Now that we’ve cleared the 1000 mark on the NosillaCast, I’d like to tell you about some changes coming to the podcasts. I promise you, they are all good. The problem(s) to be solved Of course, we have to start with the problem or problems to be solved. In order to explain the problem, I […]
Continue readingTag: Chit Chat Across the Pond
CCATP #636 – Adam Engst on 30 Years of TidBITS and other random topics
Adam Engst has been publishing TidBITS for 30 years so I asked him to come on the show to talk about that journey. While we technically had an agenda, this conversation wandered into all kinds of fun topics like why Adam still goes to the same dentist office even though the dentist left and why […]
Continue readingCCATP #622 — Bart Busschots on PBS 89 of X — Currency Converter Challenge
In this week’s installment of Programming By Stealth, Bart explains his new plan for both the content of PBS and the way the shownotes are created and presented to you. Bart has noticed that because we put a challenge solution and new content into the same show, the solution gets short-changed. That’s a shame because […]
Continue readingNC #627 12 Year Anniversary, 3 Chit Chats is Better Than 1, Akyumen Projector Smartphone, Cinamaker Multi-Cam Live Production, Security Bits
We have a huge show today. Steve’s put out two more video interviews from NAB in Las Vegas, I’ve got a pretty big announcement about Chit Chat Across the Pond, and we’ve got another giant Security Bits with Bart Busschots. I told him maybe when there’s such a big security news week we should call […]
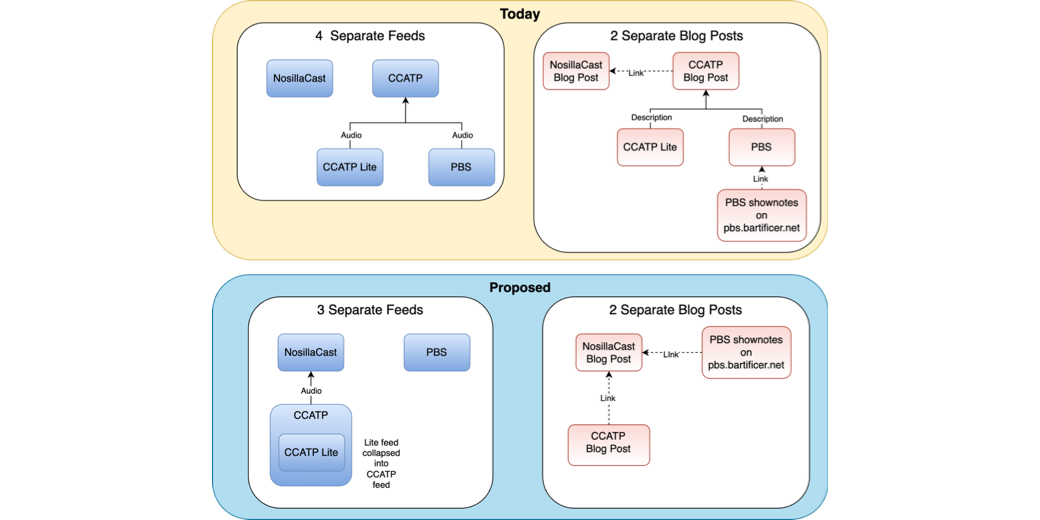
Continue readingThree Chit Chat Feeds are Better Than One
12 years ago, on May 13th, 2005, I decided to start the NosillaCast. Somewhere along the lines I met the wonderful Bart Busschots and he started to be a regular on the show, in a segment we affectionately called Chit Chat Across the Pond. Bart and I talked about photography and security and Macs and […]
Continue readingCCATP #418 Bart Busschots Programming By Stealth 5 of x (HTML Images & Links)
In this week’s episode of Chit Chat Across the Pond we have Bart Busschots with another installment of Programming by Stealth. He covers the syntax for images and links in HTML and the attributes you can apply and more importantly why you should apply them. He promises that with the first 5 episodes under our […]
Continue reading