It’s an action-packed show this week. I recommend listening to the latest SMR Podcast, not just because I’m on but because it’s a fantastic episode. We’ve got interviews with Willow about their wearable breast pump, Whistle’s pet tracker and activity monitor, CrazyBaby’s levitating speaker called Mars, Cobra’s wireless backup camera on a license plate frame, and we’ve got a Dumb Question Corner from Uncle Bob about VPNs and secure messaging services. Bart brings us up to date with another segment of Security Bits.
Hi this is Allison Sheridan of the NosillaCast Mac Podcast, hosted at Podfeet.com, a technology geek podcast with an EVER so slight Macintosh bias. Today is Sunday January 22, 2017 and this is show number 611.
Chit Chat Across the Pond
In Chit Chat Across the Pond this week, Bart and I spent a long time going through the homework assignment for the previous Programming By Stealth. I thought it was great fun and was VERY proud of my little self for actually doing most of the homework successfully. After about an hour we finally get back into the new stuff and it’s even more fun. He teaches us how to use CSS Selector Attributes to assign colors and such to html buttons. We both had a blast and I can’t wait to learn more! Check it out at on podfeet.com or subscribe to Chit Chat Across the Pond in your podcatcher of choice.
SMR Podcast
Now I want you to pause listening to this show and immediately go subscribe to the SMR Podcast. You can come back and finish and listen to SMR later, but the latest episode was me, Robb and Chris and it was fantastic. I’m not just saying this, it’s true. Sometimes they have me on to talk about an Apple event and I feel like I”m just droning on and on blathering about the announcement to them. I even bore myself after a while! this time it was way more fun because there wasn’t a specific big topic so we were all over the map. I love making Chris laugh and it happens a bunch in this episode. Anyway, go subscribe to the SMR Podcast in your podcatcher or go to smrpodcast.com and give a listen.
Blog Posts
CES 2017: Willow Wearable Breast Pump
This was a hard interview for me to do, like I said, in my generation you would have never said breastfeeding out loud. I don’t know exactly why but I’m sure glad we’re over that now. One thing I wanted to note is that when she quoted the price, and throughout the interview I did not know it was a double breast pump. If you listened closely early on I said that if you wore one under your bra it would be noticeable. That’s because I thought it was only one! So the price for Willow is actually right in line with traditional chemistry set versions.
Let’s change gears and talk about a new device to track your pets.
CES 2017: Whistle GPS Pet Tracker & Activity Monitor
Dumb Question Corner: VPNs vs End-to-End Encrypted Messaging Services
CES 2017: CrazyBaby Mars Levitating Speaker
I know I said it in the interview, but I SO want one of these levitating speakers! It was really really cool. Not to mention how fun James was in the interview!
CES 2017: Cobra Wireless Backup Camera
I think this backup camera is a fantastic solution. In working on the video from the interview, Steve noticed that the artwork Dave Marsh was showing us said “Powered by LOOK-IT”. He went hunting and found the website lookitcam.com where you can watch a video of it in action. It looks like Cobra is essentially the reseller for LOOK-IT, because where to buy links back to Cobra. It’s not on Cobra’s website till its launched in April but $249 for a backup camera that uses your phone and requires essentially no installation is pretty cool.
Patreon and Amazon
I want to give a big shoutout to Paul Markham, our latest Patron of the NosillaCast. He went to podfeet.com/patreon and signed up to pledge a small sum to show his support for the value he gets out of the shows. It means a lot, and not just monetarily, to have someone do this. I also love that I’m getting to chat with people I never heard from before Patreon!
By the say, if you want to support the show and don’t want to be recognized on the air, please let me know when you sign up. I realize that some people don’t like that kind of thing so I want to be sensitive here. Thanks again, Paul for your support of the podcasts!
Security Bits
Security Medium 1 – Browser Auto-fill Vulnerability
Security researchers have found a new way of turning the convenience of form auto-fill features in browsers against users.
This is the feature that some browsers offer where they use the names of inputs in web forms to guess at the data that should go in there, and automatically fill it in for you. Things like your phone number, address, and so on.
Some browser plugins take this concept a little further, and will also auto-fill things like credit card details. Some password manager plugins allow you to store autocomplete data which they will then fill in for you.
Some browsers, including Google’s Chrome and Apple’s Safari (but not FireFox) auto-fill fields without any user interaction at all. When the page loads, the fields are immediately filled in without you having to do anything. In FireFox the user has to put their cursor in a text field and then choose to auto-fill the form.
The big shortcoming that Chrome and Safari have is that they don’t check if a text box is visible before auto-filling it. So, it would be possible to have one innocent text box visible, asking for say, your email address, but have many more invisible, sucking up your address, telephone number, and even credit card details. When you hit submit, you think you are only sending your email address, but you are actually sending all that other information.
One obvious solution would be never to auto-fill hidden elements.
Personally, I always disable auto-fill in my browsers, because even if you never submit the form, as soon as those characters enter the text boxes, they become visible to JavaScript, and hence, could be stolen even if you never hit submit on the form. Yes it’s convenient, but no, it will never be fully safe, and I consider it a dangerously flawed idea in the first place.
Links:
Security Medium 2 – No, there is no Back Door in WhatsApp
The usually reliable UK newspaper The Guardian is coming under fire for starting an internet faux-scandal about WhatsApp that turns out to be unsupportably inflamatory now that the facts are in.
The initial reporting was that a backdoor had been found in the popular messaging App’s encryption, but that is not true.
The reality is much more nuanced, and much less sexy a story.
Like Apple, WhatsApp had to strike a balance between security and usability. To get absolutely perfect trust-no-one security, users would need to manage their own encryption keys. This is how very security conscious apps like Signal and Threema work. But regular users will not tolerate that kind of user experience, so the tradeoff is automated key management by the provider. Apple do this with iMessage, and Facebook do this with WhatsApp. This means you, as a user, must trust that the provider (Apple or Facebook for iMessage and WhatsApp) will not add extra keys behind your back, allowing devices that are not really yours to send and receive messages as you.
Should a new key be added behind your back, it will not be retro-active. The new key can only read pending messages (those with one tick rather than two), which the protocol says should be re-sent with the new key, and future messages.
This is not a bug. This is not a backdoor. This is a feature. It is an explicit choice to give up some security in exchange for usability. This decision makes the average user much more secure than not having encryption. As has always been the case, if you need the absolute top level of security, you simply must use a system where you must do the key management.
One point where Facebook could be criticised is that they have an optional feature that will alert you when keys change, but the alert happens AFTER all pending messages are re-transmitted, rather than before. This is a silly oversight, and should be easy to fix. It should also be noted that Apple doesn’t even give you this limited control over your keys – on iMessages, the keys are completely managed by Apple, and not visible to the user at all.
Links:
- Reported “backdoor” in WhatsApp is in fact a feature, defenders say – arstechnica.com/…
- WhatsApp ‘backdoor’ turns out to be known design feature – nakedsecurity.sophos.com/…
Important Security Updates
- Google have patched a nasty security hole in the firmware of their Nexus 6 and 6P phones. The vulnerability allowed attackers with USB access to inject code of their choosing into the firmware of the onboard modem, allowing them to install spying software on the devices – arstechnica.com/…
- Both Adobe and Microsoft have released their Patch Tuesday security updates for January 2017 – krebsonsecurity.com/…
- Adobe have angered many Google Chrome users by bending a browser plugin into their security update (Editorial by Bart: this is shameful behaviour by Adobe IMO, but by no means a first – their Java updates have a history of bundling crapware) – arstechnica.com/…
- Apple have released OS X 10.11.6 (El Capitan) to fix a kernel bug causing crashes – www.imore.com/…
Important Security News
- The US Federal Trade Commission (FTC) has filed suit against D-Link for failing to protect their customers from known vulnerabilities in their devices. (Editorial by Bart – the complaint is absolutely scathing, it looks very bad for D-Link) – nakedsecurity.sophos.com/…
- Pacemaker manufacturer St Jude has released a firmware update for their pacemakers to patch potentially lethal security vulnerabilities – nakedsecurity.sophos.com/…
- Security firm Cellebrite has been hacked, showing that this company works for everyone from US police departments to authoritarian regimes, including Russia. The hack is being seen as confirmation that Apple was correct when it said backdoors could never be kept secret – arstechnica.com/…, www.macobserver.com/… & www.imore.com/…
- Microsoft is working on technology to automatically lock your computer when you step away form it, being the inverse of their Microsoft Hello feature, some are nicknaming it Microsoft Goodbye – nakedsecurity.sophos.com/…
- A remote code execution bug has been found in Samsung’s popular SNH-1011 IP cameras – Samsung have promised a fix soon – if you have one of these cameras, make sure it’s IP is not accessible from the web until the patch is released and applied to your camera – arstechnica.com/…
- The FBI have issued as PSA warning that employment scams targeting college students remain prevalent in the US – www.ic3.gov/…
- Security researchers warn that the selfie enhancement app Meitu is gathering staggering amounts of personal data. The problem is worse on Android because of how permissions work on that platform, but the iOS version of the app checks if your phone is jail broken, and if it is, it then gathers the data Apple normally protects for you – arstechnica.com/… & nakedsecurity.sophos.com/…
Notable Breaches
- Data from the breach of the official Hello Kitty site in December 2015 has now been publicly leaked. There are 3.3 million records, and they include personal information as well as un-salted hashed passwords, and unencrypted security questions and answers – nakedsecurity.sophos.com/…
Suggested Reading
- The Year in Mac Security 2016 – www.intego.com/…
- Krebs Immutable Truths about Data Breaches – krebsonsecurity.com/…
- How to Choose the Right Password Manager for You – www.intego.com/…
- What the end of Patch Tuesday means for businesses – nakedsecurity.sophos.com/…
- Newly discovered Mac malware (Fruitfly) found in the wild targeting biomedical research centres. It now appears the malware also works well on Linux – arstechnica.com/…
- How hackers made life hell for a CIA boss and other top US officials – arstechnica.com/…arstechnica.com/…
- Cautious welcome to Facebook’s moves to fight fake news – nakedsecurity.sophos.com/…
- Tor users at risk of being unmasked by ultrasound tracking – nakedsecurity.sophos.com/…
- Obama administration signs off on wider data-sharing for NSA – nakedsecurity.sophos.com/…
- Trump picks hackable Rudy Giuliani as cybersecurity advisor – nakedsecurity.sophos.com/…
- Who is Anna-Senpai, the Mirai Worm Author? – krebsonsecurity.com/…
- Already on probation, Symantec issues more illegit HTTPS certificates – arstechnica.com/…
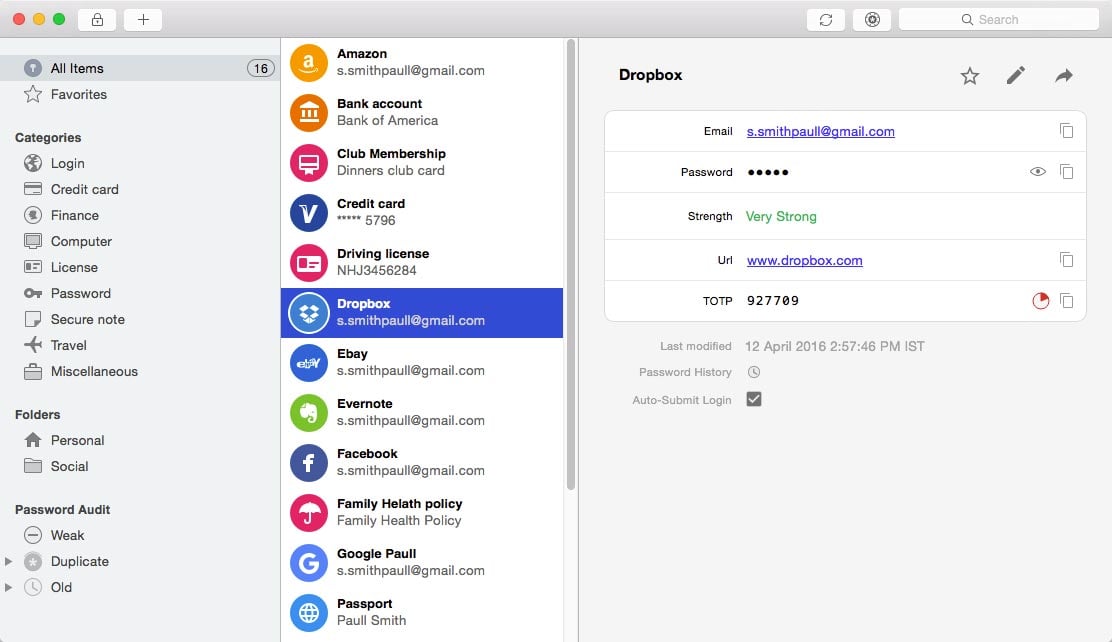 During Security Bits when Bart told us about the Intego article explaining how to pick a password manager, I noted that Enpass made their recommendation list. I noted that it was really inexpensive, so maybe we should give it a look. After we stopped recording, I looked into it a tiny bit deeper and it looks to me like they pretty much replicated the visual interface of 1Password. This kinda makes me angry. I have zero design skill so I really respect the people who can make an interface that flows well with good logic and is pleasing to look at. LastPass is an excellent password manager, but the interface (back when I used it) was very displeasing visually to me. I have looked over my daughter’s shoulder at the newer version of LastPass and it looks a lot better. For Enpass to lift the visual design interface from AgileBits makes me not want to try it after all.
During Security Bits when Bart told us about the Intego article explaining how to pick a password manager, I noted that Enpass made their recommendation list. I noted that it was really inexpensive, so maybe we should give it a look. After we stopped recording, I looked into it a tiny bit deeper and it looks to me like they pretty much replicated the visual interface of 1Password. This kinda makes me angry. I have zero design skill so I really respect the people who can make an interface that flows well with good logic and is pleasing to look at. LastPass is an excellent password manager, but the interface (back when I used it) was very displeasing visually to me. I have looked over my daughter’s shoulder at the newer version of LastPass and it looks a lot better. For Enpass to lift the visual design interface from AgileBits makes me not want to try it after all.
After Security Bits point out that Enpass looks like a ripoff of 1Password
image: https://www.intego.com/mac-security-blog/wp-content/uploads/2016/11/Enpass-Screenshot.jpg


Speaking of password managers, Macworld did a glowing writeup on Secrets and Secrets Touch (for MacOS and iOS, respectively). What they didn’t mention AT ALL is that the free versions only cover 10 passwords each, and if you want unlimited pw management, you must spend $10 apiece for the apps.
Pretty poor reporting by MacWorld, and most App Store comments are that the apps are barely worth $20. Also, it sounds like they lifted the 1Password UI.
yup, most messengers don’t have end-to-end encryption. key logs and others are far too dangerous and public wifis spell disaster for people who are willing to connect online. i have been on the receiving end of the stick and i had to resort to ivacy vpn to protect my messages and my personal data. and since the day i got bitten by these disasters, i am now very keen on privacy and even talk to my colleagues about it and often cite snowden during my arguments.