According to their official FAQ, 100M Americans and 6M Canadians are affected. The data accessed does not include credit card details, though in about 1% of cases it included Social Security Numbers/Social Insurance Numbers (about 140K in the US and 1M in Canada). In general the data included “names, addresses, zip codes/postal codes, phone numbers, email addresses, dates of birth, and self-reported income”. For customers the data also included “credit scores, credit limits, balances, payment history [&] contact information” as well as “fragments of transaction data from a total of 23 days during 2016, 2017 and 2018”, and even “about 80,000 linked bank account numbers”.
Links
- The Official US FAQ — www.capitalone.com/…
- The Official Canadian FAQ — www.capitalone.ca/…
- Capital One Data Theft Impacts 106M People — krebsonsecurity.com/…
- Capital One breach – 100 million users’ data stolen — nakedsecurity.sophos.com/…
- Capital One Hack: What We Know and What You Can Do — www.macobserver.com/…
- Capital One breach also hit other major companies, say researchers — techcrunch.com/…
- GitHub ‘encourages’ hacking, says lawsuit following Capital One breach – Naked Security — nakedsecurity.sophos.com/…
- What We Can Learn from the Capital One Hack — krebsonsecurity.com/…
Notable Security Updates
- Apple Releases macOS Mojave 10.14.6 Supplemental Update for Sleep Issue — www.macobserver.com/…
- Google have released the August Android patches, and they include particularly important fixes for a collection of bugs named QualPwn which affect Android Devices with Qualcomm SOCs (mostly higher-end phones like Samsung Galaxies and Google Pixels) — nakedsecurity.sophos.com/…
- FileZilla have release a critical security update for their open source SFTP client. Interestingly this patch fixes bugs found through the EU’s bug bounty program for important open source products — nakedsecurity.sophos.com/…
- NVIDIA patches high-severity bugs in Windows GPUs and SHIELD – Naked Security — nakedsecurity.sophos.com/…
Notable News
- It’s important that you apply the recent security updates for iOS because we now know they patched 6 ‘interactionless’ remote code execution bugs which could be triggered via iMessage. One of the six bugs is only partially patched, so security researchers are keeping the details of that bug back for now, but they’re published the details on the other five — www.zdnet.com/…, www.imore.com/…, nakedsecurity.sophos.com/… & nakedsecurity.sophos.com/…
- Security researchers have published details of three bugs in WhatsApp that allow manipulation and unexpected publication of private messages. All three bugs were responsibly disclosed to Facebook a year ago, but only a bug that allowed users to be tricked into sending a public message when they thought they were sending a private message has been fixed. The other two bugs which allow attackers to alter the content of quoted messages and to the reword other users responses, making it look like users said things they did not within group chats, remain un-patched today. In other words, you can’t trust that anything in a WhatsApp group conversation was actually said by the apparent author — thenextweb.com/…
- Security researchers have found that many popular robocall blocking apps like TrapCall, Truecaller & Hiya are monetising themselves by selling users’ private information (Editorial by Bart: yet another example of why it’s important to follow the money, though in some cases it’s even worse with companies charging a fee and selling users data!) — techcrunch.com/…
- 🧯Security researchers have found a way to bypass the liveness detection security enhancement in Apple’s FaceID. In its default configuration, FaceID will not unlock a devices until it both recognises the face, and their gaze detection algorithms report that the user is looking at the device. Researchers have found that it’s possible to use black and white tape and a pair of glasses to bypass the second of these conditions (and only the second). This means the attack only works if you have a difficult to make 3D model of the person’s head, or, the unconscious person themselves and their phone under your control at the same time. This is an interesting development in the eternal security can-and-mouse game, but absolutely no need for panic! This simply isn’t a realistic real-world attack — www.imore.com/… & threatpost.com/…
- 🧯Security researchers have found that Apple’s AirDrop and password sharing features can leak some identifiers including MAC addresses and even cell phone numbers via Bluetooth LE packets. Apple have done their best to obscure the information by hashing it, but with enough time an effort security researchers have proven they can break the hashes and recover the information. Because the data is leaked over Bluetooth LE, and only while using the features, the danger is very short-lived and localised, but it’s something to be aware of. Perhaps best not to use these features in public spaces! — arstechnica.com/… & www.imore.com/…
- At this year’s BlackHat security conference Apple launched some welcome new initiatives to help security researchers discover bugs, and encourage them to disclose them responsibly: (www.imore.com/… & 9to5mac.com/…)
- Apple will supply security researchers with special iPhones with extra debug tools including things like root shell and SSH access.
- Apple have expanded their bug bounty program to cover all their OSes, and, increased the maximum payout to $1M for a ‘zero-click kernel code execution with persistence’.
- 🇪🇺 The ECJ (Court of Justice of the European Union) has ruled that websites that embed Facebook Like buttons are joint data controller with Facebook under the GDPR. This means they are responsible for getting the appropriate user consents etc under the GDPR — www.reuters.com/…
Suggested Reading
- PSAs, Tips & Advice
- ⭐️ Even if you have 2FA/MFA enabled, never use a weak password on a banking site. It turns out many banks have by-passes for 2FA/MFA to facilitate financial apps and services like Mint, Plaid, Yodlee & YNAB — krebsonsecurity.com/…
- ⭐️If you have a NAS exposed to the internet, be sure to set a strong password on it: Ransomware crooks hit Synology NAS devices with brute-force password attacks — www.zdnet.com/…
- Everything you need to know about iCloud Keychain — www.imore.com/…
- Don’t let the crooks ‘borrow’ your home router as a hacking server – Naked Security — nakedsecurity.sophos.com/…
- Notable Breaches & Privacy Violations
- ⭐️ 🇺🇸 It turns out that due to some nasty fine-print you probably want to opt for credit monitoring rather than cash if you’re affected by the Equifax breach: Equifax Cash Settlement Backtracking Leaves a Bad Taste — tidbits.com/…
- ⭐️ 🇬🇧 UK internet-only bank Monzo accidentally logged PINs, they are contacting affected customers and asking everyone to update their app — www.macobserver.com/…, www.macobserver.com/… & nakedsecurity.sophos.com/…
- ⭐️ Amazon Requires Police to Shill Surveillance Cameras in Secret Agreement — www.vice.com/… & A deal with Amazon lets local police request Ring footage directly from home owners — www.imore.com/…
- ⭐️ Two Twitter bugs resulted in some users data being in appropriately shared: (nakedsecurity.sophos.com/…)
- Clicking on some ads may have resulted in some information about your interaction including your OS, the app you were using, and your country code, being shared with partners like Google’s Double-Click ad network. The bug was introduced in March 2018 and Twitter don’t know how many users were affected.
- Device-specific ads were shown to users who had explicitly opted out of that (like me!). This bug was introduced in September 2018.
- 🇺🇸 LinkedIn Learning policy violates library patrons’ privacy — calmatters.org/…
- 4 million Club Penguin Rewritten accounts exposed in breach – Naked Security — nakedsecurity.sophos.com/…
- Notable IoT Vulnerabilities
- News
- ⭐️ 🔥 “Urgent/11” is the catchy name given to 11 critical vulnerabilities in an OS you’ve probably never heard of, but which is powering a staggering amount of devices in our every day lives (including AirPort routers, hence them getting a security update recently). The OS is VxWorks, which is one of the most widely used Real Time OSes (RTOSes) in use today. Literally millions if not billions of IoT devices will need security updates, but many won’t get them. This bug will be with us for a very long time, and other than applying patches as and when they become available, there’s not much we can do to protect ourselves. Since this OS is embedded deep within devices, we can’t even tell if our devices are vulnerable 🙁 — nakedsecurity.sophos.com/…
- ⭐️ WannaCry hero avoids prison — nakedsecurity.sophos.com/…
- ⭐️ 🇺🇸 Russia targeted all 50 states in 2016 election, Senate report says — nakedsecurity.sophos.com/…
- ⭐️ Yet more evidence of why you should only install apps you have a reason to trust: Google Play hosted 205 harmful apps with over 32M installs last month alone — thenextweb.com/…
- ⭐️ Recent takeovers of the Telegram accounts of high-profile Brazilian politicians highlight the importance of setting a password on your voicemail. Services that rely on cellphone numbers for authentication are only as secure as access to the information sent to that number, including access to that number’s voicemail box — nakedsecurity.sophos.com/…
- Cloudflare Ends 8Chan Service in Wake of Recent U.S. Shootings — www.macobserver.com/…
- Apple joins Google and Facebook in Data Transfer Project — www.imore.com/…
- Three quarters of gamers suffer hate and harassment online — nakedsecurity.sophos.com/…
- 🇺🇸 Hackers exploit SMS gateways to text millions of US numbers – Naked Security — nakedsecurity.sophos.com/…
- Developments in the on-going war on privacy:
- Five Eyes nations demand access to encrypted messaging — nakedsecurity.sophos.com/…
- Here We Go Again: GCHQ’s Ghost User Proposal to Circumvent Encryption — tidbits.com/…
- ⭐️ A four-part series from the ACLU detailing their objections to the UK GCHQ’s so-called ‘ghost user’ proposal (recommended by NosillaCastaway @gaudior on Twitter) — www.aclu.org/…
- Opinion & Analysis
- ⭐️ What Apple’s T2 chip does in your new MacBook Air or MacBook Pro — appleinsider.com/…
- ⭐️ The Unsexy Threat to Election Security — krebsonsecurity.com/…
- Firewalls, phoning home and whitelists — eclecticlight.co/…
- Cyberattacks on connected cars could gridlock entire cities – Naked Security — nakedsecurity.sophos.com/…
- 🇺🇸 America’s DIY Phone Farmers — www.vice.com/…
- Propellor Beanie Territory
- ⭐️ NIST Publishes Multi-factor Authentication Practice Guide — www.us-cert.gov/… (some light bed-time reading for Allison 😉)
- iOS 13 is changing VoIP APIs preventing apps like WhatsApp from collecting background data — www.imore.com/… & iOS 13 privacy feature will force total overhaul for Facebook apps — arstechnica.com
- iOS 13’s new Bluetooth privacy feature is important—but confusing — www.fastcompany.com/…
- Microsoft puts another nail in VBScript coffin – Naked Security — nakedsecurity.sophos.com/…
- Baldr malware unpicked with a little help from crooks’ bad opsec – Naked Security — nakedsecurity.sophos.com/…
Palate Cleansers
- Celebrating National Sysadmin Appreciation Day:
- (nerdily humours and yet interesting) — Sysadmins need to know – how DO you pronounce “sudo”? – Naked Security — nakedsecurity.sophos.com/…
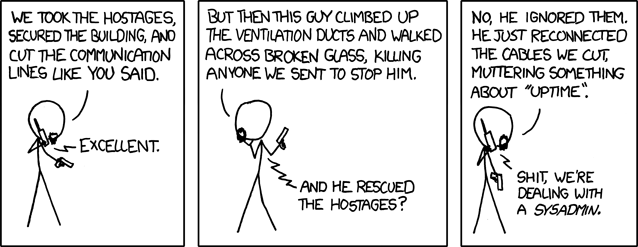 xkcd.com/705
xkcd.com/705
Note: When the textual description of a link is part of the link it is the title of the page being linked to, when the text describing a link is not part of the link it is a description written by Bart.

