In this episode we’ll try to eliminate some misconceptions about why a VPN is important and how S/MIME email is cross platform. Dr. Matt tells us about a free OSX VPN client called Tunnelblick from code.google.com. Kirschen Seah from FreeRangeCoder.com reviews Airstash from Wearable. How Howard in the Apple store told us his story of tragedy and triumph, and why I’m feeling good about having THREE backups with CrashPlan. Ken Wolf reviews Buffer from BufferApp.com. If you don’t have Clarify yet, it’s part of the $10 Macheist bundle for only 2 more days. In Chit Chat Across the Pond I had the great pleasure of talking to Stewart Cheifet, TV host of the Computer Chronicles and Net Cafe, and now at cheifet.com.
![]()
mp3 download
 Hi this is Allison Sheridan of the NosillaCast Mac Podcast, hosted at Podfeet.com, a technology geek podcast with an EVER so slight Macintosh bias. Today is Sunday April 21, 2013 and this is show number 415. I had SUCH a great weekend. As many of you know, Steve and I share the same birthday (I’m 4 hours older than him). Because of that neither of us has ever done a surprise birthday but this year I had a great idea. I contacted our crazy friends Dean and Suzanne from Chicago and asked them if they’d fly out here to surprise Steve. I got my friend Diane in on it with me and we decided that as far as Steve knew, Diane and her husband Bill were taking us to the M-Grill Brazilian Steakhouse in downtown LA on Friday night. Unbeknownst to Steve, Dean and Suzanne flew in on Thursday, and spent the night and next day with his sister Q who happens to live right around the corner from us. I ordered a limo to pick up first Diane and Bill, and then Dean and Suzanne, and then over to our house. When it arrived, of course Steve assumed Diane had ordered the limo (she does that kind of crazy thing) but when he got in, there were Dean and Suzanne. It worked out GREAT!
Hi this is Allison Sheridan of the NosillaCast Mac Podcast, hosted at Podfeet.com, a technology geek podcast with an EVER so slight Macintosh bias. Today is Sunday April 21, 2013 and this is show number 415. I had SUCH a great weekend. As many of you know, Steve and I share the same birthday (I’m 4 hours older than him). Because of that neither of us has ever done a surprise birthday but this year I had a great idea. I contacted our crazy friends Dean and Suzanne from Chicago and asked them if they’d fly out here to surprise Steve. I got my friend Diane in on it with me and we decided that as far as Steve knew, Diane and her husband Bill were taking us to the M-Grill Brazilian Steakhouse in downtown LA on Friday night. Unbeknownst to Steve, Dean and Suzanne flew in on Thursday, and spent the night and next day with his sister Q who happens to live right around the corner from us. I ordered a limo to pick up first Diane and Bill, and then Dean and Suzanne, and then over to our house. When it arrived, of course Steve assumed Diane had ordered the limo (she does that kind of crazy thing) but when he got in, there were Dean and Suzanne. It worked out GREAT!
Using a Screen Reader? click here
Dean and Suzanne spent the rest of the weekend with us – so we’ve pretty much been laughing since Friday at 5:30! Steve and I normally exchange presents but I pointed out that this year I got him PEOPLE. It was an absolutely fabulous time. I put a link in the shownotes to the video from Steve first seeing the limo up till he sees Dean and Suzanne. Ok, enough goofing around, just had to tell you about that, let’s talk about some tech.
In this week’s show, we’ve got some more about home VPNs because there’s been a lot of interest and some questions about it. Then Kirschen brings us a review of the AirStash from Wearable, we’ll talk about Howard and his backups at the Apple store, and then Ken Wolf reviews Buffer. In Chit Chat Across the Pond I had the great pleasure of talking to Stewart Cheifet, host of the Computer Chronicles and Net Cafe that were on the air from the 80s till 2002. You definitely don’t want to miss that!
VPN update
The VPN setup Donald gave us is generating a LOT of buzz, it’s been a lot of fun to see how many people are giving this a try. This week I got an email from an actual professor in computer science from an actual university. Let’s hear from Dr. Matt:
Allison,
I have used the OpenVPN for a long time, and I have found that Tunnelblick has worked very well compared to when I started. I know you linked to it in your show notes, but I think you should re-look at it. It is free, and if you would use it, you would have an entirely free VPN setup.Thanks, Matt
Well this sounded swell so I googled Tunnelblick and found it over at code.google.com. When I launched Tunnelblick the only thing I had to change to get it to work was to go into the advanced preferences and tell it NOT to use it’s own tun/tap drivers. I’m wondering though, if I hadn’t already installed the tun/tap drivers per Donald’s instructions, would I have gotten to skip that step?
I encourage you to try Tunnelblick for free and if it doesn’t work for you go ahead and spring the $20 for Viscosity.
Now is probably a good time to drop in a recording from George from Tulsa on the same subject.
George from Tulsa on Encryption and WiTopia VPN
In show 412 Bart taught us how to implement email encryption. But from John’s unanswered question in the comments, it seems to work only between Macs. And, as David Allen asked, I wonder what happens when the certificate self-expires a year after issue. That’s why I’m sticking with Keka to encrypt 7zip files for Windows or Linux, and OS X’s own Disk Utility to make DMG files for fellow Mac users.
Well George I’m glad you mentioned this because I can see how it might be easy to misunderstand this. The process Bart explained is definitely not a Mac only thing. The S/MIME protocol for sending and receiving signed, and/or encrypted email is an industry standard, nothing to do with Macs. StartSSL.com is a cross platform, web-based tool to get your certificate and private key. We did only teach about using the Apple Keychain to install it on a Mac, but you can definitely do this on Windows and Linux.
As far as David’s question about what happens when the certificate expires in a year, you must have missed it last week when Bart explained exactly what happens. If the certificate expires, you can’t open those encrypted emails, which is exactly why Bart suggests only encrypting when you need to, and when you receive an encrypted email, if you need to keep the info long term, get it out of mail.
Encrypting the files themselves is a good alternative as you describe, and cool that you found a cross-platform tool to do that, hadn’t heard of 7zip. Sending .dmg files on OSX might be overkill – remember I taught the one line Terminal command to zip and encrypt a single file or folder on OSX? Ok, I’ll let you keep going now!
In 413 Don Burr tells us he decided to set up his own personal VPN server rather than pay a commercial service he might use a few times a month. The highly reviewed Mac and iOS friendly WiTopia is as cheap as $4.16 a month. That brings an easy software install and many gateways in the US and around the world. A service, like WiTopia, adds to your privacy by masking your browsing behind the service’s IP address. That’s a lot different than a home VPN that links out using your own ISP and IP. LifeHacker.com VPN Review
Very cool you found an even less expensive VPN tool – but we wanted free and to have it in our own control. If you’re not up for the extreme geekiness of the home VPN solution, $4.16/month for WiTopia sounds pretty good.
I had WiTopia for years but recently let my subscription lapse. That’s because Google obsoleted most VPN security advantages when it implemented mandatory secure log ons and most web services followed Google’s example. You’re just as secure using Gmail or Google Drive or Google’s free Chrome Remote Desktop as you are using a VPN. (Google Implements HTTPS, HTTPS / Gmail, Secure Google Search, Chrome Remote Desktop Security)
Which doesn’t mean you are secure, because the big risk of using an open network is the hole opened by just connecting. If your system is vulnerable, it can be pwned as soon as it connects. Whether at Starbies or at work. Before you can access a secure website, or activate your VPN, ya’ hafta’ log on to the wide open WiFi network. (Just one Open WiFi Danger: the Evil Twin)
Ok George, I have to interrupt you again here. You had a cheap solution for VPN but you got rid of it because you had security on Google…but then you point out correctly that the rest of your system is vulnerable on open wifi networks.
Remember HTTPS provides end-to-end encryption so it is indeed safe on public wifi. In fact, HTTPS uses the same encryption most VPNs do, SSL/TLS. Now, this is only true if you ALWAYS go DIRECTLY to the HTTPS URL, and don’t go insecure first and wait to be redirected by the site. Also – for random browsing, you will not be on HTTPS for everything, so you are still at risk from malware injection as you read the WSJ etc.. It’s not just about protecting what you send out, but also about protecting the integrity of what you get in! The chances of someone pwning your system in the 5 seconds it takes to connect to VPN are incredibly small. The chances of being attacked when you’re on for 2 hours in a hotel are much much higher. Not using a VPN when on public wifi is like having those bad guys sitting on the couch next to you looking into your system. A free or paid VPN is the best protection you can get.
Several years ago I saw a demo of monitoring software that installed silently over a network and then captured and reported every keystroke, screen refresh, email, chat, and IP address. Similar software is now sold direct to the public. You can be sure Blackhats, FEEBS, and corporate security have even more powerful tools. (PCMag.com Reviews Monitoring Software, ManageEngine.com using the Firewall to Monitor Employees)
US law gives employees no right to privacy when using an employer’s computer or network. So connecting your iPad to your work WiFi on your lunch hour makes it and what you do fair game. Even your personal cell service could be connecting over an employer installed repeater you don’t know stands between you and Ma Bell. (PrivcayRights.org – Your rights at work, Kim Komando – Your smartphone at work, Wikipedia on Cellular Repeaters)
There’s some scary links in the shownotes which I hope you’ll check out. But maybe not at work, even if you have a VPN.
You’re right George that in the US companies have the right to see anything you’re doing on their network. In fact, one of the reasons I minimize what I do on the work network. Also keep in mind that a vast portion of our audience here is not in the US and from what I understand Europe has much more strict privacy policies than we do here. In any case, sitting at work, on the work network, just because the company has the right to sniff your traffic does not mean the can. If the traffic your’e sending is encrypted, it’s encrypted. They still have the right to try snoop, but it will be impossible! On work-provided devices they could install their own SSL certs, which can then be used to intercept SSL/TLS without triggering any sort of warning at all, but if it’s your devices, then the encryption holds, that’s the whole point of encryption – without the keys you can’t get in! The examples you give of non-SSL stuff being intercepted are true and all fair game, but all 100% irrelevant to HTTPS or VPNs.
I’m glad you recorded this George because I think we got deeper into understanding because of it and perhaps quash some misconceptions. Ok, enough about security, let’s have some fun. Back in January, we had the pleasure of hanging out with Kirschen Seah at Macworld and shortly after that she put a review into Dropbox for us – which I completely missed way back then! Well good news, she reminded me about it and we have it for you today.
AirStash from Wearable Review by Kirschen
Hi to all the NosillaCastaways! I’m Kirschen Seah from FreeRangeCoder.com and I’ll be reviewing the AirStash from Wearable. First off, what’s the problem to be solved? Well, you’ve decided to go without a Mac and carry only your trusty iPad or iPhone to a conference and someone says they’d like to give you a PDF to read and a Pages document to edit. You say, sure, just e-mail them to me. And they say, well, I have it here on my MacBook Air, do you have a USB flash drive? And you left your Mac at home… Or you have a carful of kids each wanting to watch different movies and TV shows on their iDevices, but they haven’t got the videos already stored on their devices, but you just happen to have the files on a handy secure digital card.
Now, with the AirStash, you can do all that, and more! The device is 3.5 inches long, an inch wide and half an inch thick, much like an oversized USB flash drive. It has a slot for a Secure Digital card on one end and a USB A plug on the other. You insert the SD card, which can be a regular SD, SDHC (high capacity), or SDXC (extended capacity) card, for up to a staggering 2TB of storage. The AirStash works like a regular USB flash drive using the SD card for data storage. When you insert it into your computer’s USB socket, it mounts like a regular USB drive.
The difference is that the AirStash is also a WiFi-enabled data storage device. The current model A02 supports 802.11b, g, and n over 2.4GHz, with WPA2 and WEP 128 bit protection. There’s a power button on the top of the AirStash. When this is pressed and held for 2 to 3 seconds, the status indicator turns green. Release the button and the status indicator will blink three times to indicate that the WiFi signal is on. The AirStash sets up its own network with a default name of “AirStash” and has a DHCP server to assign addresses to your devices. To turn off the AirStash, press and hold the power button until the status indicator blinks green three times rapidly, and then release the button.
So what network services does the AirStash support over WiFi? It comes with a web server so you can access the files on the device via the handy web address http://airstash.net via a regular web browser. You can even use the web browser to upload files to the device. There’s also a WebDAV server for computer, tablet, and phone apps which support that protocol – and there are quite a few, including OS X itself, Apple’s iWork suite for iOS, iThoughts, and GoodReader. And finally, the AirStash has a media streamer – if you have media files on the SD card which can be played from your computer or device, using something as simple as a web browser will let you pick the video or audio file and stream that from the AirStash. You can even load an SD card from your camera and then view the photos you just took, without needing to store them in iPhoto on the iPad for example.
Up to 8 devices may connect simultaneously to the AirStash. Simultaneous video streams can be supported for DVD quality standard definition video for up to three devices. The same limit applies also to audio streams, and AirStash’s support page indicates that it may be possible to stream to more than three devices but results may vary.
AirStash has also released a universal iOS app – which lets you browse and view files, as well as playback media files on the device. It even remembers where you left off last time. You can also use the app to configure the AirStash WiFi settings, such as network name (also known as SSID), network security passwords, and more. There’s also a corresponding app on the Android store.
The AirStash is charged much in the same way as any iPhone or similar smart device – just plug it into a USB charger, such as the iPhone, iPad, or even 12V car USB adapter and wait a couple of hours. You can even use a powered USB hub or one which is attached to a computer. The status indicator will flash yellow while it’s charging and will turn off when it’s fully charged. One charge is good for 7 hours of WiFi operation. If you plug it into a USB charger, you can continue to use the WiFi features, but plugging it into a USB hub will only allow the AirStash to charge and be used as a USB flash drive.
Now for the price. An AirStash costs $130 with an 8GB SDHC card and $140 with a 16GB card on Amazon. I opted for the 8GB model since I could get a larger capacity card. There are other WiFi enabled devices out there but the AirStash is the only one which uses SD cards for data storage, thus providing quite a bit of flexibility for media swapping. If you do decide to get one, do remember to use Allison’s Amazon affiliate link! (8GB AirStash, http://www.airstash.com/)
Once again, this is Kirschen from FreeRangeCoder.com and I’ll see you in the bitstream.
Wow Kirschen – this is even cooler than I realized when you told us about it while we ate those yummy falafels across the street from the Moscone center. The good news is that the price has dropped – the 8GB is only $117 at Amazon right now and the 16GB is only $140. I’ve been wanting something like this ever since I reviewed the Apotop device that was supposed to do this but was cludgy and slow. The problem it solves for me is that I want to take GOOD photos on my DSLR but I want the fun of being able to tweet them quickly instead of waiting till I get back to my computer. I know I can use the camera connection kit to pull them into my iPad but for some reason I never think to do that and I’m pretty sure that won’t let me selectively browse to just grab one or two photos the way the AirStash does. Having it work to stream video too is ultra cool as a bonus! Very cool pick and great review as always, keep them coming! next time I won’t wait 3 months to play it, I promise!
Howard and his backups at the Apple Store
I’ve started to think maybe I’m one of the crazy ones now, sucked into Katie Floyd’s madness. I have a USB full backup at home, another one at work, and then of course CrashPlan for cloud backups. She’s a good influence I suppose? I guess I never did finish the story on what I think of CrashPlan, did I? After 3 and a half weeks, my 300GB of data was finally up in the cloud and backing up to CrashPlan. Early on in that time period I started backing up Steve’s Macbook Air which has less far less data on it (since his heavy lifting is on his iMac that Kevin (big_in_va) made me buy for him).
Things went swimmingly until one day I got an alert from CrashPlan that his device hadn’t backed up in 3 days. I learned how to resume the backups, restart the backups and reconnect to their servers using a handy little command line tool they give you but I could not get his Mac to reconnect to their servers. I shot off a support request and after 3 days hadn’t heard back.
I tweeted out a complaint about this to CrashPlan and they got back to me right away and helped me connect to the right people. Don’t know how it didn’t work the first time but at least I had people helping me. The bad news was that they suggested I just start the backups over from scratch. I didn’t like that solution since if that were to ever happen on MY system it would be a disaster. Instead I argued with them back and forth for several days, and one day his mac was able to connect to their servers again. I wasn’t very happy with their service and when I got the opportunity to fill out a survey, it was scathing. I was rewarded with a bonus month or two of CrashPlan service, which was nice but still left me queasy about a critical, paid-for service.
Fast forward to this week. I’ve been happily getting notices every week or so telling me how our backups are doing, all showing 100% and the size of the backup, until I got one warning me that my Mac hadn’t backed up in 3 days. Yikes, not this again! I did the reconnect, restart, resume dance again and they wouldn’t start back up. Then I went into their logging tool and noticed that exactly 3 days ago, they updated the software and that’s when the backups stopped.
Shot an email off to support at CrashPlan, and within about 45 minutes my new little friend Marc got back to me. We went back and forth a few times, and even though at one point he misunderstood and thought the problem was on my end, after about 5 email exchanges, he discovered a misconfigured setting on their end from the upgrade and I was able to restart my backups.
So I now have 2 datapoints on CrashPlan’s tech support – one dreadful and one fantastic. I’m hoping the first one was an aberration and from talking to my backup-fanatic friends I think it is. In any case, it makes me super happy knowing that I’m backed up in three places.
There’s a reason I’m telling you this story right now though. Steve and I were at the mall, and as one does, we stopped by the Apple Store for no reason. While goofing around we met a nice gentleman named Howard who told us a story of tragedy and triumph on his backups.
Howard is a smart man, he has two backups, one on site and one offsite. Unfortunately he was burgled, and since he had just run his backup, his external drive was still connected to his Macbook when the robbers stole it from his home. For most people this would be tragic because most people have between 0 and 1 backup. For Howard though, the loss of the device was bad but at least he knew his data was safe because of his offsite backup.
Except. When he got a new Mac and plugged in that backup, the drive was dead. Again with the tragedy. He took the drive around to places like MacMall and they all wanted to charge him an arm and a leg, and with no promise of any data recovery. Undaunted, Howard looked for a solution. He found a place called LA Laptop Repair who said they’d look at it and see if they could repair it for $89. They even said that if they couldn’t figure out what was wrong that he’d get his $89 back. And the triumph of the story is that it was only a bad power supply on the case! So Howard was happy and got his data back for only $89.
Now I have to say I’m not feeling like a backup nutjob any more, because with THREE backups Howard would have been fine, right? Another lesson to keep in mind is what Katie always preaches – CHECK your backups periodically to make sure they’r still working. I’m happy for Howard though and if you’re in the LA area, keep LA Laptop Repair in mind for emergencies.
Ken Wolf reviews Buffer
Hi Allison, this is Ken Wolf from Manhattan Repertory Theatre with a review of a web app that I absolutely love. But first, let’s start with the problem that needs to be solved.
Just recently at Manhattan Rep, we decided to jump into the Social Media arena full force to try to promote some of the plays that we do here and also to bring in new producers into our theatre. So I started posting passionately to our Twitter account and to our Facebook account, but to be honest Allison I just didn’t have the time to be tweeting and posting all day. It made me nuts. I have too many important things to do and the problem with Twitter and Facebook is that it is all kind of real time, especially Twitter – it’s real time, so I have to post all the time if I am going to connect to people because otherwise it goes away.
BUFFER was the solution at BufferApp.com. Buffer is a web service that automatically posts to your Twitter, Facebook and Linked in accounts. AND with Buffer you can automatically schedule WHEN your tweets and posts will be posted. Here is how it works. You log into your Buffer account using your Twitter, Facebook or Linked in login.
You then, pre-place your tweets and posts in THE BUFFER, and then you go and schedule when you would like to have them be tweeted or posted. You can set up a series of times to post everyday, or you can set up different posting times for every day of the week. You can attach pictures and links just like any other Twitter or Facebook client. It is super easy to do and super fun.
It is free for up to 10 posts a day, but I chose to go with the AWESOME PLAN, where for $10 a month you can schedule as many tweets, Linked in posts or Facebook posts as your heart desires.
It is just a beautiful solution to our Real Time problem. Now, usually on Sunday night, I create my Twitter and Facebook posts FOR THE ENTIRE WEEK and I do 9 a day! So I pre schedule 63 posts to both Twitter and Facebook. And I am done for the week!!
Also they have a Buffer iPhone app so I can add on the spot Tweets to my BUFFER from anywhere. And it works great. The web interface is fun because you can drag and move your Tweets up and down your Buffer to change the order, and it works really well. They also have really cool analytics feature which I really don’t fully understand. It shows each Tweet and if it was Retweeted or Favorited and then it shows a number in something called POTENTIAL. I have no idea what this number means but it LOOKS official and important. And the analytics go all the way back to when I first began with this service in February. It is just crazy fun.
The only problem I had with it, was Facebook once burped and refused to accept my posts. Buffer app then told me to try and post less, so I did, brought it down to 9 a day and it worked. I have no idea why, because I didn’t know Facebook limited posts but maybe it does limits posts from automated apps like this I have no idea. And I did have one problem when Twitter failed, but it was because Twitter failed, not because Buffer didn’t post.
So if you need a way to automatic some or all of your Social Media info, check out Buffer. My Twitter handle at Manhattan Rep is @ManhattanRep. I tweet out motivational tweets about creativity, acting, directing, and LIFE, and then throw in a few promotional tweets. Please check it out. Allison and Steve…. Have the happiest of Happy Birthdays!
Thank you so much Ken we did have happy birthdays! Buffer sounds really cool. What I like is that you’re using it for good and not evil. Seems like it would be easy to be spammy with it but you’re not. You’re doing thoughtful tweets, you’re just writing them all at once and having them spit out over time. I struggle with what time and day to announce things too – if I do it first thing in the am for me, it’s the middle of the night for New Zealand and they might miss all my wit and wisdom. Thanks for the review and the great ideas.
Clarify in the MacHeist Bundle
 I hope you’re listening to this very early in the week, because I wanted to tell you about the latest MacHeist bundle which only has 2 days left as of Sunday. This might be the best bundle I’ve ever seen – first because it’s a mini-bundle with 10 apps for $10. Secondly Clarify from BlueMango Learning is in the bundle! Clarify is normally $30 all by itself, so this is a steal even if it only had Clarify in the deal. The other apps that caught my fancy were Path Finder which I’ve been meaning to buy for about 5 years now and somehow never seemed to get around to it. The MacHeist mini bundle also includes AirServer, which is a lot like Reflector that I use that lets you view on your Mac whatever you have on your iOS device via AirPlay. There are so many uses for that – if you want to demo something from your phone onto a projector, or via a screenshare, this is a great tool, or you can even do a screencast of an iOS app using something like Screenflow to capture your screen while AirServer sends the iOS screen to your Mac. iStopMotion from Boinx is in the mini-bundle and I’ve heard a ton of great stuff about Fantastical, a new calendaring app for the Mac I’ve been meaning to try.
I hope you’re listening to this very early in the week, because I wanted to tell you about the latest MacHeist bundle which only has 2 days left as of Sunday. This might be the best bundle I’ve ever seen – first because it’s a mini-bundle with 10 apps for $10. Secondly Clarify from BlueMango Learning is in the bundle! Clarify is normally $30 all by itself, so this is a steal even if it only had Clarify in the deal. The other apps that caught my fancy were Path Finder which I’ve been meaning to buy for about 5 years now and somehow never seemed to get around to it. The MacHeist mini bundle also includes AirServer, which is a lot like Reflector that I use that lets you view on your Mac whatever you have on your iOS device via AirPlay. There are so many uses for that – if you want to demo something from your phone onto a projector, or via a screenshare, this is a great tool, or you can even do a screencast of an iOS app using something like Screenflow to capture your screen while AirServer sends the iOS screen to your Mac. iStopMotion from Boinx is in the mini-bundle and I’ve heard a ton of great stuff about Fantastical, a new calendaring app for the Mac I’ve been meaning to try.
There’s even more in this bundle than we have time to talk about but rush over to macheist.com and get it for $10, enjoy Clarify and then see what the other apps do! Lots of NosillaCastaways have tweeted me that they did it this week!
Chit Chat Across the Pond
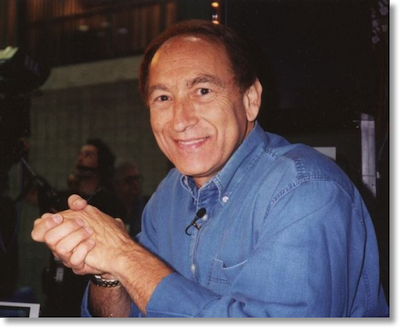 In Chit Chat Across the Pond we’ve got Stewart Cheifet, host of the Computer Chronicles and Net Cafe that were on the air from the 80s till 2002. These shows are on the Internet Archive at archive.org/details/computerchronicles and archive.org/details/netcafe. Here’s the outline of the conversation that at least I MEANT to follow:
In Chit Chat Across the Pond we’ve got Stewart Cheifet, host of the Computer Chronicles and Net Cafe that were on the air from the 80s till 2002. These shows are on the Internet Archive at archive.org/details/computerchronicles and archive.org/details/netcafe. Here’s the outline of the conversation that at least I MEANT to follow:
- How did shows of such intelligence actually survive on mainstream TV?
- Curious that I never actually heard of them – I would have loved them
You can find Stewart at cheifet.com, on Twitter at @cheifet, on Facebook at Cheifet.
So do I have to have Stewart back again or what? I found him fascinating and I really want to hear more of his great stories. I got off of Skype with him and instantly called Steve to tell him what a great time I had. I know, I know, I say that a lot, but I really did love learning from him and hope to get involved in some of the stuff he’s doing now.
That’s going to wind this up for this week, don’t forget to go over to macheist.com and buy Clarify from BlueMango Learning in the mini-bundle for only $10. Don’t forget to send in your Dumb Questions, comments and suggestions by emailing me at [email protected], follow me on twitter at @podfeet. Check out the NosillaCast Google Plus Community too – lots of fun over there! If you want to join in the fun of the live show, head on over to podfeet.com/live on Sunday nights at 5pm Pacific Time and join the friendly and enthusiastic NosillaCastaways. Thanks for listening, and stay subscribed.

I did in fact link to Tunnelblick in my show notes for the VPN episode. When I was putting together my DIY VPN setup, it was the first app I tried, my desire being to see just how much mileage I could get using just free/Open Source tools. However I had no end of trouble with it. The darn thing just would not connect, both on my two physical machines (desktop and laptop) as well as any number of test virtual machines I set up. I quite literally pulled an all-nighter trying to get it to work, with no avail. I consulted Google during this ordeal and found tons of people for whom Tunnelblick was working perfectly, but I also found tons of people who, like me, were having loads of trouble getting it going, or, if by some miracle they did get it to connect, they had stability issues with it. By then I had long passed the “enough is enough” point and paid the $10 for Viscosity. I really should have given up sooner, as I had long ago passed what I call the “just man up and pay for it” point: the point at which what I would normally earn (my usual hourly rate) during the time I spend on a project exceeds the cost of the paid-for/commercial equivalent times two. I don’t mean to malign Tunnelblick in any way; it is a great app. (I do think Viscosity has a better user interface than Tunnelblick, but that is my own personal opinion and your mileage may vary.) And everyone who is interested in doing the VPN thing should check it out. Just remember, if things don’t work right away, don’t do the pig-headed thing like I did and plow ahead spending hours on something that eventually proved futile.
I’m responding here to Allison’s comments as she disassembled my audio contribution in this show, #415 April 21, 2013
I try to keep my audio to about three minutes, and provide links to explain what that doesn’t give me time to clarify. PLEASE GO READ THE LINKS IN “MY” TEXT ABOVE.
I’m breaking my responses to Allison into separate posts, organized by topic.
—
# 1 – ENCRYPTED EMAIL
Setting up encrypted email as described by Bart in #412 proved troublesome for some.
John (NASANut in Chat) who did get it set up on his Mac reported “most of the Windows users at Work can’t see and open the (encrypted) attachment.”
While I might be able to set up encryption among the Macs I “control,” I can’t easily reach out and do it on my nephew’s in New Hampshire, or my sister’s Windows PC in Seattle, and certainly not on “my” lawyers PC in a big law firm with its own IT staff.
Then there’s serious limitations in StartSSL’s free certificates.
1. Not for commercial use (so not for business)
2. Not good enough for relaying “sensitive information.”
What’s the point, if it’s not good enough to send “sensitive information?”
http://www.startssl.com/policy.pdf
Which is why I personally prefer encrypted DMG or 7-zip. They meet the highest of Steve Gibson’s “Trust No One” security. They’re free, non-expiring, and with good passwords, well suited for sending sensitive information.
#3 – PWNED ON CONNECTION
Allison:
“In fact, HTTPS uses the same encryption most VPNs do, SSL/TLS. Now, this is only true if you ALWAYS go DIRECTLY to the HTTPS URL, and don’t go insecure first and wait to be redirected by the site . . . ”
—-
Which is the main point I was trying to make.
You can’t go direct to HTTPS or VPN when you connect to an open network, or to a network you don’t control yourself.
A “man in the middle attack” can intercept your HTTPS connection. Or your VPN connection. BEFORE THEY’RE ENABLED.
I sent Allison this link on Friday, but she had already completed editing the show notes and wasn’t able to include it:
Vic Hargrave, of Trend Micro, writes that VPNs and SSL sites are both vulnerable in his post:
“What Are Man-in-the-Middle Attacks and How Can I Protect Myself From Them?”
http://fearlessweb.trendmicro.com/2012/tips-and-tricks/what-are-man-in-the-middle-attacks-and-how-can-i-protect-myself-from-them/
#4 – PWNED on CONNECTION part 2
Allison:
“The chances of someone pwning your system in the 5 seconds it takes to connect to VPN are incredibly small.”
———–
This HAK 5 two video set demos the widely available “Pineapple” WiFi hacking tool and SSLStrip application intercepting and pwning SSL log ons and passwords:
#5 – BACK to WORK
Allison on the “safety” of your encrypted traffic at work:
“Allison
“If the traffic you’re sending is encrypted, it’s encrypted. They still have the right to try snoop, but it will be impossible!”
—————–
See the comment above in which HAK 5 demos how easy it is for a black hat to steal your HTTPS / SSL password.
If a hacker, the FEEBS, or corporate IT have your logon and password, they don’t need to “break” encryption to read your traffic.
It should, in fact, be easier for corporate IT to snag your device if you log it onto a corporate network than for a hacker at Starbies. It is their network . . .
Then there’s simple tracking of your activity on the corporate network. Even if IT isn’t able to read your encrypted traffic, they will know to what IP addresses you connect, when, and for how long.
Happy computing?
#2 – DMG ENCRYPTION IS OVERKILL?
[ sorry, posted this twice, but it didn’t take. trying again without active links ]
Allison:
“Sending .DMG files on OSX might be overkill — remember I taught the one line Terminal command to zip and encrypt a file or folder on OS X?”
———————–
In an Apple Discussion Post about Apple’s Zip – E encryption, Thomas A. Reed wrote:
“”Zip uses the PKZIP algorithm, which is extremely insecure at this point. Information about how to crack it is all over the Internet.”
Here’s what Wikipedia says about that:
“tQuoting Allison:
“Sending .dmg files on OSX might be overkill – remember I taught the one line Terminal command to zip and encrypt a single file or folder on OSX?”
I’ll just quote this from Thomas A. Reed in Apple’s Forums about the ” zip-e ” method in Terminal:
“Zip uses the PKZIP algorithm, which is extremely insecure at this point. Information about how to crack it is all over the Internet.”
Here’s what Wikipedia says about that:
“.ZIP supports a simple password-based symmetric encryption system which is documented in the .ZIP specification, and known to be seriously flawed. In particular it is vulnerable to known-plaintext attacks which are in some cases made worse by poor implementations of random number generators.”
Could Apple have silently upgraded the built-in “zip – e ” to be more secure than it’s ancient legacy in PKZIP? Don’t know.
But I do know that 7-zip used by Keka is 256 bit AES and Disk Utility offers a choice between 128 and 256 bit AES when encrypting DMG files.
So, are you going to rely on an email encryption certificate its provider says not to use for “sensitive information,” Apple’s “Terminal zip -e” that may generate inherently weak zip encryption, or the state of the art encryption of 7-zip and DMG?
[In full disclosure, StartSSL.com offers PAID certificates it says are adequate for sending sensitive data]
#1 not sure what you’re arguing here George. Never said any of this was easy or that you’d be able to convince or teach other people to secure their email. This talk was for personal use, we didn’t tell you to use it for business.
#2 I also said that Bart told me recently that there are problems with the regular zip encryption. The overkill statement was because you’re always sending a large volume even if what you have to send is a few kb. I wasn’t saying it was too much encryption.
#3 & 4 the Man in the Middle attacks when you’re using SSL/TLS are avoidable if you type in https first, as I said. Here’s a good and simple explanation on how SSLStripper works (they say in there that MITM attacks don’t work if you type in https): http://mason.gmu.edu/~msherif/isa564/projects/sslstrip2.pdf
I watched all 19 minutes of that video and he never showed anything about being able to intercept your traffic if you were on a VPN.
#5 Again you’re arguing something I didn’t say – I told you that I do not use my work network to do play stuff. ABSOLUTELY they can track what you do on their network and in the US they have the legal right to do it if you’re using their devices. They can keylog you all day long. However, if you’re on your device using a VPN, once you’re in, you’re secure.
1. I’d like to think we’re discussing and sharing how to be safer on the ‘net, not arguing.
John (NASANut) reported setting the encrypted email to use at work. That’s what I would have done with it, used it to share files over email among our employees, bankers, brokers, and my board of directors.
But let’s say you want to securely email your PERSONAL financial data in your “retirement” folder to your financial advisor. According to the terms of the StartSSL.com site, you should not rely on their free certificates to make that email secure. Maybe it’s just lawyer CYA. Maybe the resulting encryption is not adequate. If a web security service tells me not to rely on its security, I’m going to take them at their word.
The tips and tricks Bart introduced will work with the paid service StartSSL does stand behind. It is always good to learn how to do things. It is also good to be aware of limitations, especially when security of data is at risk.
2. I just did a test on a folder with 22.2 MB holding 5 books in .txt downloaded from Project Gutenberg. total
Straight, unencrypted, Apple “compression” zip = 7.03 mb
128 bit AES DMG = 9.04 MB
Keka 7-zip 256 bit AES set to normal compression with enclosed file names encrypted = 1.06 MB
3. The PDF you linked from George Mason University is excellent. The give away that you’re subject to a “Man in the Middle Attack” is the lack of the S on HTTP in your log on. Yet I can only refer to the first statement I made, you’re as safe connected to an Secure Web Service (like Gmail, or iCloud) as on a VPN.
The problem is GETTING CONNECTED.
I rely on the comment Trend Micro’s Vic Hargrave who wrote:
“To decrypt HTTPS and VPN, a man-in-the-middle attacker would have to obtain the keys used to encrypt the network traffic which is difficult, but not impossible to do.”
I’ve not done it. I have no interest in spending my retirement in Leavenworth. But I believe the techniques are the much same, whether the “Man in the Middle” is attacking a VPN or HTTPS.
Not that it is conclusory, but a Google Search on term “crack VPN password” coughed up 3.6 million results, leading off with “Cisco VPN client password cracker.”
#5. Again, if “they” can crack HTTPS or VPN secure passwords, “they” can watch what a hypothetical user is doing. Can “they” crack your personal gear? My bet is that “they” can, if it connects to “their” network and they want to badly enough to trick your system by DNS redirection, false certificates, or other techniques I can only imagine.
And the whole point of keyloggers is if “they” can implant one on a user’s device, “they” can duplicate everything the user does.
In the end, all I’ve been trying to say is that SSL websites and encrypted VPNs offer much the “security,” and suffer the same potential vulnerabilities.
Want to run all your “remote” computer activity through a computer back at home?
Set up a personal VPN.
Use Chrome’s Remote Desktop Extension.
Pretty much the same security end result.
I’m a bold boy and only getting around to listening to the show now.
First – I need to make a correction – Allison said I said that when the cert expires you can’t read the encrypted emails anymore – this is not so. What I said was that you need to keep your old certs in your keychain to continue to be able to read old encrypted email. As long as you have the certs, they will work for reading email. If you try use them to send new email to to sign new email they will “work” in that the encryption will happen, but, the receiver will get a warning that the cert is not valid.
Now – on to George’s point that because some Windows users are having trouble S/MIME is a Mac only thing. This week I had a Windows user have trouble opening a PDF, does that mean PDFs are Mac only? I’d wager that if you looked at the mail clients using S/MIME on any give day, you’d see a heck of a lot more Outlook than Mail.app. S/MIME is very common in big business, and that is very much Windows land.
So, why are people having trouble? Because all encryption is hard. S/MIME is by no means the hardest though. Your other options are PGP which is also no cake-walk, and encrypted &Zip or RAR files which also confuse recipients because they have to go get software that can open those formats. Right now there exists NO method of sending encrypted content that is frictionless.
Finally on the email front, I suggested StartSSL as AN OPTION. That is all it is AN OPTION, S/MIME is in NO WAY limited to that one free CA. You can get S/MIME certs from any provider you like, with any key-length you desire. Also, they key lengths from StartSSL are more than adequate for protection against realistic threats today. Yes, if you throw the resources of a three letter acronym government player at it they could break in, but you have to balance the value of what you send against the resources needed to break in. Nothing I send is worth the kind of effort needed to break Start SSL’s 2048bit keys. Do you have lasers guarding your house? No? Well, you do know that regular locks are useless against tanks right? StartSSL’s certs don’t give Fort Knox level security, but, I doubt any of our listeners need that for their personal emails! If you are running a business you should buy your certs and match the price you are willing to pay against the value of what you are sending.
One final final point – 7Zip does indeed seem to provide good security, but it is symmetric encryption, so you have no choice but to introduce a vulnerability by sending someone the password. It could get snagged in transit, and, you have to trust the person on the other end not to be careless with it. The nice thing about public key crypto is there is no need to send a secret key between the communicating parties – an exchange of PUBLIC certs is all you need. Granted, assuming you send the password out of band you are probably fine, but, no more probably than when I use my S/MIME cert from StartSSL, you can’t send that password in a way the feds can’t get it if they really try!
George – you could not be more wrong when you say this – “A “man in the middle attack” can intercept your HTTPS connection. Or your VPN connection. BEFORE THEY’RE ENABLED.”
SSL (and HTTPS) are designed EXPLICITLY to SET UP A SECURE CONNECTION IN THE PRESENCE OF A MITM. That is “the big deal” about public key crypto. That is why it is possible for the internet to work at all!
SSL Strip is very clever, but it does not break SSL connections, it works because most people just type a plain URL into their browsers, so the session STARTS in plain text, what would normally happen then is that the SERVER replies with a redirect asking the client to switch to HTTPS, but the server HAS to respond on the connection the client made, which is NOT encrypted. SSL Strip can worm it’s way in at that point and PREVENT the hand-off from HTTP to HTTPS.
If you go DIRECTLY to HTTPS, SSL Strip is powerless.
Similarly, IF, and only IF, you have your SSL VPN properly configured with properly signed certs, SSLStrip has no way in. If you just blindly accept certificate warnings then yes, you are vulnerable to MITMs, not because SSL is broken (it did warn you remember), but because you are not using it right.
SSL is not perfect, but it is not nearly as broken as your post erroneously states. The core weakness is in the CA system where too many organisations have the power to sign certs without enough safe-guards. ATM we are dealing with this quite effectively by revoking any bad certs found.
If SSL were really broken like you say, then all internet commerce would be over.
Bart.
Hey, Bart, good to hear from you.
Ah, anyway.
I was not the person who said Cert. Encryption didn’t work on Windows. No blame to him but it was John (NASANut) who reported he couldn’t get it to work after it did on his Mac.
No question, Microsoft’s world dominating email systems work with encryption certificates.
What I was doing was leveraging John’s experience to shorthand a statement that anything that troublesome to set up is not something I could get someone e.g., my sister in Seattle on her Windows PC or my my 80+ year old Board of Director’s member to set up or use.
But while we hand deliver paper to the Director I mentioned, I was able to walk my sister through setting up 7-Zip so I could send her some confidential family contracts. And while we were doing the setup, I gave her the password over the phone (a separate channel).
So, yes, no matter how good 7-Zip is, the sender and receiver still have the problem of exchanging the keys (password).
Is there anything wrong with certificate based email encryption?
Nope, presuming you can get it set up on both ends, and you buy a StartSSL certificate they stand behind instead of relying on the free one they warn should not be used to send “sensitive information” or for business or commercial use.
I just find encrypted DMG and/or 7-Zip easier . . .
Then the other point I was trying to make that I think has been completely misunderstood.
I am not saying SSL is “broken.”
I am not saying properly connected encrypted VPNs are ineffective.
But I am saying that there’s no difference in your security if you’re properly connected to an SSL site like Google’s many services or a properly set up VPN.
Here’s what you say,”If you go DIRECTLY to HTTPS, SSL Strip is powerless.”
We’re in 100% agreement.
Here’s what I say, “You can’t go DIRECTLY to HTTPS” when you log on to ATT WiFi at Starbucks.”
Which is the point of vulnerability.
Same at work . . .
As to the personal VPN recommended by Don, it is interesting. But if SSL encryption is “secure,” then I don’t see the VPN offers an advantage over the Chrome Remote Desktop Extension which is a lot less hassle to set up.
You’re “phoning home” over a secure connection either way, then using the gear you left running there to re-route your internet activity through that gear.
I’ve also been (quietly) concerned that listeners who keep hearing the message that neither bad guys nor corporate IT s can snoop on your connection if you use a VPN could be in for a rude surprise when security shows up with a cardboard box, final paycheck, and a log of what they’ve been doing.
Even if IT can’t intercept or crack the VPN, having it up and running will leave connection logs in the servers. I’d bet you (Bart) could fill us in on just what tracks even an encrypted VPN connection would leave on network logs.
Quoting:
“Well on May 28th, I did look at various websites throughout the day and my boss went back and researched what sites I had looked at and printed them out for me to look at and then let me go.”
George
I personally do not advocate the use of VPNs to hide your traffic from corporate IT personnel; I merely put it down in my notes as a possible reason why someone might want to set up a VPN. Ultimately it is up to the end user to decide what he/she wants to do, and to weigh the risks, deal with the consequences, etc.
Yes, you are correct, if you type in HTTPS to go directly to a website, you are safe. But not all websites are coded correctly, sometimes they drop you back to HTTP, or they don’t have HTTPS login pages. (Fortunately this is becoming less of a problem as webmasters become more aware of the threats out there)
But HTTPS doesn’t protect your traffic once it reaches the hotspot. If an unsavory type were to install a tap at the coffee house’s Internet connection,
Your traffic is encrypted as it goes over the local Wifi (so other patrons can’t read your traffic), but once it gets past the wifi access point, it’s open to anyone who has installed a tap there. (This has been known to happen) There are also devices that basically advertise themselves as rogue access points. (Do a google for “wifi pineapple” for example) And while the chance of this happening is small, it is not insignificant.
In any case the reason why I choose to VPN whenever I am on a public network is ultimately peace of mind, a “belt and suspenders” mentality if you will. It didn’t take me that much (both in terms of time and money) to set up, is very easy to use (basically one click), and it adds an additional layer of security.
Gah… didn’t realize that I hadn’t finished a sentence when I posted that. But I think you can figure out where I’m going with that.
Ok, we’re all agreed that surfing on your company’s network to do non-essential work stuff is simply not a good idea. No one has said that it is. No one said we should use VPNs to hide such traffic from our employwers. Still can’t figure out why anyone thinks that any of us have said that!
Allison –
Because Donald Burr said it in # 413
“To work around government- or corporate-mandated Internet censorship/site blocking.”
And, again, right above your latest:
“I personally do not advocate the use of VPNs to hide your traffic from corporate IT personnel; I merely put it down in my notes as a possible reason why someone might want to set up a VPN.”
He then continued:
“Ultimately it is up to the end user to decide what he/she wants to do, and to weigh the risks, deal with the consequences, etc.”
I disagree. “We” have a responsibility to the new and naive who don’t know there are risks, much less possible consequences.
There’s a great old Johnny Cash song, “Don’t Take Your Guns to Town” about a young kid named Billy Joe who disregarded his mother’s advice and did just that.
At least he was warned . .
George,
OK. You’re right. I should have said that, should you choose to set up a VPN to get around corporate restrictions, then you run the risk of disciplinary action, blah blah blah. One would have thought that that would be common sense (not to mention blatantly obvious), especially to the more technically minded types who listen to this show. Fine, whatever. With these responses (which maybe Allison should summarize and amend to the original show notes, I dunno, that’s up to her) everyone should consider themselves officially warned.
Now can we PLEASE get back to our regularly scheduled geeking out?