Feedback & Followups
- In the previous instalment we joined in the mockery of a Chinese railroad company that relied on Flash for their operations. Listener Tom Merit got in touch with a follow-up article which casts some doubt on the details of the Apple Daily report we linked to — it seems the problem did not stop them dispatching trains, and the fix was not a pirated version of Flash, but an older version without the self-deactivating code. They do still deserve quite a bit of mockery regardless IMO — arstechnica.com/…
- In the previous instalment we mentioned that based on Apple’s infamous FaceTime bug a security researcher had found similar bugs in other apps and got those responsibly fixed. We’ve since learned that the same research has also revealed how Apple responded in the long-term – they completely re-architected FaceTime to harden it dramatically with a new kind of extra secure sandboxing arrangement they’ve codenamed BlastDoor (Editorial by Bart: I’m really impressed with what Apple have done, very clever!) — www.zdnet.com/… & tidbits.com/…
- 🎦 Apple have released the video of Tim Cook’s speech to the CPDP21 EU data protection conference mentioned in the previous instalment — youtu.be/…
- The fallout from Apple’s up-coming App Tracking Transparency feature continues:
- A study by the Harvard Business Review has found that the numbers Facebook used in their recent anti-anti-tracking ads were false — www.imore.com/…
- The HBR Article — hbr.org/…
- A study by the Harvard Business Review has found that the numbers Facebook used in their recent anti-anti-tracking ads were false — www.imore.com/…
- Snapchat also warns investors that requiring informed consent could cost it money — www.imore.com/…
- Twitter seems more optimistic, warning its investors of only a ‘modest impact’ — www.imore.com/…
- WhatsApp have launched a second attempt to roll out their controversial updated privacy policy — www.imore.com/…
- New reporting suggests it wasn’t just the Russians making use of the SolarWinds vulnerability, Chinese government hackers may have done so too — www.msn.com/… (via listener Lynda)
- 🦠 COVID App News (not done on of these in a while!)
- Apple have released updated app store rules requiring ‘Health pass’ apps (apps for tracking things like vaccination status and recent test results) to be submitted to the store in conjunction with an approved health authority — www.imore.com/…
- 🇬🇧 Data from the UK’s storied COVID-19 app shows how effective these apps can be when implemented properly — analysis of the notifications sent by the app show it instructed 1.7m people they should isolate, preventing an estimated 600k infections — www.imore.com/…
- 🇺🇸 Utah re-Launches its COVID-19 Exposure Notification System, this time based on the Apple/Google API — www.macobserver.com/…
Deep Dive — Bloomberg Follows up on its Sensationalistic “The Big Hack” Story from 2018 (Opinion)
This entire segment is opinion, but here’s the link to the piece if you’d like to read it yourself: The Long Hack: How China Exploited a U.S. Tech Supplier — www.bloomberg.com/…
What made the original story such big news is the report that there were spying chips inserted into an entire line of popular products used in data centres around the world by massive cloud providers like Amazon and Apple. The authors hadn’t been able to find any actual chips, so they illustrated their piece with an artist’s impression of what one might look like, and the entire US security apparatus and the companies involved all issued strenuous denials of the story.
Back in 2018 when the authors were criticised for publishing such a big allegation without any actual evidence, they replied confidently that now the story was out it would just be a matter of time until the evidence flowed in as these chips started to be found all over the place. That never happened, and still hasn’t!
This new article never admits the old one was wrong. It never retracts the unfounded chip allegations, but it also doesn’t provide any new evidence to support the original claim. Instead, in a bait-and-switch maneuver, the article instead describes highly targeted malicious firmware attacks by nation-states against each other’s interests. That’s neither surprising nor news, and it wouldn’t have been either in 2018 either.
We know governments and their operatives are using highly targeted supply-chain attacks, and have known that for years. It’s nice to see an example of this described in detail, but it does not justify the original publication of the utterly unsupported and hyperbolic original piece back in 2018, nor does it justify Bloomberg’s continuing refusal to retract that sensationalistic nonsense.
I’m in complete agreement with Jon Gruber’s scathing criticism. This quote sums up my opinion nicely:
“It’s a 4,000-word exercise in journalistic sophistry. It creates the illusion of something being there, but there is nothing there. The only good purpose this report could serve is as source material for a class on critical thinking.”
❗ Action Alerts
- Chrome zero-day browser bug found – patch now! — nakedsecurity.sophos.com/… (rather old news at this stage, but if you’re the kind of person who almost never re-starts their browser, and you use Chrome, now would be a good time to do that so it can update itself!)
- Another Patch Tuesday has been and gone, with 56 bugs patched in Windows, including a zero-day being actively exploited in the wild — krebsonsecurity.com/…
- Two sets of Mac patches:
- Apple released patches for its Mac operating systems (macOS Big Sur 11.2, and Security Update 2021-001 for Catalina & Mojave) on February 1st, these did not fix the Baron Samedit Sudo bug we discussed last time — support.apple.com/…
- About a week later Apple released macOS 11.2.1, macOS Catalina 10.15.7, and Security Update 2021-002 for Mojave, and these do patch the Sudo bug — tidbits.com/… & tidbits.com/…
- GnuPG crypto library can be pwned during decryption – patch now! — nakedsecurity.sophos.com/…
- Telegram have patched a bug in their Mac app that stopped self-destructing messages from being properly deleted — thehackernews.com/…
- 📌 New malware Silver Sparrow found on 30,000 Macs has security pros stumped arstechnica.com/…
Worthy Warnings
- Romance scams at all-time high: here’s what you need to know — nakedsecurity.sophos.com/…
- 🇺🇸 Washington State Suffers Data Breach due to Contractor ‘Accellion’ — www.macobserver.com/…
Notable News
- Emotet takedown – Europol attacks “world’s most dangerous malware” — nakedsecurity.sophos.com/…
- Apple launches iCloud Passwords extension for Chrome on Windows — www.imore.com/…
- A security researcher made use of 35 large companies’ bug bounty programs (including Apple, Microsoft, PayPal, Spotify & Netflix) to legally demonstrate a new and dangerous kind of supply-chain hack. He looked for open-source code using package managers that referenced both public and private packages in their requirements, then created public malicious packages with the same names as the private packages — www.bleepingcomputer.com/… & nakedsecurity.sophos.com/…
- From Allison: Ford vehicles will run on Android Auto starting in 2023 — www.engadget.com/…
- Apple have updated their security & privacy explanation page: Apple Platform Security — support.apple.com/…
- Ring Security Cameras Adding End-to-End Encryption — tidbits.com/…
- 🇺🇸 An attack on the Oldsmar water treatment facility in Florida highlights the real-world dangers posed by cyber-attacks, and the vulnerability of so much critical infrastructure around the world — www.theverge.com/… & krebsonsecurity.com/…
- 🇮🇹 An Italian court has found that the parents of a young man killed in a traffic accident do have the right to get a copy of all recoverable data on his iCloud account — www.imore.com/…
Top Tips
- Topic-Adjacent: 10 Steps to Improve Your Computer Ergonomics – The Mac Security Blog — www.intego.com/…
Excellent Explainers
- A timely reminder that email tracking pixels have not gone away: Spy pixels in emails have become endemic — www.bbc.com/…
- One to bookmark and hope you never need to use or share with friends or family: Fallen victim to online fraud? Here’s what to do… — nakedsecurity.sophos.com/…
Interesting Insights
- A security researcher has released a proof-of-concept supercookie (un-removable tracker) based on browser favicons (the icons websites can publish to include in browser tabs). The good news is that the researcher is working with the browsers to help then resolve this issue — www.vice.com/…
- 🎧 Recode Daily: How private is Clubhouse? — overcast.fm/…
- From Listener George (I think): They Stormed the Capitol. Their Apps Tracked Them. — www.nytimes.com/…
- 🎧 A nice explainer on why we should be excited about Quantum Computers: TED Talks Daily — Matt Langione: The promise of quantum computers — overcast.fm/…
Palate Cleansers
- XKCD use Star Wars to explain mRNA vaccines: xkcd.com/…
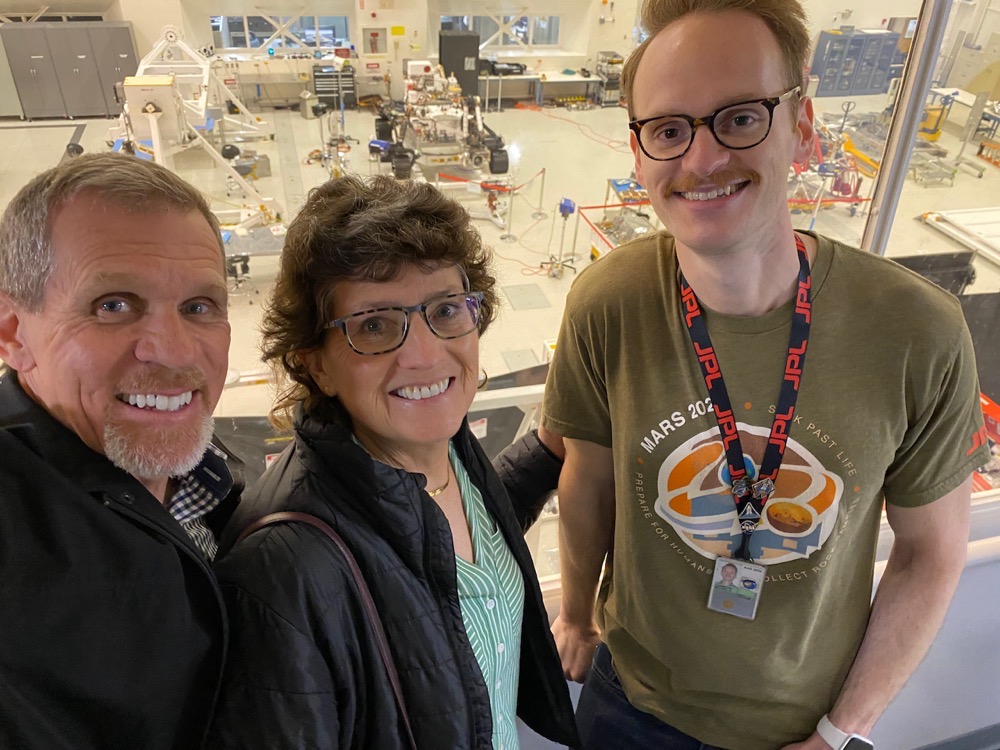
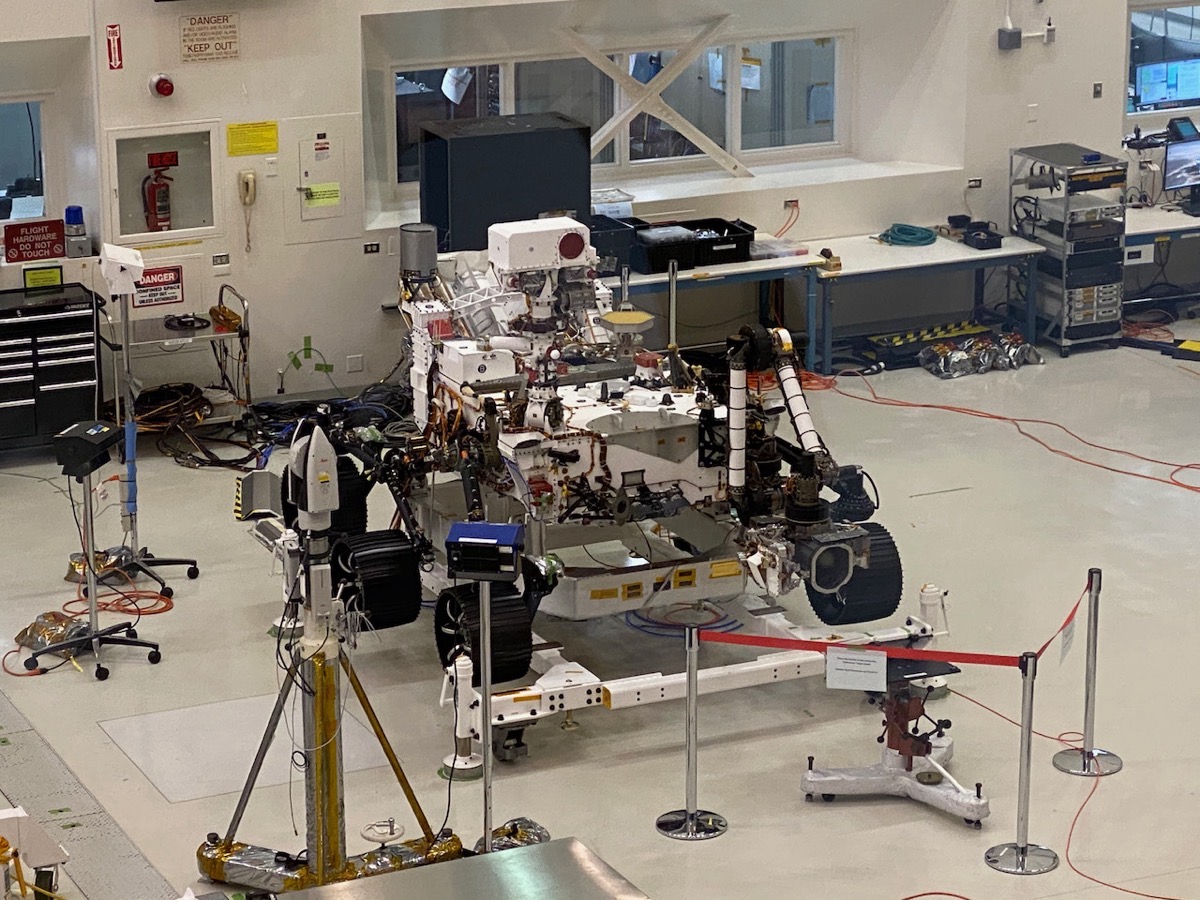
- NASA reminds us just how cool space engineering is, and just how good they are at — they’ve done it again, used another sky crane to land an even bigger rover on Mars, and this time, in a really hazardous terrain using AI to allow the craft pick its own landing site!
- A really cool photo of the rover dangling from the sky crane over the martian surface — apod.nasa.gov/…
- 🎦 A great video explaining how the sky crane plays its part in the seven minutes of terror between the top of the Martian atmosphere and a safe gentle touchdown on the red planet — apod.nasa.gov/…
- Northrup Grumman named a spaceship after Katherine Johnson, the black NASA mathematician whose handwritten calculations helped launch the first Americans into space (and highlighted in the movie Hidden Figures) www.npr.org/…
Legend
When the textual description of a link is part of the link it is the title of the page being linked to, when the text describing a link is not part of the link it is a description written by Bart.
| Emoji | Meaning |
|---|---|
| 🎧 | A link to audio content, probably a podcast. |
| ❗ | A call to action. |
| flag | The story is particularly relevant to people living in a specific country, or, the organisation the story is about is affiliated with the government of a specific country. |
| 📊 | A link to graphical content, probably a chart, graph, or diagram. |
| 🧯 | A story that has been over-hyped in the media, or, “no need to light your hair on fire” 🙂 |
| 💵 | A link to an article behind a paywall. |
| 📌 | A pinned story, i.e. one to keep an eye on that’s likely to develop into something significant in the future. |
| 🎩 | A tip of the hat to thank a member of the community for bringing the story to our attention. |

