Make sure you get to Macworld | iWorld in time to see me do my Tech Talk on Thursday March 27th! And early bird registration ends on 28 February so be sure to sign up early. Interview from New Media Expo with Nataša Dukanović about the .Me domain name. In Dumb Question Corner, Yadiel Sotomayor asks about key modifiers during boot up and I explain each of them as outlined in Apple knowledge base article HT1533 and tell you what problem they solve. In another “Dumb” question, Slau asks if there’s a way he can control a Mac remotely but actually be able to hear the other Mac’s audio, and I found the solution at bionoren.com. I do a review of PortraitPro from portraitprofessional.com which allows you to “improve” portraits like the pros (spoiler, I liked it enough to buy it). In Chit Chat Across the Pond Bart takes us through Taming the Terminal Part 14, where he explains how to create aliases and prompts.
![]()
mp3 download
Hi this is Allison Sheridan of the NosillaCast Mac Podcast, hosted at Podfeet.com, a technology geek podcast with an EVER so slight Macintosh bias. Today is Sunday January 12, 2014 and this is show number 453. We have a LOT to pack into the show today, I may even need to push some of it out to next week.
I really do love being able to post to podfeet.com mid-week. I know you never told me I couldn’t but it felt like I should warn you at least. Remember I told you last week that Leo LaPorte hosted a discussion with the CEO of Stitcher and the CEO of PodcastOne during New Media Expo, all about the future of radio and podcasting? Turns out Steve recorded a video of that really interesting discussion and posted it on YouTube so I put it on podfeet.com yesterday so it would be really easy for you to find. It’s pretty long so settle in with a nice cup of tea to watch. You may not agree with what they say but I bet you’ll find it makes you think.
Macworld | iWorld
If you’re thinking about going to Macworld | iWorld, when you make your plans, be sure to be there for the Thursday tech talks because my talk is on Thursday at 3pm! I’ll be doing a talk called Digital Disaster – Life After Death. In that session I’ll talk about what you can do to make sure your family and friends know what to do with your digital life if the worst were to happen to you. This was, as you might guess, inspired by what we went through helping Tim Verpoorten’s wife Alice out after he passed away. It’s a grim subject but you know I’ll manage to make it entertaining while you’re learning.
Paul Kent is the event manager for Macworld | iWorld from IDG, and he’ll be the guest for Chit Chat Across the Pond on the 26th of this month, so you’ll learn all the reasons why you really do want to come! If that’s not enough, don’t forget Steve and I are hosting the NosillaCastaways party again on Friday night at Jillians at the Metreon right next to the conference so if nothing else you’ll want to meet the friendly and enthusiastic NosillaCastaways like Leon Sargent who’s celebrating his birthday by going to Macworld! I’ll give you more information on how to RSVP when we get closer to the date.
With all that said, the Macworld | iWorld conference pass goes up after February 28th – right now you get access to the expo floor, all of the tech talks, and the main stage activities for $249. I put a link in the shownotes for the registration page at macworldiworld.com if you want to get in early!
.me Domain Interview from New Media Expo
Let’s start with another short interview from New Media Expo. I’ll play the audio here, and I’ve also included the video as its own blog post earlier today (I’m out of control with this now!)
Dumb Question Corner
In Twitter, Yadiel Sotomayor asked a great question. He asked:
Really dumb question here. What does pressing certain keys on the keyboard do when booting up the Mac? I know T is for target disk mode. But the rest, I have no clue. Is there an article explaining the different functions?”
I knew about a few of the keys that did interesting things during boot up but since he asked about an article I thought I might be able to find a more complete answer. I did a search on Google using a few of my favorite search tricks. I was hoping that Apple would have a knowledge base article on the subject, and I wanted to make sure I didn’t get search results from the discussion forums, Which are often not the definitive source. So into Google I typed:
key during startup site:apple.com -discussions
And that worked perfectly. I was rewarded with Apple knowledge base article HT1533. I put a link the show notes of course but I thought I’d walk you through each of the options. We’ll do the problem to be solved first, and then I’ll tell you what keystroke will achieve that objective.
- let’s say you want to start up from a bootable CD or say a USB thumb drive like back when we used to get OS X install media on a thumb drive. Press C during startup. Easy to remember, c is for CD, that is if you still remember what CDs were for.
- Having trouble with your Mac and you want to eliminate hardware as the problem? Try holding down the D key during startup to run Apple’s Hardware test.
- One of the classic voodoo operations you can do on a Mac when things get weird is to reset your NVRAM. Apple recommends resetting your NVRAM if you have weird problems with speaker volume, screen resolution, getting the right disk to start up or even kernel panics. Before there was NVRAM, we had Parameter RAM on our Macs, and they never changed the keystroke, so to reset your NVRAM, hold down option-command-P-R until you hear a second startup chime. I don’t think this has ever fixed a problem for me but it does make you feel like you’re doing something.
- We just talked about setting a certain disk as your startup volume, but sometimes you want to change it on the fly. If you hold down the option key during startup you’ll get the Startup Manager screen.
- I didn’t know about this next one but I’m sure it would have come in handy back when I had an optical drive on my Mac. If you’ve got a disk stuck in your optical drive, you can boot up holding down either Eject, F12, or hiding down your mouse/trackpad button and it will squirt right out for you. Of course not if it’s a mechanical problem…
- I’ve never needed to boot from a network server using NetBoot but it you know what that is, hold down the N key during boot up. You can also boot from the default boot image on that network server by holding down option-N during boot up.
- Sometimes you want to use your Mac as a disk to another Mac, like when you’re doing data transfer to a new Mac. As Yadiel mentioned, that requires Target Disk Mode which you allow by holding down the T key on your Mac during boot up. Unfortunately this only works via FireWire and I really missed it the last time I transferred data between my Macs. I bet I could add a Thunderbolt to FireWire adapter to my arsenal of adapters and get that back…
- I don’t know about you but I have a LOT of apps loading on startup nowadays – especially my fleet of menu bar apps. I can’t survive without many of them, like TextExpander, Bartender (which organizes my plethora of menu bar apps), iStat Menus to watch my fan speeds and data transfer rates, Shush to mute my mic – many of these are used daily. But what if your Mac is acting janky, and you want to stop all of them from loading at startup, it would be a royal pain to go to System Preferences, Users & Groups, Login Items, and then delete each of them and then later put them all back. No worries, simply hold down the Shift key during startup and it suppresses all of them just during that boot up. Now if your Mac stops the jankiness, you still might have to go back and kill them one at a time and put them back, but at least you’ve narrowed down the problems.
- The next two are pretty geeky but they’ve been known to be helpful to me so we’ll go through them. If you’re having a higher level of jankiness that shutting off the startup items and Apple’s hardware test haven’t resolved, you may have file system errors. Your first line of defense there is to launch Disk Utility in your Applications/Utilities folder. Select your disk and then choose Repair Disk Permissions. You can also verify and/or repair your disk from there. But let’s say that’s not an option for some reason. You then want to run a File System Check, which can be invoked by booting your Mac into Single User Mode. To do this, boot up your Mac holding down Command-S. You’ll actually see some “interesting” gibberish on screen, but then you can type in /sbin/fsck -fy. Now I HIGHLY recommend you read Apple’s Knowledge Base Article TS1417 before heading down this path – they give a lot of explanation of why, how and when to invoke this, and how to interpret the information you get back. I’ve used it before and it did help me out. I said there were two commands in this category – the other one is called Verbose Mode. When you’re in Single User Mode you have to type reboot to restart normally, but with Verbose mode it will exit automatically wen the computer’s startup progresses sufficiently. If you need to do the file system check I’d think you’d want Single User Mode.
- The last key combo is super useful. Let’s say you’re selling a Mac, like I did recently with Steve’s 24″ iMac. I wanted to write zeros all across the disk as it had one time held sensitive information. I first installed Mavericks on the Mac (it was on Snow Leopard before that) by installing from the Mac App Store. I now wanted to run Disk Utility and do a full secure erase (the one pass version since I figure the NSA has all our data already) on the boot volume, but of course I can’t do that since I’m booted from it. I restarted the Mac holding down Command-R to invoke the OSX Recovery System. From there I was able to run Disk Utility and do the erase. Once that was done, and my only internal hard drive was completely empty, I was able from the Recovery System to install Mavericks again. Note that had I not done the Mavericks upgrade first, the Recovery System would have been Snow Leopard. I guess it’s 6 of one half dozen of another, but I thought it was most excellent that the Recovery System stays up to date like that. The Apple support article does note that some CPUs require an EFI Bootrom update to support this feature and they do link to another article telling you how to do such a crazy sounding thing.
I really enjoyed going through these tips and remembering why I cared about most of them, so I hope this answered Yadiel’s “dumb” question and maybe will help one of you in the future.
VoiceOver and Screensharing
Hi Allison, Hey, I would have copied Dave and John for the sake of the geek I’m about to gab but I don’t have their email addresses. Please forward if you think they might have some insight.
So, I need to have remote access to a Mac. There are plenty of options out there—no problem, right? Wrong. You see, the solutions appear to essentially be windows that show an image of the desktop and one can click around in it and have access—yes, that’s all good but those options appear to be inaccessible to VoiceOver. So, I’m looking to truly take over the machine as if my keyboard was controlling the other computer and not just with mouse clicks.
Now, I understand it’s possible to log in through the Terminal but, in this case I need to be accessing Pro Tools and other utilities for a user. Have you heard of such remote access? I guess it’s sort of one step above the kind of remote access through a full screen application one normally encounters. Let me know what you think.
Cheers, Slau
I should mention if you’re new to the show that while Slau is blind, he owns his own recording studio, so he’s a genius in my book. When I read the first part of Slau’s question, I was already forming my answer – just use the Terminal to ssh into the other machine, right? And then I read the next line that said he needed to run Pro Tools on the remote Mac. This was going to take some mad skills to figure out.
I started breaking down the problem. I went to the Finder, and clicked on Go, Connect to Server, and entered
vnc://10.0.1.2
which opens a virtual network connect, otherwise known as a screen share to the Mac at 10.0.1.2, which happens to be my VPN server. Up popped a window with my full desktop on the remote Mac. With keyboard control of the remote Mac, I tapped command-F5, which turns on VoiceOver. As Slau explained, no audio came through. I know, Slau is needy that way – VoiceOver was working but he INSISTS it only matters if he can hear it.
So now we have a simpler question that all this messy stuff about Logic and VoiceOver. The simple question is whether there’s a way to get the audio to be played from a remote Mac via screensharing. I did some googling and found an article on a site called Thoughts From a Hacker bionoren.com that revealed a solution! It uses the well known Soundflower in combination with a tool I’d never heard of called AU Lab which is actually from Apple. I’ve included the link to the most excellent instructions on how to make this “go” but essentially on the Mac you want to control you use Soundflower to talk to AU Lab which then sends the audio to AU Lab on the receiving Mac.
I tested this on a remote Mac (doing it all without leaving my easy chair). In Screensharing, I turned on VoiceOver again and now I can hear everything VoiceOver is saying on the local Mac. Now you may wonder if the remote Mac is now soundless. I DID get my lazy butt out of my easy chair to check, and the remote still makes noise when visited in person.
One thing I find interesting is that the AU Labs app is not from a signed developer, GateKeeper made me use right-click to open…even though it’s from Apple. This might indicate that the app has been around for a long time. At first I also thought it wasn’t accessible, which would mean Slau would have to have someone help set it up for him which would have been a HUGE bummer. The blind, just like everyone else, actually hate it when they have to ask someone to help them instead of being able to do stuff themselves. Go figure. Anyway, it turned out I was misremembering how to use VoiceOver to interact with elements. It was bugging me so I went back in and pulled up the VOLUMINOUS help files and dug around till I figured out what I was doing wrong. When I used the RIGHT keystrokes, everything I played with worked a champ in VoiceOver. I can’t swear to it but I think this will work perfectly for Slau.
Now you may be thinking that this is a very specialized answer that will only help Slau in this unusual problem he was trying to solve, but the person who wrote the article (there’s no attribution on the site) came up with this solution to a completely different problem. This person was actually watching a movie on one Mac but wanted to play the audio on a second Mac because it was connected to the awesome speakers. They had tried things like an Airport Express or Apple TV using AirTunes but they were getting a 2.5 second lag in the audio so that didn’t work at all.
The blogger did find that after several hours this solution did accumulate lag but resetting the connection from either Mac seemed to fix the problem. I was VERY proud of my little self for figuring this one out, and sent my solution along to John and Dave too in case they wanted to include it in Cool Stuff Found.
PortraitPro
 Have you ever had a formal portrait taken where you sit for a photographer and then he or she modifies the photo to “improve” you? After they’re done with the photo, your wrinkles are all but gone, the bags under your eyes removed, you have no pores at all and you look gorgeous. Maybe you don’t look like yourself any more but you do look good. I remember a long time ago when Glamour Shots were all the rage for this kind of photographic transformation.
Have you ever had a formal portrait taken where you sit for a photographer and then he or she modifies the photo to “improve” you? After they’re done with the photo, your wrinkles are all but gone, the bags under your eyes removed, you have no pores at all and you look gorgeous. Maybe you don’t look like yourself any more but you do look good. I remember a long time ago when Glamour Shots were all the rage for this kind of photographic transformation.
 Now you can transform photos without knowing all of the tricks of the trade and without high end tools like Photoshop. Robert Lachman, staff photographer for the LA Times showed Steve and me a really cool piece of software called called PortraitPro from portraitprofessional.com. Before I dig in, PortraitPro is available not just for the Mac but for Windows as well. it’s not in the Mac App Store unfortunately and for some reason it’s not a signed developer, so you do have to control-click to override Gate Keeper’s safety controls in order to open the trial version.
Now you can transform photos without knowing all of the tricks of the trade and without high end tools like Photoshop. Robert Lachman, staff photographer for the LA Times showed Steve and me a really cool piece of software called called PortraitPro from portraitprofessional.com. Before I dig in, PortraitPro is available not just for the Mac but for Windows as well. it’s not in the Mac App Store unfortunately and for some reason it’s not a signed developer, so you do have to control-click to override Gate Keeper’s safety controls in order to open the trial version.
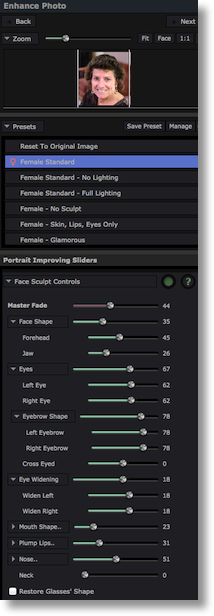
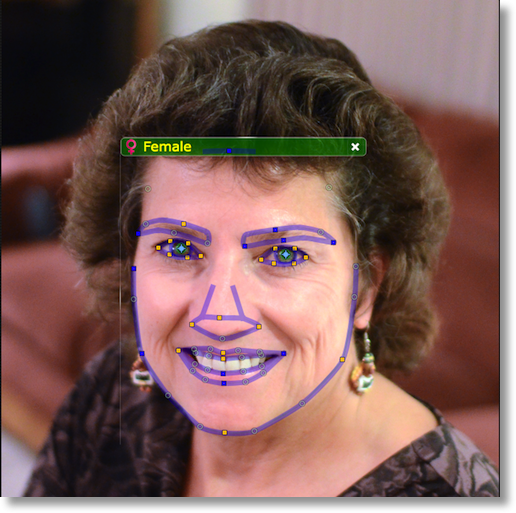
Open a headshot and PortraitPro draws outlines of the eyebrows, eyes (including irises), nose, mouth and the shape of the face. On screen instructions instruct you to drag control points on these curves to more closely match to the portrait. In my experimentation, PortraitPro matched the facial identifiers very well, so I didn’t have to fiddle with it very much. I should mention that the software makes an assumption on whether this is an adult female or male, or possibly a child but lets you correct it if it guessed incorrectly.
Once you’ve defined the facial structure, PortraitPro shows you the original photo on the left, an improved version on the right. For a woman it applies a preset for Female Standard. Now what does a Female standard look like? Taking me as an example, her eyes are slightly larger, her nose is smaller, her skin is smoother, she has fewer wrinkles, her mouth is more pouty, her forehead is taller, her cheek bones are more sculpted…do I need to go on? I have to say that the standard does look mostly like me, but not quite me if you know what I mean.

PortraitPro gives you amazing control using what they call Portrait Improving Sliders for every single thing you could think of to modify facial characteristics. Now you CAN make a beautiful portrait, but of course that’s not what I did at first. I grabbed that face sculpting slider and cranked it all the way up shrinking my face width by about 20%. My eyes need to be Disney doe eyes, don’t you think? My lips need to be plumped, my skin needs to be smoothed more than standard, and of course my teeth need to be whitened! My favorite slider was the neck lengthening control. When I was done absurdly moving the sliders, I sure didn’t look lil eke, but the picture reminded me of my cousin Kyle. I found it interesting that at least I resembled one of my relatives – and one of my good looking relatives at that!

I enjoyed this tool so much that after an hour or so of playing with the trial version, I shelled out the $40 to buy the full version. Then I took that same picture of myself and instead of starting with the preset that did more modification than I’d like, I did every slider by hand. I sculpted my cheeks a little, I lengthened my neck just a smidge, I made my eyes a tiny bit bigger, and added just a touch of plumpness to my lips and brightened my teeth just a little. I did let it lessen the dark circles under my eyes and I might have let it remove a wrinkle or two, but in every case I just did small adjustments on the sliders instead of the more dramatic changes that made me look like my cousin. One of the most flattering changes I made was actually in the lighting – I was able to add left and right shadows and it vastly improved the photograph.
I put the freaky change (with a trial water mark over it) and the flattering and yet still familiar face version in the shownotes so you can see the kind of changes that can be achieved. I think I’ll probably use this to improve photos of my friends and relatives WITHOUT telling them. I’m not sure I’ll do the boys but I know some women who will love my photos after this! Don’t tell them, ok? One more time, the software is called PortraitPro from portraitpro.com.
Clarify
John McNeilly sent in a cool story to me that he suggested I tell to you. He uses Freshbooks, which is an online invoicing service. I use it too for the consulting and advertising I do, highly recommend it. Anyway, he wrote to tech support with an improvement to the way invoices were displayed, specifically that if he was in one project, he wanted to only see invoices related to that project. The tech support person, Jaclyn wrote back saying that she was confused as to where he was in his account, and took a stab at answering it anyway. John wrote back, only this time he included a quick 3 page Clarify document. He had screenshots with red outlines to highlight the tabs he’d clicked on and the areas of concern. He added a couple of titles to the steps and threw in a few words of clarification, and then sent her a PDF of the Clarify document. This must have only taken him about 5 minutes to produce, very simple document.
The response he got back from Jaclyn at Freshbooks was awesome – she wrote back, “Ahhhhhhhhhhhhhhhhhh, but of course. This makes total sense. I now fully understand the situation. Thank you for sending me such great screenshots (tip of the cap if I may).”
He could have gone back and forth 6 times trying to explain in text, but instead he circumvented all of the confusion and helped her see immediately where his concern was. It made HER job so much easier and if you can make it easier for a tech support person to help you, it only makes your life easier too.
Thanks John for the great testimonial! If you haven’t bought Clarify yet, head on over to clarify-it.com, download the free trial for Mac or Windows. Don’t download Clarify unless you’re ready to love it because you will, and then you can buy it for $30 for the Mac or Windows, or you can get a cross-platform license for only $40. Be sure to tell them that John and Allison sent you!
Chit Chat Across the Pond
Security Light
Important Security Updates:
- Reminder – next Tuesday is Path Tuesday, and MS have pre-announced updates to Windows and Office – http://technet.microsoft.com/en-us/security/bulletin/ms14-jan
Important Security News:
- Google expose G+ users who use Gmail to email spam by allowing strangers to send you email via G+ (by default each stranger only gets to spam you once, while those in your circles get to do it as often as they like) – everyone is getting opted into this by default, but you can opt out (my “Google is becoming Facebook” hypothesis strengthens) – http://www.pcworld.com/article/2086722/how-to-prevent-strangers-on-google-from-flooding-your-gmail-inbox.html
- Turns out the Target breach was worse than we thought – the names, mailing addresses, phone numbers and email addresses of up to 70 million ‘guests’ (or ‘customers’ in English) have also been taken – http://krebsonsecurity.com/2014/01/target-names-emails-phone-numbers-on-up-to-70-million-customers-stolen/
- Yahoo lives up to it’s promise and now defaults to HTTPS on Yahoo Mail – http://nakedsecurity.sophos.com/2014/01/10/yahoo-makes-good-on-its-promise-to-enable-https-by-default-for-yahoo-mail/
- SnapChat’s arrogant dismissal of a reported security vulnerability as “theoretical” leads to the leaking of the names and phone numbers of 4.6 million users. The company’s responses throughout this incident leave a lot to be desired, but they did finally apologise and promise to take steps to remedy the problem – http://nakedsecurity.sophos.com/2014/01/09/snapchat-blurts-out-the-s-word/
- Remdiner – Phishers will use any pretext they can think of to try spam you – including data breaches – phishers sent out emails pretending to be from JP Morgan Chase about their recent data breach – http://nakedsecurity.sophos.com/2014/01/06/followup-phish-targets-possible-victims-of-last-months-jp-morgan-chase-card-breach/
- More bad news for many home routers – a whole bunch of them are found to contain a back door – for MOST the back door is ‘only’ on the LAN side, but for a few, it’s on the WAN side – http://nakedsecurity.sophos.com/2014/01/03/gaping-admin-access-holes-found-in-soho-routers-from-linksys-netgear-and-others/ (list of known affected devices: https://github.com/elvanderb/TCP-32764)
Suggested Reading:
- IOActive Labs finds that the security of many iOS banking apps leaves a lot to be desired: http://blog.ioactive.com/2014/01/personal-banking-apps-leak-info-through.html
- The war against FlashBack continues – Intego Research shows there are still over 22,000 infected Macs out there – but Apple is protecting those infected Macs by bulk-purchasing all the command and control domains – having recently purchased all those for 2014 – http://arstechnica.com/security/2014/01/its-alive-once-prolific-flashback-trojan-still-infecting-22000-macs/
- Sophos finds that 82% of Enterprise Mac users are not getting security updates because they are running old versions of OS X – http://nakedsecurity.sophos.com/2014/01/09/82-of-enterprise-mac-users-not-getting-security-updates/
- The NSA paid RSA $10M to make the random number generator who’s design they sabotaged the default – http://www.reuters.com/article/2013/12/20/us-usa-security-rsa-idUSBRE9BJ1C220131220
- Security Researcher claims NSA can inject malware into any iOS device – Apple deny they helped them in any way – http://www.macobserver.com/tmo/article/nsa-can-hack-and-spy-on-any-iphone-any-time
- The UK’s Centre for the Protection of National Infrastructure (CPNI) has recently released a paper titled “Spear Phishing – Understanding the Threat” – the paper explains who’s likely to be spear phished and the protections organisations can put in place – http://www.us-cert.gov/ncas/current-activity/2013/12/30/UK-CPNI-releases-Spear-Phishing-paper
- Sophos release a handy free Security Thesaurus to help you understand and/or explain computer security jargon – http://nakedsecurity.sophos.com/2013/12/25/on-tech-support-duty-for-family-at-christmas-get-our-free-threatsaurus/
A Quick sorbet – Another Take on BitCoin
Without doubt, the cryptography in BitCoin is well designed and is standing up well to scrutiny. From a computer science point of view there is a lot to admire in BitCoin.
When it comes to a digital currency though – the computer science is only part of the equation, the other part, and arguably the more important part, is the economics of the thing.
I’m not an economist and I have no training in economics, but, I do make an active effort to understand economics, and to keep myself informed on the topic. I’ve read the arguments for and against the economic doctrine that BitCoin embodies, and in my opinion, it’s built on a highly questionable foundation – the idea that the problem with the world is that we left the Gold Standard and created central banks – basically, the libertarian economics of Ayn Rand.
In NosillaCast terms, you have to remember that central banks were created to try solve a real problem – the devastation massive booms and busts wreak on ordinary people. The job of central banks around the world is to act as a countervailing force to booms and busts, so as to stabilise the economy. When the economy starts to overheat, the central banks apply the brakes, and when the economy starts to stagnate they inject stimulus to get things going again. Two tools used to try achieve this stabilising effect are changes in interest rates and the supply of money. When things start to over-heat you raise rates and/or take money out of the economy, and when things start to go south you lower rates and/or put more money into the economy.
There can be no BitCoin central bank, and that’s by design. This makes BitCoin a really interesting economic experiment, but a rather risky place to invest real money!
My advice to anyone thinking of getting involved with BitCoin would be to treat it like the stock market. Yes, you could make a tidy profit, but, you could also lose the lot. If you have disposable income, why not, but please think very hard before putting money that’s not disposable into BitCoin!
Before you get too financially invested in BitCoin I’d recommend recommend this article by Nobel Prise winning economist Paul Krugman (and the articles he links to in it) – http://krugman.blogs.nytimes.com/2013/12/28/bitcoin-is-evil/
Main Topic – Taming the Terminal Part 14 of n (Aliases & Prompts)
http://www.bartbusschots.ie/blog/?p=2782
That’s going to wind this up for this week, many thanks to our sponsor for helping to pay the bills, Blue Mango Learning at bluemangolearning.com makers of ScreenSteps and Clarify. Don’t forget to send in your Dumb Questions, comments and suggestions by emailing me at [email protected], follow me on twitter and app.net @podfeet. Check out the NosillaCast Google Plus Community too – lots of fun over there! If you want to join in the fun of the live show, head on over to podfeet.com/live on Sunday nights at 5pm Pacific Time and join the friendly and enthusiastic NosillaCastaways. Thanks for listening, and stay subscribed.

Let me take a few minutes here to reiterate my stance on Bitcoin, partially in response to Bart . I believe I stated this in our discussion last week, but it doesn’t hurt to reiterate (bits are cheap).
I am fascinated with Bitcoin from both a technological and a socio-political standpoint. The cryptography is well-engineered, and the various controls in place (limiting the total number of Bitcoins in circulation, the rate limits imposed on their creation, etc.) are IMHO well thought out.
Is it The Answer(TM) to the global financial system? Ehh, I’d tend to say “no”, but think that the jury’s still out on that one. As Bart said, this is an experiment on a grand scale, and I for one am fascinated to see where this all goes.
Is Bitcoin useful? Absolutely. Is it safe to use? (Note I said “use” NOT “invest in”) Yes. There are many reputable outfits that will let you convert between Bitcoins and real currency. Coinbase is the one I use and I am very comfortable with it. It has some real solid backing behind it, in other words it’s not a fly by night operation that’s liable to up and disappear tomorrow. There are legitimate reasons why one would want to use Bitcoin. Say you want to make a donation to support a cause, that you may not necessarily want Them(TM) to know about. (“Them(TM)” could mean “the NSA,” “your bank,” “your boss/friend/spouse/parents/etc.”) Say, for example, if Edward Snowden had a legal defense fund, and you wanted to show your support for what he did without tipping off the authorities; or if you want to donate to a controversial organization that you happen to support, like the Pirate Bay or whatnot. Or maybe you just want to send an anonymous tip to your favorite Redditor/YouTuber/podcaster/whatever.
BTW, what I did not mention is that there is absolutely nothing holding you back from creating more than one Bitcoin address. You can have as many Bitcoin addresses as your computer has storage space for. (And Bitcoin addresses, being basically a public/private key pair, are very very small.) So if you’re *really* paranoid you can create a whole bunch of Bitcoin addresses and forward your payment back and forth between them several times. Sort of like in those spy movies where the agent on the run is calling his headquarters to try and make a deal, but makes the call impossible for them to trace by bouncing it across 18 different phone networks, 12 satellite links, 5 undersea cables, etc. etc.
Would I accept Bitcoin payments for goods and services I provide? Maybe. I would probably answer differently if said work was my main “bread and butter” income. But the fact is that I have a day job that covers that, and for those little side jobs I do for people on off hours, yeah I would probably be wiling to accept payment in BTC.
Would I invest in Bitcoin? That means either buying Bitcoins using real money, or paying to set up a Bitcoin mining rig. That is completely up to you. Although, as Allison and Bart said, I probably wouldn’t do so unless I had a comfortable income and were willing to take a loss if the value of BTC were to plummet (and it has).
Note that I have not actually sunk any “real” money into Bitcoin, except for maybe a trivial amount (a few dollars tops) in electricity costs. I have two computers that are doing Bitcoin mining, but that’s not all they do; I use them for other work-related projects, as well as personal stuff (media center, file server, etc.) So I already owned the computer equipment, and I already keep it running 24/7. I started out by pool mining Bitcoins with my GPUs, and amassed a few BTC that way. I lucked out here because this was back when the BTC->USD exchange rate was pretty high. So I took those BTCs and invested them in ASIC miners. (Again I lucked out when I got these, I happened to get them when they were at a really good price, around the equivalent of $10-11 a pop) Now that I’ve maxed out my USB miners, I have just been holding on the BTC that I have been mining, and have amassed the equivalent of several hundred dollars in BTC. Not exactly “time to fly to Tahiti” money but enough for a nice meal out and/or a geek gadget every now and then. I’m mainly doing it as a way to participate in this experiment, to see where it all goes, and to help the Bitcoin network (since because it’s peer to peer, having as many nodes as possible online processing transactions is beneficial to the network’s overall health) The BTC income I just consider a temporary added perk (temporary since it will diminish over time as the mining difficulty increases, payouts decrease, etc.)
Hey, I’m trying to build a Freshbooks alternative called ZipBooks. I’d love for you to check it out and see what you think. It’s a great way to send out invoices for free!
[…] think the first time I talked about the wonderful menu bar app organizer, Bartender, was in January of 2014. When I do my annual nuke and pave, Bartender is in the top list of critical apps I install first. […]
Стою перед стеллажом с красками, и голова идет кругом. Такое ощущение, что я попал в художественный магазин без всякого представления о том, что хочу нарисовать. Проблема в том, что я затеял обновление гостиной, и цвет стен, как мне казалось, должен был быть самой простой частью этого процесса. Но вот уже третий день я смотрю на эти бесконечные палитры, и любая уверенность в своих дизайнерских способностях улетучивается.
Потом еще возникает вопрос о типе краски. Матовая, глянцевая, полуматовая? Для гостиной, наверное, матовая предпочтительнее, чтобы скрыть мелкие неровности стен. Но, говорят, она менее стойкая к загрязнениям. А у меня маленький ребенок и собака! Получается, в любом случае придется выбирать между красотой и практичностью.
Уже все глаза сломал, рассматривая эти маленькие образцы на картонках. В магазине освещение совершенно другое, чем у меня дома, так что я понятия не имею, как выбранный цвет будет выглядеть в реальной обстановке. И главное, хочется создать уютную и стильную атмосферу, а не просто покрасить стены ради покраски.
Может, у вас есть какой-то личный опыт в выборе краски для гостиной? Какие цвета оказались наиболее удачными и практичными? Буду очень признателен за любые советы и рекомендации! Интересует [url=https://taksafonchik.borda.ru/?1-2-0-00001361-000-0-0-1756719279]краска по ржавчине.[/url]
Асфальтирование – это многоэтапный процесс, требующий соблюдения технологических норм и использования специализированной техники. Качественно уложенный асфальт – это залог долговечности дорожного покрытия, его устойчивости к нагрузкам и неблагоприятным погодным условиям.
Подготовка основания: Этот этап – фундамент будущего покрытия. Сначала производится очистка территории от мусора, растительности и старого покрытия. Затем выполняется выравнивание основания с использованием геодезических инструментов. При необходимости, проводится укрепление грунта, например, с помощью геосетки. Важно обеспечить хороший дренаж, чтобы избежать скопления воды под асфальтом.
Укладка щебёночного основания: Щебень служит дренажным слоем и распределяет нагрузку от транспорта. Сначала укладывается крупная фракция, затем более мелкая. Каждый слой тщательно утрамбовывается катком. Толщина щебёночного основания зависит от предполагаемой нагрузки на дорогу.
Укладка асфальтобетонной смеси: Асфальтобетонная смесь доставляется на место укладки в специальных термоизолированных машинах. Смесь равномерно распределяется по основанию с помощью асфальтоукладчика. Важно соблюдать температурный режим укладки, чтобы обеспечить оптимальную плотность и прочность покрытия.
Уплотнение асфальта: Уплотнение асфальта производится с помощью катков различных типов. Сначала используются лёгкие катки для предварительного уплотнения, затем более тяжёлые – для окончательного. Уплотнение необходимо проводить до полного остывания смеси.
Контроль качества: На каждом этапе укладки асфальта необходимо проводить контроль качества. Проверяется ровность основания, толщина слоёв, температура смеси и степень уплотнения. Делитесь своим опытом и подрядчиками на [url=https://2stol.ru/index.php?topic=1006.0]укладка асфальта санкт петербург[/url]