Followups
- The Reply All podcast released an episode about the Momo panic mentioned on the previous Security Bits — overcast.fm/…
Security Medium — Facebook Accidentally Store Passwords in Plain Text Since 2012
Brian Krebs broke this story, and sourced it from “a senior Facebook employee who is familiar with the investigation and who spoke on condition of anonymity because they were not authorized to speak to the press”.
What Krebs reports is that an internal Facebook audit found that poorly written apps logged plain-text passwords into some kind of searchable logs. These logs was theoretically accessible by “thousands” of Facebook employees.
The investigation is on-going, but Facebook have now admitted that they did log plain-text passwords for hundreds of thousands of users, and did so since at least 2012.
Facebook have found no evidence that any of their employees ever abused these passwords, or, that they were ever compromised by outside hackers of any kind. But, audit logs show that approximately 2,000 engineers ran approximately 9 million queries which produced results that contained plain text passwords.
Facebook have promised to contact users they know for sure were affected, but they will not be forcing and password resets. In their official response to Krebs Facebook said it expects to notify “hundreds of millions of Facebook Lite users, tens of millions of other Facebook users, and tens of thousands of Instagram users”.
If you trust that no Facebook employee ever abused this treasure-trove of data, then you don’t need to take any action. If, on the other hand, you have a Facebook account and believe there could easily be one or more proverbial bad apples on staff in Facebook, it would make sense to change your Facebook password ASAP. What’s a little more annoying is that you should not just change your current password on Facebook. Any password you’ve ever used on Facebook and then re-used anywhere else needs to be updated everywhere.
If you’ve been putting off getting a password manager, this might be an opportune moment to finally give in and accept the inevitable!
Links:
- Brian Krebs’ Original Reporting — krebsonsecurity.com/…
- Facebook’s official response (Orwellianly titled ‘Keeping Passwords Secure’) — newsroom.fb.com/…
- Change your Facebook password now! — nakedsecurity.sophos.com/…
- Hundreds of Millions of Facebook Passwords Were Stored as Plain Text. For Years. — www.macobserver.com/…
- Facebook exposed up to 600 million user passwords to its employees — www.imore.com/…
Notable Security Updates
- Patch Tuesday has been and gone and Microsoft have released patches for Windows, IE, Edge, Office & Sharepoint, including fixes for two zero-day bugs — krebsonsecurity.com/… & nakedsecurity.sophos.com/…
- Windows 7 users received a patch that presented them with a message warning them that there will be no more patches for Windows 7 after it reaches end-of-life next January — nakedsecurity.sophos.com/…
- Adobe have released security updates for Photoshop CC & Adobe Digital Editions — www.us-cert.gov/…
- WordPress 5.1.1 patches a critical bug that could allow complete site takeover — www.us-cert.gov/… & nakedsecurity.sophos.com/…
- Chrome 73 patches a number of vulnerabilities, and adds the ability to default to searching with DuckDuckGo — nakedsecurity.sophos.com/…
- FireFox 66 patched a number of vulnerabilities, and adds video auto-play blocking — www.theverge.com/…
- FireFox 66.0.1 has since been released to address three critical vulnerabilities — www.mozilla.org/…
Notable News
- Windows users, beware
.regfiles, a security researcher has found a way to alter the warning dialogue content, including the text within the buttons by simply including some special characters in the filename. This literally allows an attacker to turn the button to back out of the registry changes into the one to accept them! What’s worse is that Microsoft have no plans to fix this issue ATM — nakedsecurity.sophos.com/… - Security Researchers have found a way of extracting Microsoft Bit Locker encryption keys when the full-disk encryption software is configured in its least-secure configuration. Microsoft were already advising against this configuration, and the attack involves creating some custom hardware to intercept the key as it moves across busses within the computer, so, for now at least, this attack is only likely to affect high-value targets — nakedsecurity.sophos.com/…
- Security researchers have found two zero-day exploits against Safari, one which allows complete take-over of a Mac simply by tricking the victim into visiting a malicious URL. Thankfully both came to light in a hacking contest run by the Zero Day Initiative (ZDI), so they have been responsibly disclosed to Apple, and details have not been published — 9to5mac.com/…
- Google Hit With $1.69 billion EU Anti-Trust Fine Over Adsense Restrictions — www.macobserver.com/…
- Google have released details of some privacy improvements that will be included in Android Q (the next major Android release which is scheduled for this summer). The most notable is a switch to iOS-style control over location data (three choices for each apps: when using the app, always, or never). Android Q will also curtail access to device identifiers being abused by app for tracking users against their will, and greatly improve the security of app data stored on SSD cards — nakedsecurity.sophos.com/…
- Microsoft worked with Google’s Project Zero team for over a year to get to the bottom of a whole new class of Windows security vulnerability. Thankfully, after all that work they found there are no currently usable exploits, and, they have developed improvements to Windows 10 that will harden the OS against this new class of problem. The improvements will be included in the 1903 Spring Update for Windows 10. Microsoft are also recommending that driver vendors similarly harden their code. It’s notable that Google chose not to publish details of this vulnerability after its usual 90 day window — arstechnica.com/… & nakedsecurity.sophos.com/…
- Microsoft is re-branding its Windows Defender AV offerings as Microsoft Defender because it is bringing its enterprise AV offering to the Mac as part of it’s Advanced Threat Protection (ATM) suite. The software is only available as a preview ATM, but will launch soon — arstechnica.com/… & www.macobserver.com/…
- The pro-privacy social media site MeWe has reached 4M members — www.macobserver.com/…
- Editorial by Bart: I’ve done a little digging, and they are a for-profit company based on a freemium model (very much like Slack, the premium products are aimed more at enterprises than home users).
- DARPA Is Building a $10 Million, Open Source, Secure Voting System — motherboard.vice.com/…
- Mozilla have released Firefox Send (send.firefox.com), a new and easy to use tool for securely sharing files — www.wired.com/…
Suggested Reading
- PSAs, Tips & Advice
- ⭐️ There is currently a malware campaign on-going trying to extort users with fake emails claiming to be form corrupt CIA agents offering to help you destroy evidence of child pornography on your devices. Don’t fall for it!
- ⭐️ Two-thirds of all Android antivirus apps are frauds — www.zdnet.com/…
- ⭐️ 🇺🇸 The FTC is warning that phone-based tax scams have increased nearly 20 fold since 2017 — nakedsecurity.sophos.com/…
- ⭐️ 🇺🇸 Based on reporting by Brian Krebs, US citizens who have existing credit freezes with Equifax should probably sign up to their new My Equifax portal before someone impersonating them does so instead — krebsonsecurity.com/…
- Notable Breaches & Privacy Violations
- ⭐️ Email verification company Verifications.io leaked hundreds of GB of data though an unsecured MongoDB database. Initial reports put the breach at ‘just’ 800M records, but it now seems the true number is closer to 2Bn. This is entirely fresh data, not duplicates of data from previous breaches. The data includes things like names, email addresses, phone numbers, physical addresses, gender, dates of birth, mortgage amounts & interest rates, Facebook/LinkedIn/Instagram accounts, and characterisations of credit scores (average, above average etc.) — arstechnica.com/… & nakedsecurity.sophos.com/…
- ⭐️ Epic (makers of the popular game Fortnite) have come under fire for the way in which their app store collects and shares data about users use of competitor Steam’s app store — arstechnica.com/… & nakedsecurity.sophos.com/…
- Gargantuan Gnosticplayers breach swells to 863 million records — nakedsecurity.sophos.com/…
- Citrix have publicly acknowledged a data breach in which their customers ‘business documents’ were stolen, but security researchers are claiming this is a bigger and longer-lasting breach than Citrix’s statement suggests — nakedsecurity.sophos.com/…
- Misconfigured Box accounts leak terabytes of companies’ sensitive data — nakedsecurity.sophos.com/… & Dozens of companies leaked sensitive data thanks to misconfigured Box accounts — techcrunch.com/…
- 🇺🇸 Meditab Health Tech Company Data Leak — www.macobserver.com/…
- 🇺🇸 In a letter to from Senator Ron Wyden, T-Mobile has disclosed 5 instances of abuse of the location data it was sharing with third parties — www.macobserver.com/…
- Elsevier exposes users’ emails and passwords online — nakedsecurity.sophos.com/…
- ‘Yelp for conservatives’ MAGA app leaks users data — www.zdnet.com/…
- News
- ⭐️ Patent filings show Apple is working on giving FaceID the ability to tell even twins apart — www.loopinsight.com/…
- ⭐️ (Editorial by Bart: this really underlines the fact that no company is too big or too technologically sophisticated to fall prey to phishing) Scammer pleads guilty to fleecing Facebook and Google of $121m — nakedsecurity.sophos.com/…
- 🇺🇸 John Oliver bombards the FCC with anti-robocall robocall campaign — nakedsecurity.sophos.com/…
- Sir Tim Berners-Lee Calls for Adoption of Contract for the Web to end ‘Dysfunction’ — www.macobserver.com/…
- Sir Tim’s full letter — webfoundation.org/…
- Facebook sues developers over data-scraping quizzes — nakedsecurity.sophos.com/…
- Facebook’s data deals are under criminal investigation — www.loopinsight.com/…
- G Suite admins can now disallow SMS and voice authentication — nakedsecurity.sophos.com/…
- 🇺🇸 FBI crackdown on DDoS-for-hire sites led to 85% slash in attack sizes — nakedsecurity.sophos.com/…
- 🇺🇸 New bill would give parents an ‘Eraser Button’ to delete kids’ data — nakedsecurity.sophos.com/…
- Opinion & Analysis
- ⭐️ Beware of second hand USB drives (including thumb drives), and be very careful how you dispose of yours! Security researchers have found that 66% of the 200 second-hand drives they bought on eBay had malware on them, and many were also chock full of sensitive personal data — nakedsecurity.sophos.com/…
- ⭐️ What Google knows about you — www.axios.com/…
- ⭐️ Here are the data brokers quietly buying and selling your personal information — www.fastcompany.com/…
- ⭐️ Child-friendly search engines: How safe is Kiddle? — nakedsecurity.sophos.com/…
- Why Phone Numbers Stink As Identity Proof — krebsonsecurity.com/…
- Here’s What It’s Like to Accidentally Expose the Data of 230M People — www.wired.com/…
- How the tragic death of Do Not Track ruined the web for everyone — www.fastcompany.com/…
- Propellor Beanie Territory
Palate Cleansers
- A serious story that’s not so cleansing on the palate, but is well worth a read regardless: Are you a robot? — www.bloomberg.com/…
- Accompanied by the most wonderfully nerd-tacular cover, especially for a main-stream publication:
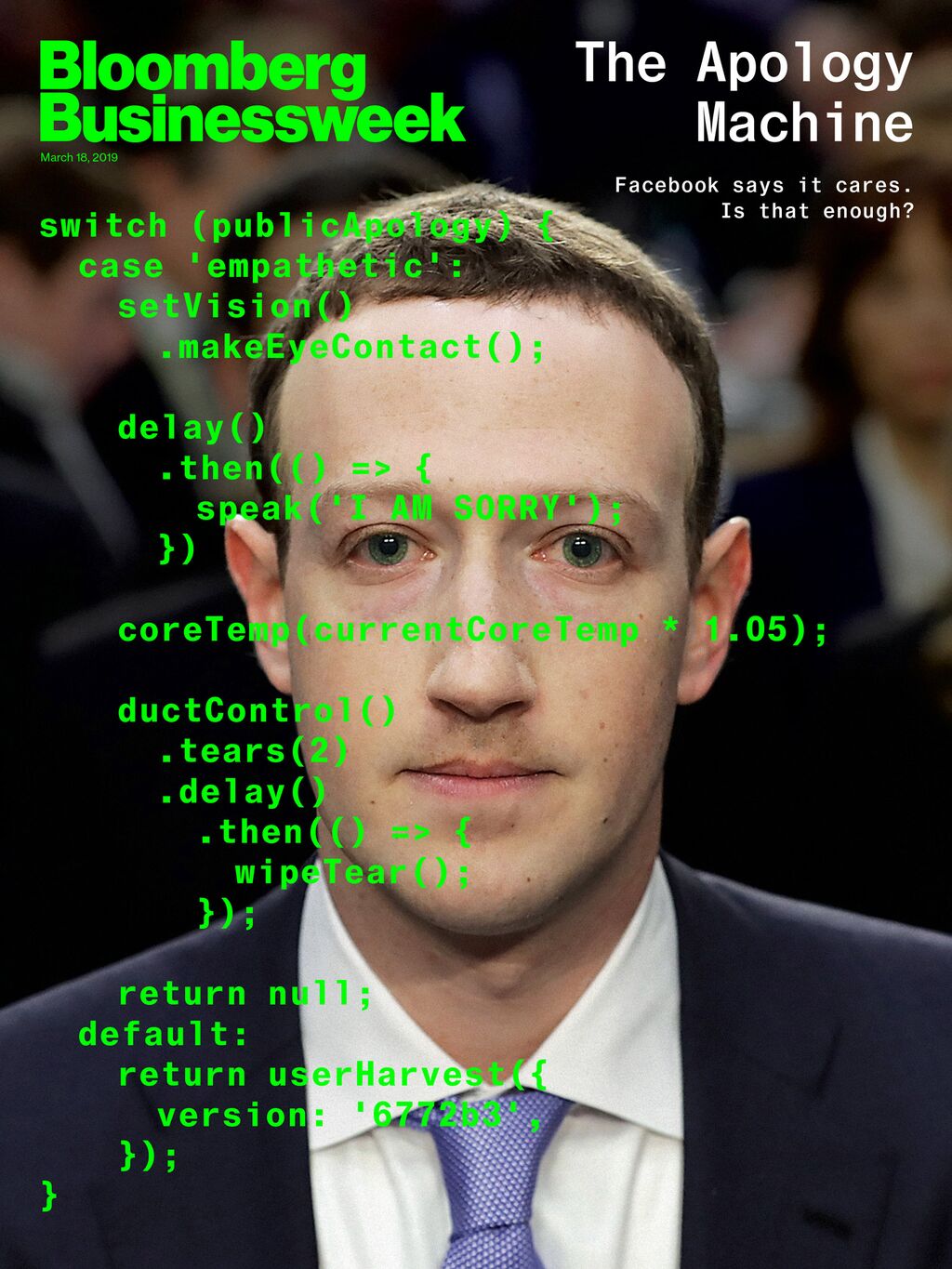
- Accompanied by the most wonderfully nerd-tacular cover, especially for a main-stream publication:
- 🎧 The fantastic science & technology podcast American Innovations is running a series of specials on women inventors to celebrate Women’s History Month. The first instalment tells the story of Margaret Hamilton, the amazing programmer who invented software engineering while making it possible to put man on the Moon! — overcast.fm/…
- NYC is planting secret messages in parks using this typeface for trees — www.fastcompany.com/…
- How the Internet Travels Across Oceans — www.nytimes.com/…
- A fun little game that illustrates just how bad we humans are at being random — www.expunctis.com/…


Here’s another site that lets you securely transfer large files. They just started this service a few months ago. Transfer is free for files up to 25GB:
https://www.swisstransfer.com
The randomness game is a bit lamer than I was thinking. I gave up at 1001 presses where it had scored 69% over me (it never crossed 70% after the first 50 or so presses). Randomness of only two choices is not anywhere near the same as randomness of passwords. After many years using xkpasswd-generated passwords I have now developed a system where I *can* come up with passwords, if I need to in a pinch, that I believe are random enough to make no difference to any guesser or brute-force algorithm than had I used a computer-generated one. Case in point — here’s a random one I will make up right now on the spot… 733!gravel+locomotive+greenery!182. Every component of that password comes from my local environment (my study), though not necessarily directly. Though the symbols I just chose on the fly. Can humans be random? Not over a large domain, but for the purposes of passwords… yes, with some thought.