If you already know what xkpasswd is, and you want to jump right to the tutorial, click here.
What is xkpasswd?
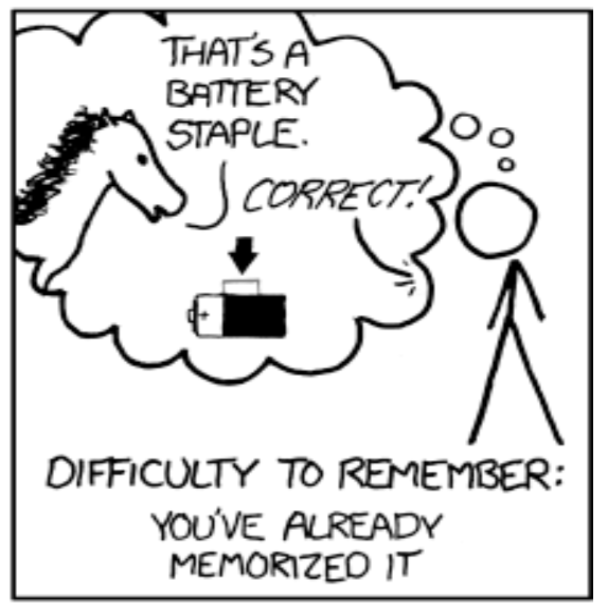
Back in 2011, Randall Munroe, the author of the fantastically nerdy and hilarious comic strip XKCD wrote a comic he calls Password Strength. In the illustration he explains how by forcing humans to create complex passwords, we have actually encouraged them into creating easy to guess passwords that are terribly difficult to remember.
Being a nerd, he includes how many bits of entropy are in these awful passwords and then explains how if we just string four random, common words together we’d have much more difficult passwords to crack that were actually possible to remember. The example strong password he uses is “correct horse battery staple” and that line has become a staple phrase amongst those who encourage good passwords.
Around that same era, Steve Gibson made a very compelling case on the podcast Security Now! with Leo LaPorte for the importance of password length over password complexity. I won’t even begin to try to explain the math behind it (but here’s a link to the 37-minute explanation). Both the XKCD cartoon and Steve Gibson were trying to get across to us that it’s possible to create really good passwords that we can actually remember.
Bart Busschots started noodling these two ideas in combination: XKCDs illustration of how common words can make good passwords, and Steve Gibson on the fact that longer by definition is way harder to crack. From these ideas, Bart created a tool to help people create long, strong and yet memorable and typeable passwords. He called his project called XKPASSWD (for a head nod to XKCD) and later Bart published it as an open source project on Github calling it Crypt-HSXKPasswd. Bart has a full explanation on all the tech behind this tool at bartbusschots.ie/…
Bart’s tool is available as a user-friendly website at xkpasswd.net. While I’ve mentioned it a million times on the show, and Bart and I have talked about it together, it occurred to me recently that I’ve never written a guide on how to use xkpasswd. I use it all the time to create my passwords. In fact, I use it so much that it is a pinned tab in Safari so that I can simply click the tiny little square tab and I’m ready to create a password that I won’t hate.
As you make these long, complex, and yet easy to remember passwords, I’m hoping that you’re using a password manager like 1Password or LastPass. No matter how good your memory is, if you aren’t using a password manager, you’re bound to reuse passwords or to start mutating one of the good ones we’re about to create. Unique passwords are critical to keep your stuff safe, and no matter how memorable the passwords are, you simply cannot remember them all so use a password manager. Please?
I’ll remind you again at the end, but creating this tool took Bart a long time to write and prove the math, and he continues to pay for the server to support it. If you think it’s as cool as I do, be sure to hit his Donate button to help pay the bills.
With that looooong introduction, let me dig into explaining how to actually use xkpasswd to create strong passwords in a way that you can remember and type. I’m going to walk you through the settings at xkpasswd.net and show you how flexible this tool is to make passwords you won’t hate.
Generate Password(s)
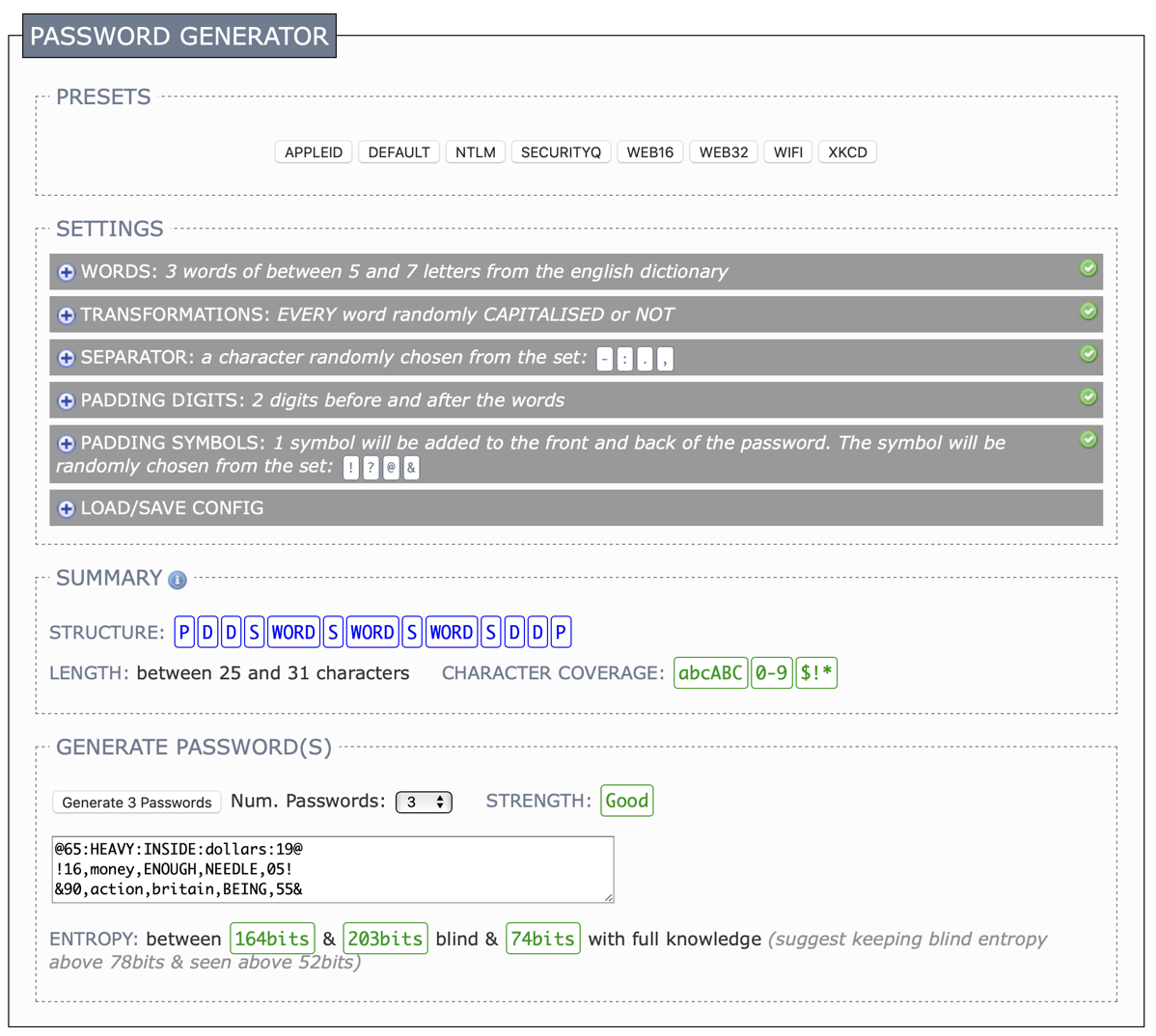
Oddly enough, I’d like to start at the bottom of xkpasswd. The very last section in the tool is called Generate Password(s). In that section, you’ll see a button that says Generate 3 passwords. If you simply click that button, 3 passwords of the default format will be spit out into the text box next to the button. If one of those 3 passwords looks like something that makes you laugh or reminds you of something and it looks like you have the patience for the format and length, then simply copy it and use it. You don’t need to follow along with the rest of this tutorial. But I bet you want to know what else it can do.
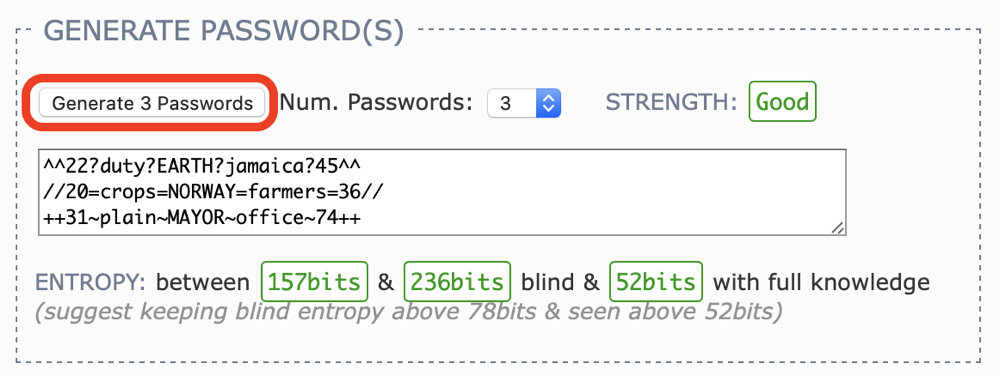
If you’re curious about how good the passwords are that you created by clicking the button, you’ll notice a few boxes beside and next to the generated passwords that will tell you something about them. If you want to keep it simple, look at the strength. It will say “Good” in green if you’ve kept with the defaults. Down below the text box, it will tell you about the entropy of the password. Entropy is a super nerdy term that I learned about in physics that has to do with thermodynamics, but in this context, the term means simply, “lack of order or predictability”. You want a password that has as little order and predictability is possible.
Where we fall back into the land of nerds again is in how it’s measured. As you’ll see when you click the button for the default 3 passwords, it says the entropy is between 157bits and 236bits blind, and 52bits with full knowledge. We are not going to worry our pretty little heads about this because Bart helpfully colors these numbers in green if they’re good and red if they’re not, and the strength will change color too if you pick bad settings. Remember, green is good, red is bad.
Within the Generate Passwords section, you can use a pulldown to change the number of passwords generated every time you push the button, or you can just obsessively keep clicking the button. I like clicking it, makes me feel like I’m in Vegas pulling the handle of a slot machine to see what will come up. As I said, I wait until I see one that makes me laugh or reminds me of something.
Presets
Now that you know you can stop listening to me at any point and just start generating passwords, let’s explore the rest of the tool, starting with the presets. Across the top of xkpasswd there are 8 preset buttons to choose the format of the passwords that will be generated. Each preset is designed to solve a different problem. If you hover over each preset, a popup will tell you what problem it is trying to solve. I’ve put them all in the blog post so you can scan them without hovering.
- APPLEID
- A preset respecting the many prerequisites Apple places on Apple ID passwords. The preset also limits itself to symbols found on the iOS letter and number keyboards (i.e. not the awkward to reach symbol keyboard)
- DEFAULT
- The default preset resulting in a password consisting of 3 random words of between 4 and 8 letters with alternating case separated by a random character, with two random digits before and after, and padded with two random characters front and back
- NTLM
- A preset for 14 character Windows NTLMv1 password. WARNING – only use this preset if you have to, it is too short to be acceptably secure and will always generate entropy warnings for the case where the config and dictionary are known.
- SECURITYQ
- A preset for creating fake answers to security questions.
- It’s important that you do not answer security questions with real answers. This is how your accounts can easily be hacked. If for example, the question is, “what is your mother’s maiden name?” this information is easily available on the Internet. Instead, use this preset and get an answer such as “pull uncle Belgium dollars space meat!” from xkpasswd. (It really gave me that security answer, isn’t that awesome?)
- WEB16
- A preset for websites that insist passwords not be longer than 16 characters.
- WEB32
- A preset for websites that allow passwords up to 32 characters long
- WIFI
- A preset for generating 63 character long WPA2 keys (most routers allow 64 characters, but some only 63, hence the odd length).
- I have a cautionary tale on this 63-character business for your WiFi password. Sure we have a password manager so we don’t have to type it often, and our phones offer barcode scanning to other people so they don’t have to type it. But I have a super long password on my WiFi router and I have had to type it into the old-style Apple TV remote. You remember, the silver one with the buttons to click back and forth to select the characters? I also had to type it into my HP printer which has a non-touch screen display that is 2 3/8″ diagonally and has a QWERTY layout I had to navigate with up/down and left/right buttons. I may have said some non-Girl Scout safe words about Bart while I was typing that in. And mine is only 24 characters long, not 63!
- XKCD
- A preset for generating passwords similar to the example in the original XKCD cartoon, but with a dash to separate the four random words, and the capitalisation randomised to add sufficient entropy to avoid warnings.
Settings
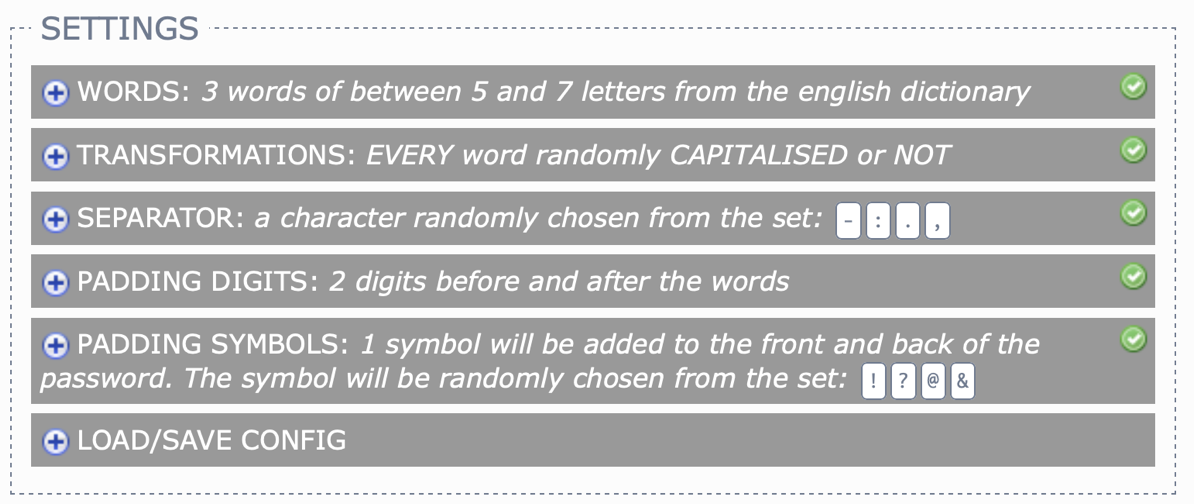
With a given preset selected, the Settings Section presents 6 different settings that modify how the password(s) will be created. Next to each setting is a little plus button inviting you to click anywhere on the setting to change the values. Let’s walk through all of the settings using the APPLEID preset as our starting point.
WORDS
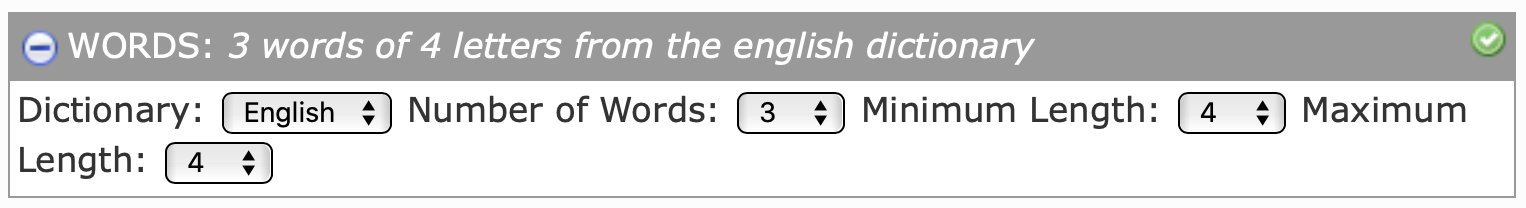
The first setting is the number of words in the password. The APPLEID preset starts with 3 words of between 5 and 7 letters from the English dictionary. We can modify this from 3 words to anywhere from 2 to 10 words. I don’t know about you but 3 sounds like enough. You can change the minimum and maximum lengths of the randomly chosen words from 4 to 12 characters each. You can play around with these lengths, but if you shorten them, be sure to test your changes by tapping that Generate 3 Passwords button at the bottom and watching to make sure the Strength is still green for Good.
All of the presets use words from the English dictionary. Inside the Setting for WORDS, it has a dropdown to change the dictionary language, but English is the only option. If you want to go crazy with other dictionaries, go check out Bart’s open source project I mentioned where you can preload other languages’ dictionaries.
TRANSFORMATIONS
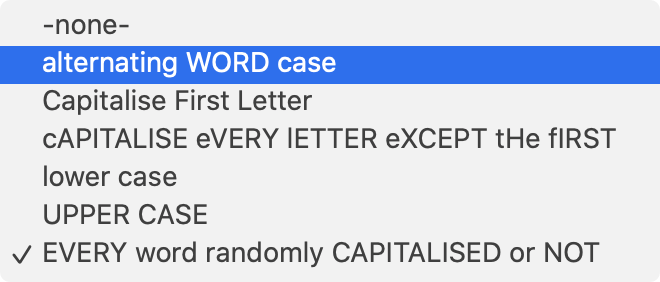
One of the easiest ways to increase the search space for a password hacker is to have both upper and lower case letters in your password. But imagine how annoying it would be (especially on a phone keyboard) to type in a password with every other letter capitalized. Just having one in there would make it harder to crack but remembering where that one capital letter is would be too much for our little brains.
By default, the APPLEID preset randomly chooses whether to capitalize each word or not. Because it’s randomly doing it by word, the password generator may offer you options with all upper case or all lower case. This isn’t a coding error if it happens, that’s by design.
To ensure you have both upper and lower case letters, you can choose another option from the dropdown such as “alternating WORD case” or “Capitalise First Letter”. If you really want some entertainment, he’s got an option to “cAPITALISE eVERY lETTER eXCEPT tHE fIRST”. If doing the upper/lower case thing is too much friction for you, there are options to have just lower or just upper case words in your password. Watch those entropy colors at the bottom when you generate the passwords though!
SEPARATOR
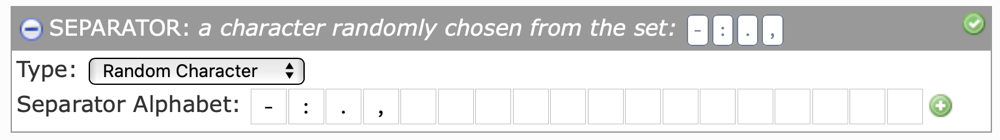
Another great way to increase the entropy of a password is to add in special characters. But rather than sprinkle them randomly inside your password, xkpasswd uses them as separators between the words. Having a special character as a separator between words actually makes the password way easier to read and remember.
By default, xkpasswd will choose a random character from an Alphabet. The Alphabet by default contains dash, colon, period, and comma. These characters are displayed inside little boxes, like the ones where you have to fill your name in on a form and they want to make sure you write clearly. There are a bunch of empty boxes inviting you to type in more characters to add to the Alphabet. You can even delete characters from the Alphabet. As you add and delete, the set gets updated real-time up above. For some reason, there’s a green plus sign at the far right of the little boxes where you put the characters but it doesn’t seem necessary to click it. You can if it makes you happy though!
If there’s a character that you prefer to type and would like to make your passwords always have that same character, you can change the separator to be a specified character using the dropdown and then type in the character you prefer. While the password would seem as strong whether the separator is chosen randomly or whether you use the same one every time, there is a difference. If someone sees one of your passwords for something you don’t really care about, they can figure out the pattern you’re using for your passwords and have a better shot at getting into an important account.
For example, let’s say you tell someone your WiFi password and they notice that you have 4 words of 5 characters always separated by hyphens. That gives them a way smaller search space to crack your password. Now of course if you’re not a high-value target this is probably not a big deal, but something to keep in mind. I think that’s what Bart is talking about when he shows us the bits of entropy “with full knowledge”. Someone knows the pattern but they don’t know exactly what characters are in each slot.
PADDING DIGITS
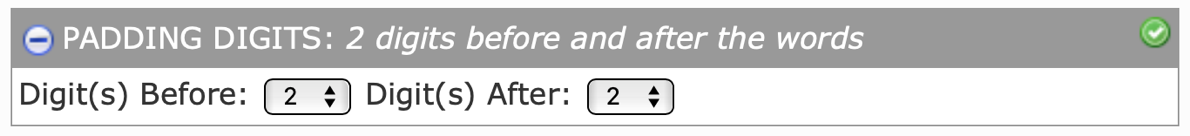
In addition to a bunch of words separated by a special character, Bart’s password design with xkpasswd adds a couple of digits (aka numbers) before and after the words. He calls these PADDING DIGITS.
By default, the APPLEID preset has 2 digits before and after and can be changed to 0-5 digits using the pulldowns. Having these PADDING DIGITS, even just one at the front or back of the password is yet another easy way to increase the search space for the hacking computer to try to guess your password. I don’t advise setting this to zero.
PADDING SYMBOLS
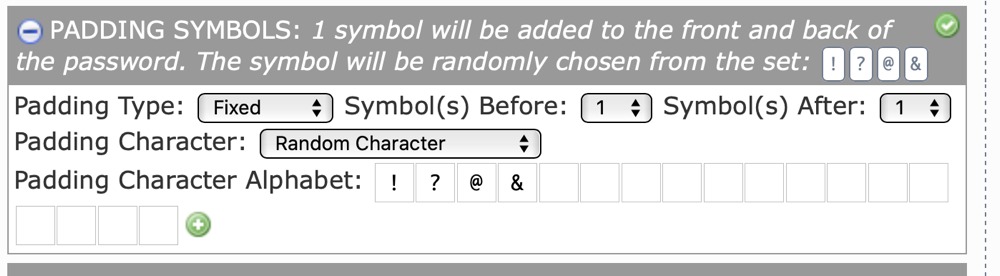
The final setting you can change at xkpasswd is PADDING SYMBOLS. Not to be confused with SEPARATORS, or PADDING DIGITS, PADDING SYMBOLS are a special character (or more) that pads your password at the beginning and end.
This section has a lot of options. Just like the SEPARATOR settings, you can choose a random character for your PADDING SYMBOLS, add to the Alphabet, and change it to a specified character. But you can also set it to match whatever is chosen for the SEPARATOR character. I like that option a lot so I don’t have to remember two special characters. You can set the number of PADDING DIGITS before and after the other characters, using the Fixed option for Padding Type.
But there’s another option in here that’s very unusual. If you have a goal of making a password that’s of a specific length, such as 32 which is often a guideline for a wicked good password, you can change the Padding Type from Fixed to Adaptive using the pulldown. This will reveal a field where you can enter the length you want your entire password. Let’s say you’ve chosen 3 words of 4 characters each with just separators and no padding. That would be a 14-character password which isn’t really long enough without a lot of entropy (it’s only 89 bits and says OK in yellow instead of Good in green!) If you use the Adaptive option and set it to pad to length 20, it will add 6 of the same character to the end of your password. I just tried it and got “main-song-VIEW!!!!!!” for a password.
Your first thought would be that adding 6 exclamation marks can’t possibly make it a good password, but that’s where Steve Gibson’s lesson in Security Now! Comes in. I won’t go through his explanation, but the bottom line is that simply making a password longer makes it a lot stronger. With only 1 exclamation at the end of my password scheme was 96 bits of entropy, while adding 6 of them made it 128 bits of entropy.
I think this option might be the best illustration of what makes a strong password – having all different kinds of characters, upper and lower case, and lots of characters even if they’re repeated will get you a good password. There is a danger with the repeated characters. If I’m sitting next to you and I see you using all kinds of random fingers to type a password and then I see you reach over and hit one key six times, I’ll probably notice which key and I’d have an advantage cracking it.
LOAD/SAVE CONFIG
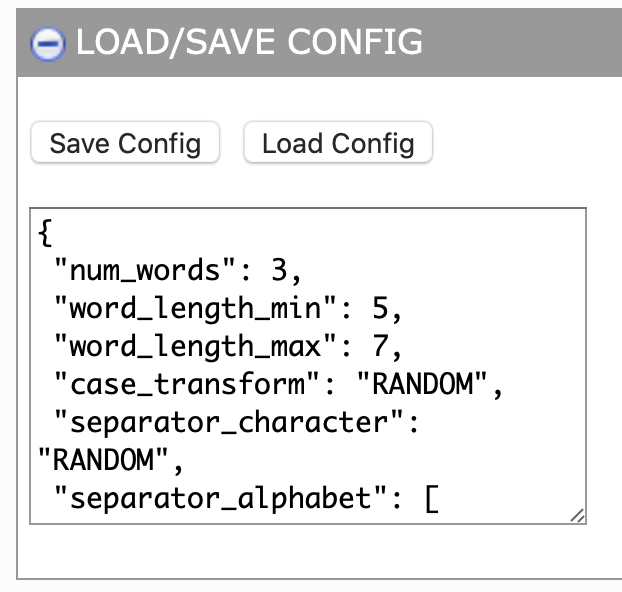
The last section in Settings is really cool if you don’t want to use one of the presets. Heck, you’re with me this far you must enjoy the customizations. This section is called LOAD/SAVE CONFIG. If you open it up and click the Save Config button, it will spit out what’s called a “dictionary” in programming terminology. It’s a set of name/value pairs that match the settings you’ve chosen.
For example, if you choose the APPLEID preset and then select Save Config, the text box will say "num_words": 3, "word_length_min": 5, etc. You don’t have to be a super nerd to use this config file (but if you want to, you can use it with Bart’s Crypt-HSXKPasswd open source project. But if you’re a budding nerdlet, there’s still some fun to be had.
I created a configuration I favor (and no I’m not going to tell you what it is) and then tapped on Save Config. I then copied what was in the box and pasted it into a TextExpander snippet. Instead of having to flip all the switches to get the configuration of settings I like every time I use Bart’s tool, now when I come to xkpasswd.net, I can simply type my TextExpander abbreviation into the little box and hit the Load Config button. After that, I hit the Generate 3 Passwords, chose the funniest one and I’m ready to go.
Summary
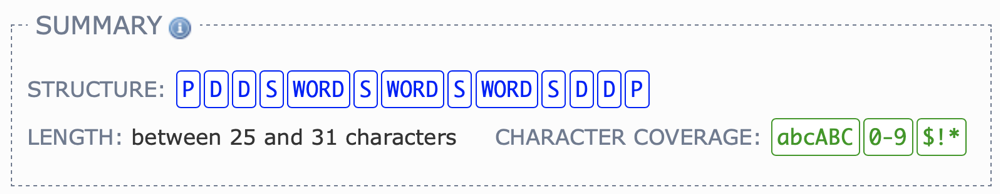
The final piece of information xkpasswd provides you is a nice visual summary of the password scheme you’ve created. First it gives you the structure with a series of little boxes.
For example, for the APPLEID preset it says P (padding character) DD (two digits) WORD S (separator) WORD S WORD S D D P. I know that sounds dopey as I read it out but when you’re looking at it it makes perfect sense! Then it tells you the length of the password it will generate, which for the APPLEID preset is between 25 and 31 characters. That length variability is because the length of the words was 5-7 characters each.
Finally, it tells you your character coverage which gives you an idea of whether you’ve got enough types of characters. The APPLEID preset says abcABC showing we have both lower and upper case, then 0-9 showing we used numbers and $!* which means it includes special characters.
Bottom Line
I am really glad I wrote this up because it made me really understand every little setting in Bart’s xkpasswd tool and how I can modify them. I’ve been an avid user for ages, probably since the first time he showed it to me, but I wasn’t taking advantage of everything it can do. I hope you’ll consider using xkpasswd to generate your passwords so that they’re easy for you to type and remember, but hard for computers to crack.
I also hope you’ll appreciate how much work went into not just the beautiful design of this tool but the math behind it to make sure it’s safe for us to use. With that appreciation, again please consider pushing the donate button for Bart. I push it and donate around once a year!