Feedback & Followups
- Silver Sparrow Mac Malware Update:
- Correction: in the previous Security Bits we made it sound like 30K M1 Macs were infected with this new strain of malware, and that it only affected M1 Macs. That’s not correct. The malware has simply been compiled using Apple’s tools so it runs natively on both Apple Silicon and Intel CPUs (i.e. it’s a Universal Binary), and the 30K infections cover both platforms — www.intego.com/…
- In the previous instalment Allison asked how to tell if you were infected, I didn’t have an answer, but now I do: How to Find Out if Your Mac has ‘Silver Sparrow’ Malware — www.macobserver.com/…
- 🎧 Related Suggested Listening: An excellent interview with stalwart Mac security researcher Patrick Wardle covering Silver Sparrow in particular, and malware on M1 Macs in general — The Checklist by SecureMac Ep. 220: Malware and the M1 with Patrick Wardle — overcast.fm/…
- App Tracking Transparency Update:
- Facebook starts making the case for tracking to the users who will soon get to make their own decisions on cross-app tracking — www.imore.com/…
- Twitter hails iOS 14 privacy changes — www.imore.com/…
- LinkedIn to stop collecting tracking data before Apple shames it — www.imore.com/…
Deep Dive 1 — FireFox’s Total Cookie Protection
The latest Firefox update brings along a very substantial change to how the browser handles cookies, and it’s a privacy game-changer, effectively ending third-party cookies.
Before describing what Firefox have done, let’s describe the world as it has been up until now.
To keep things clear, we need to agree on some terminology.
Firstly, the URL in the address bar defines what I’ll refer to as the primary site. It’s where you explicitly chose to send your browser in some way, perhaps by clicking a link, opening a bookmark, or typing it into the address bar.
When your browser loads the primary web page there are two parties involved, the browser and the site’s web server. These are the first and second parties.
Web pages can embed resources from other websites. Those could be anything, images, videos, scripts, little embedded sub-pages (iframes) etc. To load those resources your browser has to talk to the web servers hosting them, and those web servers are all third parties. You didn’t explicitly choose to contact those servers, they were implicitly contacted so as to be able to load the page you did explicitly request.
Every time your browser contacts any web server that server can include a little token in the reply and ask the browser to store that token locally, and to include that same token in all future requests to that server. These tokens are called cookies, and the browser stores them in a so-called cookie jar.
Every cookie in a cookie jar contains at least four important pieces of information:
- the domain of the website that sent (or set) the cookie
- a name for the cookie
- a value for the cookie
- an expiration date for the cookie
In this pre-total-cookie-protection world, the browser retains one cookie jar for all regular tabs and all regular windows, and that jar is permanent, when you quit and re-start the browser all the cookies are still in that jar.
One of the things that makes private browser mode different is that those tabs get their own cookie jar, and the private cookie jar is not permanent, when you quit the browser the private cookie jar gets emptied.
In this world, ad tracking works by asking the owners of primary websites to embed a resource (perhaps just 1px by 1px image) in their page that loads from a server that’s part of the ad tracking network. That server is a third-party, and they can include a cookie in their reply. The browser gets the cookie that contains a unique ID, and stores it in the one universal cookie jar.
Every time the user visits another primary website with the same tracker embedded, their browser returns the cookie it was sent before, telling the server they are the same person from the other websites in the process.
So, third-party cookies facilitate the tracking of users across the primary websites they visit, assuming those primary sites are integrated with the same tracker.
You might think that blocking third-party cookies would solve the tracking problem, and it would, but, not without some serious collateral damage!
3rd party cookies were not invented for tracking, they were invented to facilitate relationships between sites. Among those relationships are authentication relationships — you can’t have any kind of single-sign-on without 3rd party cookies, so when you block them, some things simply stop working, you find yourself logged out of some sites and unable to log in.
So, the desire is to allow the cross-site relationships we rely on while blocking tracking.
Until now, the approach has been to assume all 3rd-party cookies are legitimate and to block known trackers by simply not saving cookies from their domains into the one universal cookie jar.
Firefox have turned that approach on its head. Rather than assuming all 3rd-party cookies are fine and block-listing known trackers, they are assuming all 3rd-party cookies are hostile, and allow-listing only authentication providers.
Only authentication cookies go into the universal cookie jar, and all other cookies go into a per-site cookie jar for each primary website you visit. When you go to google.com a Google-only cookie jar is created, when you go to facebook.com a Facebook-only cookie jar is created, and so on. Each jar is still storing 3rd-party cookies, but they’re all independent of each other, so a tracker sees you on Google and you on Facebook as two completely separate people, putting an end to cross-site tracking via cookies.
Something else to note, Firefox are not only relying on allow-lists of known authenticators, they are also including some algorithms (probably ML of some kind) to detect authentication-like behaviour and allow those cookies into the global cookie jar. Assuming Firefox can keep these algorithms well-tuned they should make this entire change 100% transparent to users.
Finally, just a reminder that none of this in any way alters your relationship to the primary sites you visit. When you go to a site, that site can track what you do on that site, and it will always be able to do so, nothing can change that. Firefox can stop Facebook from seeing what you do on Reddit, but it can never stop Facebook seeing what you do on Facebook!
Link: Mozilla has just announced a ‘major privacy advance’ for its Firefox browser — www.imore.com/…
Deep Dive 2 — Has Google Seen the Light?
Google released a blog post announcing their intention to move away from cookie-based tracking and switching to privacy-respecting aggregate tracking instead.
Some Highlights:
… If digital advertising doesn’t evolve to address the growing concerns people have about their privacy and how their personal identity is being used, we risk the future of the free and open web.
That’s why last year Chrome announced its intent to remove support for third-party cookies, and why we’ve been working with the broader industry on the Privacy Sandbox to build innovations that protect anonymity while still delivering results for advertisers and publishers. Even so, we continue to get questions about whether Google will join others in the ad tech industry who plan to replace third-party cookies with alternative user-level identifiers. Today, we’re making explicit that once third-party cookies are phased out, we will not build alternate identifiers to track individuals as they browse across the web, nor will we use them in our products.
…
… our web products will be powered by privacy-preserving APIs which prevent individual tracking while still delivering results for advertisers and publishers.
I’d love to be able to go into great technical detail, but I can’t, because Google haven’t told is what they will do, just what they won’t, and some vague aspirations.
I don’t know whether Google are being good netizens, or if they’re just being pragmatic and can see the writing on the wall for the modern tracking ecosystem. I’m not sure that’s what really matters though. Regardless of their motivation, what we need to see is the actual technology they roll out. Will it actually preserve privacy? Or will it just be a case of meet the new boss, same as the old boss?
My approach is to welcome the sentiment, assume they are being genuine, but verify that assumption when they start rolling out actual technology. Basically, I’m taking a page from President Reagan’s book — trust but verify.
Links:
- Google’s blog post: Charting a course towards a more privacy-first web — blog.google/…
- Related Opinion/Analysis:**
❗ Action Alerts
- Keybase secure messaging fixes photo-leaking bug – patch now! — nakedsecurity.sophos.com/…
- Another Chrome zero-day exploit – so get that update done! — nakedsecurity.sophos.com/…
- macOS 11.2.2 Protects MacBook Pro and MacBook Air from Non-Compliant USB-C Hubs and Docs — tidbits.com/…
Worthy Warnings
- From Allison: LastPass Android app tracking users, says researcher — www.tomsguide.com/…
- I see you: your home-working photos reveal more than you think! — nakedsecurity.sophos.com/…
Notable News
- Microsoft have released an out-of-band emergency patch for their Exchange corporate group-ware server, plugging a collection of vulnerabilities being actively exploited by a newly discovered Chinese espionage group to break into large corporations and education and research institutions — Microsoft: Chinese Cyberspies Used 4 Exchange Server Flaws to Plunder Emails — krebsonsecurity.com/…
- Microsoft’s post about the attacks: HAFNIUM targeting Exchange Servers with 0-day exploits — www.microsoft.com/…
- Microsoft’s Advisory on the vulnerabilities: Multiple Security Updates Released for Exchange Server – updated March 5, 2021 — msrc-blog.microsoft.com/…
- Brave to Launch Its Own Search Engine — tidbits.com/…
- 🇺🇸 TikTok Settles Class Action Lawsuit for $92 Million — www.macobserver.com/…
- Transferring photos from iCloud to Google Photos is finally possible. Here’s how – CNET
Top Tips
Excellent Explainers
- A good summary and explanation of the recent faux-scandal around a locked Apple ID: The Mystery of Dustin Curtis’s Locked Apple ID — tidbits.com/…
Interesting Insights
- Excellent reporting from Wired highlights the fact that many mobile apps make use of cloud services for their back-ends, and many of them are misconfigured, making them insecure: Thousands of Android and iOS Apps Leak Data From the Cloud — www.wired.com/…
- Brian Krebs explains a concerning new development in malware economics — grey-hat companies and cybercriminals are paying browser plugin creators to add extra code into their extensions, or are simply buying popular extensions outright and adding in extra nefarious code themselves: Is Your Browser Extension a Botnet Backdoor? — krebsonsecurity.com/…
- A fascinating deep-dive into a modern malware delivery mechanism: Search crimes – how the Gootkit gang poisons Google searches — nakedsecurity.sophos.com/…
Palate Cleansers
- 🎦 Bart: Perseverance filmed itself landing on Mars — apod.nasa.gov/…
- Bart: There’s a hidden message in the parachute of NASA’s Mars rover — www.theverge.com/…
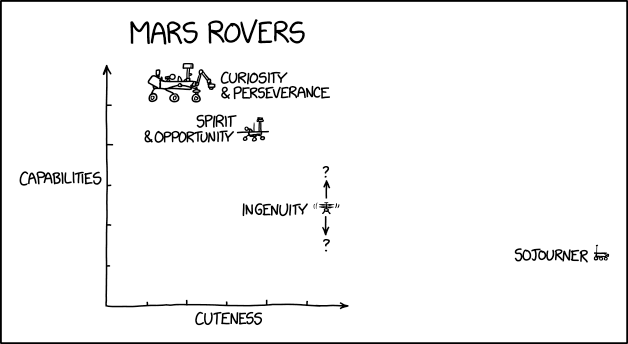
- Allison: Mars Rovers — xkcd.com/…
- Allison: Luke Miani creates the first “M1 iMac mini”
Legend
When the textual description of a link is part of the link it is the title of the page being linked to, when the text describing a link is not part of the link it is a description written by Bart.
| Emoji | Meaning |
|---|---|
| 🎧 | A link to audio content, probably a podcast. |
| ❗ | A call to action. |
| flag | The story is particularly relevant to people living in a specific country, or, the organisation the story is about is affiliated with the government of a specific country. |
| 📊 | A link to graphical content, probably a chart, graph, or diagram. |
| 🧯 | A story that has been over-hyped in the media, or, “no need to light your hair on fire” 🙂 |
| 💵 | A link to an article behind a paywall. |
| 📌 | A pinned story, i.e. one to keep an eye on that’s likely to develop into something significant in the future. |
| 🎩 | A tip of the hat to thank a member of the community for bringing the story to our attention. |

