Hi folks, welcome to episode 621 of the NosillaCast, a technology geek podcast with an ever so slight macintosh bias. This the show for Sunday April 2nd 2016, and I’m your guest-host Bart Busschots.
CCATP – Dermot Daly from Tapadoo
In this week’s Chat Chat Across the Pond I chatted with Dermot Daly who runs Tapadoo, a mobile app development company based Dublin, Ireland. We talk about what it’s like being a developer witting apps for iOS and Android, how App Store and Google Play store differ from each other, and the state of the app business in general. We also look at what some of the recent changes to the app store really mean for developers.
An Update on my Health Tracking
Of all the things I’ve ever recorded with Allison over the years, the show that I’ve gotten the most positive feedback on is our CCATP chat about how I’m using tech to gain control of my health and weight. We recorded that chat in July last year, so I thought it might be nice to update you all on how things are going.
Firstly, I still use an Apple Watch to measure the calories I burn. I’ve now moved from an original Apple Watch to a Series 2, and I love it even more than I loved the original. The two things I really wanted from the new watch were waterproofness, and built-in GPS. Not having to worry about your watch getting wet is a really big deal when you get your exercise mainly form cycling, and live in Ireland! The original Apple Watch relied on the iPhone’s GPS, so if there was ever a bluetooth glitch between the watch and the phone, the watch lost its ability to accurately record calories, and generally assumed you’d decided to stand still for half an hour and robbed you of hundreds of calories. That kind of thing only happened ver occasionally, but it was so dis-heartening on handful of occasions it happened that I really wanted to stop it happening again. An un-expected bonus is that the battery life on the Series 2 is not just a little better than it was on the original, but MUCH better. I now generally finish the day with well over 50% battery remaining, and I track between 1 and a half and three hours of workouts every day! Also, I went for the Nike+ model, and those straps with the little holes are so much nicer to wear than the solid sports band I had one my first watch.
Secondly, I’m still using MyFitnessPal to track calories consumed and manage my daily calorie budget. The app has been steadily improving, so I’m loving it more and more as time goes on. Also, the longer you use the app, the better it knows you, and the more it can help you to log your food quickly and easily. Also, in my experience it was well worth taking the small extra effort to create saved meals. I turns out I’m much more of a creature of habit than I realised, and I repeat the same meals very regularly indeed!
I’ve also added some nice connected hardware into the mix to track my progress. I track my weight and body composition with the Body wifi scales from Withings, and my blood pressure with the Withings bluetooth Blood Pressure Monitor. The industrial design on both of the Withings products is superb, and while I initially hated their app, it’s improved a lot over the last year, to the point that I’ve moved from merely tolerating it to actually liking it.
I still rely on Apple’s health app to act as the hub that ties all my data together. My watch writes my calories burned there, MyFitnessPal gets the burn data from there, as well as my current weight, and writes back my nutrition information, and both of my Withings devices write the measurements they take there.
So – the big question, is it working?
The reason I started down this road was because my blood pressure was too high, presumably because I was over weight. So, has all this tech actually solved the problem? Yes! In January 2016 my BMI was well over 25, I was, officially, morbidly obese, I had a resting heart rate in the low 80s, and I had grade 1 hyper tension. Today, my BMI is 21 with a body fat percentage of just 12%, a resting heart rate of about 60, and my blood pressure at the bottom of the normal range.
CSUN 2017 Interviews
Two macOS Window Tilers
Security Bits
Followup – More Fallout from Vault 7
- Documents in the recent leak of CIA documents exposed a vulnerability in 318 Cisco routers and switches that allows simple remote-takeovers of the switch. Cisco are presumably rushing to get a patch out, but nothing has been released yet – arstechnica.com/…
- Additional information released as part of the dump shows the CIA targeted Macs, including making booby-trapped Thunderbolt ethernet adaptors code-named sonic screwdrivers that used the now-patched Thunderstrike vulnerability to take over Macs they were physically plugged in to – arstechnica.com/… & nakedsecurity.sophos.com/…
Security Medium 1 – The iCloud Extortion Attempt
A gang of cyber criminals calling themselves the Turkish Crime Family say they have 300 million iCloud account details, and that if a ransom is not paid by the 7th of April, they will start using those details to wipe devices and accounts. The ransom they are demanding is $100K in iTunes gift vouchers, or, $75K in Bitcoin or Ethereum crypto currency.
Based on all the reporting I’ve read to date, it seems they group definitely have some Apple ID usernames and passwords, and that they probably got them from breaches of sites other than iCloud, and/or from phishing campaigns. Basically, password re-use and phishing are the prime suspects yet again. Apple insist iCloud has not been hacked.
How can you protect yourself? If you have re-used the password you use for your iCloud anywhere else at all ever then it would seem sensible to re-set your Apple ID password ASAP, and be sure to set it to something unique. This would also seem like an opportune moment to enable two-factor auth if you haven’t done so already.
You should also be aware that some scammers seem to be capitalising on the news coverage of this story by launching phone-based scams where they pretend to be Apple calling about the iCloud breach. Apple will not call you out of the blue like that, so don’t fall for these scams!
Links:
- Hackers Threaten to Wipe Out Millions of iCloud Accounts if Apple doesn’t Pay $75K – www.macobserver.com/…
- Here’s How To Protect Yourself From The iCloud Extortionists – www.macobserver.com/…
- ‘Turkish’ hackers threaten to reset millions of iCloud accounts – nakedsecurity.sophos.com/…
- If You Haven’t Changed Your iCloud Password in the Past Two Years do it Now – www.macobserver.com/…
- How to set up two-factor authentication for your Apple ID and iCloud account – www.macworld.com/…
- iCloud wasn’t breached but you should still reset your password and set up 2-factor authentication – www.imore.com/…
- Ignore that call from “Apple” about an iCloud breach – www.macworld.com/…
Security Medium 2 – MAC Address Randomisation Weaknesses
Any device that has a wifi card has a unique MAC address, and, as long as that card is active that MAC address can be seen by nearby wifi access points. Retailers and others realised this fact allowed smart phones to be used to track people as they move through a store or a city, or even as they travel around the world.
MAC address randomisation was invented to address this problem. The idea is that while a device is not connected to a Wifi network, it will use a periodically changing random MAC address.
Apple added MAC address randomisation in iOS 8 in 2014, and Google added it to Android as an experimental feature the same year, before adding it as a full-blown feature in 2015. In theory, neither iOS nor Android devices should be trackable by their MAC address anymore. So, a group of security researchers set out to test that theory, and found that the reality is somewhat different!
In the standard passive scenario where the trackers just listen, iOS implements MAC address randomisation perfectly, and, almost all iOS devices you see in use today are running iOS 8 or later, so almost all iOS devices in the real world are randomising their MAC addresses.
The same is not true for Android. From a sample of nearly 1 million phones, only 6% implemented MAC address randomisation. That’s bad enough, but it gets worse! The majority of that 6% that do implement MAC address randomisation were found to implement it poorly – the devices periodically broadcast their real MAC addresses by mistake!
Everything is not perfect for iOS though. The researchers also found an active attack that works against all devices, including iOS devices, and it may not be possible to fix. The attack relies on standard features of the wifi protocol, and involves sending packets aimed at specific MAC addresses an seeing if any device with that MAC address responds. In effect, it is a brute-force attack. You broadcast to all possible MAC addresses in Apple’s assigned range, and eventually, you’ll get a reply from every Apple device in the area.
While the weakness is not easy to fix, it’s also not nearly as easy or practical to carry out as the old-style passive attacks that work on un-randomised or poorly randomised devices.
Link: arstechnica.com/…
Security Medium 3 – US Congress Votes to Revoke ISP Privacy Rules
In the previous Security Bits we mentioned that votes were up-coming on removing ISP customer privacy protections. Those votes have now passed both the US House of Representative and the US Senate, so the bill is on its way to President Trump, who is expected to sign it.
The bill invalidates US FCC (Federal Communications Commission) regulations introduced last year which prevented ISPs from selling customer browsing data without their consent. The votes were largely along party lines – everyone who voted for the bill is a Republican, and all Democrats voted against it, but there were a handful of Republicans who voted against the bill.
Central to this are two important facts.
Firstly, customers pay their ISP for a service. Selling data about your paying customers is not the same as offering free ad-supported services.
And secondly, and most importantly, ISPs are literally in an extremely privileged position – every bit of data that enters or leaves your home passes through your ISP. That’s not just your web browsing, but every single thing you do online on every single device in your home over every single protocol. Yes, Google and Facebook see much more of your browsing that many would like, but they only see snippets of your browsing (and your email if you use GMail). They have no idea what’s happening over other protocols.
I’ve seen a lot of politicians miss these two vital facts. I can’t tell whether they are just ignorant, or whether they are being wilfully dishonest, that’s something we all have to judge for ourselves.
Another important factor that complicates things is the sorry state of the US broadband market. If there was a thriving healthy market with lots of choice, you could make the argument that the free market will save the day, and that those who want privacy will be able to vote with their wallets and choose to use privacy-respecting ISPs. But, the reality on the ground in the US is very different. There is not a thriving healthy market, most US consumers have little or no choice of ISP.
Finally, if you consider internet access to be a basic utility like water, electricity, or telecommunications, then it makes a lot of sense to regulate the providers. We take it for granted that our electricity company is not allowed to sell our data, and that our telephone companies can’t sell our call data to advertisers. Why are ISPs being given such different treatment?
Can you do anything to protect yourself?
Yes – encrypt everything! Your ISP will still see the two end-points of any encrypted data streams to and from your home, but they can’t see into them, despite their privileged position.
Using HTTPS on websites helps a little, but only a little. HTTPS encrypts the data exchanged between you and the site you’re visiting including the full URL, but generally not the domain part of the URL. Why? Because the HTTPS connection will be to a given IP, which will probably uniquely identify the site anyway, but even if the site is on a shared IP, your DNS queries will have given the domain name away anyway. DNS packets are unencrypted, so every domain name used in every app on every device within your home can be seen by your ISP. Note that this is true regardless of which DNS server you configure your computers to use. Some ill-informed people are recommending people ‘protect’ their privacy by switching DNS provider. This is terrible advice!
What you need to do is to wrap all your traffic, including the protocols without encryption support like DNS, in a layer of encryption as it moves through your ISP. The obvious technical solution is to use a VPN, but be careful!
Using a VPN changes who you place in the privileged position of seeing all your data, but it doesn’t remove the presence of such a privileged position. When you use a VPN, you simply move from trusting your ISP, to trusting your VPN provider. Hence, it’s really important to choose your VPN provider wisely, they have to be someone you trust. In reality, that means you have to follow their incentives, which means following the money. That means free services are almost certainly out – if they are not charities, they must be making money off your use of their service – if you are not giving them that money, then they are probably selling your data!
The other obvious problem with using VPNs for everything at all times is the hassle of setting that up. You could install a VPN app on every single device in your home, which is a lot of work, and also probably impossible, because you probably have devices that don’t support VPN clients like smart TVs, game consoles, and IoT devices in your home. Clearly, what you want is to have your router manage a VPN tunnel between your home and your VPN provider, and automatically route all traffic through it. This is easy to do on corporate routers, and it can be done if you build your own router using open source firmwares, but that’s not trivial, and beyond the vast majority of the population’s abilities. Hopefully router manufacturers step up and make this easy for people in the future.
If I lived in the US I would run my own VPN end-point on a cheap cloud VM from a provider like Digital Ocean or Linnode, then configure my home-made PFSense-based router to connect to that VPN and route all my traffic through it. Thankfully, I don’t have to do that, because Ireland has robust data protection laws and our ISPs are well regulated.
Links:
- Congress Says ISPs Can Sell Your Browser History on Party Line Vote – www.macobserver.com/…
- On the House vote to wipe away the FCC’s landmark Internet privacy protections – www.loopinsight.com/…
- The 265 members of Congress who sold you out to ISPs, and how much it cost to buy them – www.theverge.com/…
- How ISPs can sell your Web history—and how to stop them – arstechnica.com/…
- What Is A VPN, And How Can It Help You? – www.macobserver.com/…
- 5 Things to Consider when Evaluating a VPN for Privacy – www.macobserver.com/…
Important Security Updates
- Apple release a flock of security updates:
- iTunes 12.6 for OS X – support.apple.com/…
- iTunes 12.6 for Windows – support.apple.com/…
- iWork update – support.apple.com/…
- This update adds password protection for documents – www.macobserver.com/…
- Safari 10.1 for OS X Sierra, El Capitan & Yosemite – support.apple.com/…
- OS X 10.12.4 & security update 2017-001 for OS X El Capitan & Yosemite – support.apple.com/…
- iOS 10.3 – support.apple.com/…
- watchOS 3.2 – support.apple.com/…
- tvOS 10.2 – support.apple.com/…
- macOS Server 5.3 – support.apple.com/…
Important Security News
- Windows Vista is dead (MS has ended support) – www.us-cert.gov/…
- Fortune warn of a dangerous new phishing technique that is proving effective. Attackers use Data URLs to make fake URLs that contain the real URL. The give-away is that the URLs start with
data:text/html, so if you see that, run away! – fortune.com/… - Google have announced strong sanctions against Symantec for mis-issuing 30,000 HTTPS certs. Over the next few releases Chrome will stop trusting Symantec certs unless they have ever shorter live-spans until only 9 month certs will be trusted. Also, all EV (Extended Validation) certs from Symantec will be treated as regular non-EV certs. This will remain the case until Symantec prove they have stopped playing fast and loose with the rules for CAs, and if there are any more shenanigans uncovered, Google may come down even harder on Symantec – arstechnica.com/…
- Instagram enables 2-factor authentication, but sadly, via SMS, which is now considered the weakest form of 2FA – www.imore.com/…
- Related – eBay on the other hand are removing support for their hardware 2FA tokens, and forcing users to down-grade their 2FA to SMS-based codes, which is a real step down – nakedsecurity.sophos.com/…
- Security researchers find a vulnerability in a built-in Windows feature which leaves some AV products vulnerable to exploitation, turning them from a defender of your computer into an entry-point for attackers. The vulnerability has been dubbed ‘DoubleAgent’, and despite what you may read in some media outlets, it does not affect all AV, and the Windows feature in question is in no way secret or un-documented – nakedsecurity.sophos.com/…
- LastPass fixes a responsibly disclosed vulnerability in less than a day. The bug was managed through Google’s Project Zero project, which gives vendors 90 days to fix a problem before full disclosure. The clock did not even get down to 89 before LastPass had fixed the problem. Since the problem was on the server-side, it could be fixed without users needed to do anything – nakedsecurity.sophos.com/…
- Unfortunately, the above quickly-fixed LastPass vulnerability was not the only one found. The clock is ticking on another critical vulnerability that Google say will be a lot harder for LastPass to fix, and that they will have to work very hard during the 90 days to get the job done. While we know there is a vulnerability, and that it is serious, the details have not been released, so users should be safe while LastPass work to address the problem – arstechnica.com/… & nakedsecurity.sophos.com/…
- Microsoft got a lot of bad press because their Docs.com service, a specifically designed for sharing documents publicly, and advertised as such, did what it was designed to do, even when users foolishly used it to publish things that should not have published. (Editorial by Bart – the amount of un-thinking Microsoft bashing I saw over this from people who should know better really disappointed me – e.g. Steve Gibson confused Docs.com with OneDrive, and hence, based on that ignorance, tore MS a new one on Security Now) – arstechnica.com/…
- As many expected when the US introduced optional screening of social media accounts when entering the country, that screening is no loner optional in some circumstances (Editorial by Bart – I’d be shocked if this is as far as this slides) – nakedsecurity.sophos.com/…
- Perhaps unsurprisingly, in the aftermath of the recent terrorist attack in London, the UK government is calling for encryption back-doors again – nakedsecurity.sophos.com/…, www.macobserver.com/… & nakedsecurity.sophos.com/…
- US Lawmakers are scathing over the FBI’s massive illegally gathered facial recognition database which is estimated to contain data on about half of all Americans – nakedsecurity.sophos.com/…
- PSA – security researchers warn that someone is putting a lot of effort into attacking GitHub developers, presumably in an attempt to distribute malware. If you have a GitHub account, be on your guard – arstechnica.com/…
- Support for Windows Vista ends on April 11 2017 – if you’re still using the OS, it’s time to upgrade! – nakedsecurity.sophos.com/…
Suggested Reading
- How to protect your private photos and personal data from being hacked – www.imore.com/…
- Quality for news is mostly about solving the reputation issue – mondaynote.com/…
- Android under siege from malware – here’s how to protect your phone – nakedsecurity.sophos.com/…
- Google launches their new invisible CAPTCHA – nakedsecurity.sophos.com/…
- A Judge has signed a sweeping dragnet-style search warrant against Google for all data they have on anyone who searched a given name anywhere on earth over a week. We don’t yet know how Google will respond to such an unprecedentedly broad warrant – nakedsecurity.sophos.com/…
- RSA Conference 2017 Highlights – www.intego.com/…
- Man loses appeal over Facebook threat to kill Obama – nakedsecurity.sophos.com/…
- New York’s ‘unconstitutional’ right to be forgotten bill sparks concern – nakedsecurity.sophos.com/…
- ‘I forgot my password’ doesn’t impress judge in a child images case – nakedsecurity.sophos.com/…
- Prosecutors access data from locked phones of 100 Trump protesters – nakedsecurity.sophos.com/…
Palette Cleansers
- CGP Grey Explains US Social Security Cards (and why they suck so much) – www.cgpgrey.com/…
- A Brief History of Random Numbers – medium.freecodecamp.com/…
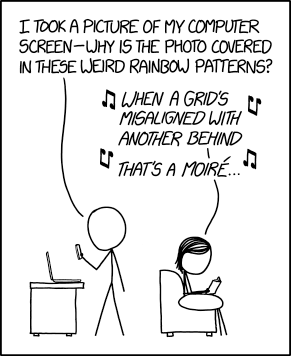
- Color Pattern – xkcd.com/…


Bart, it looks as if you have been considering only the mainstream media’s interpretation of the acton by Congress on ISP’s “selling” customer information.
Here’s a Wall Street Journal’s editorial on the subject:
The Phony Internet Privacy Panic – WSJ 4/3/17, 10)42 AM
https://www.wsj.com/articles/the-phony-internet-privacy-panic-1491000504 Page 1 of 2
Perhaps you’ve read that Congress voted to empower cable providers to collect your
personal information and sell it, unraveling “landmark” privacy protections from the
Federal Communications Commission. The partisans and reporters pumping this claim
are—let’s be kind—uninformed, so allow us to add a few facts.
The House voted this week to rescind an Obama Administration regulation requiring
that cable customers “opt in” to allow data mining of their preferences, which allows
companies to feature targeted ads or improve service. The rule passed in a partisan FCC
vote last year but never took effect. This belies the idea that Comcast and other invented
villains will have some “new freedom” to auction off your data. President Trump is
expected to sign the bill, which already passed the Senate. The result will be . . . the
status quo.
The FCC didn’t roll out these rules in response to gross privacy invasions. The agency
lacked jurisdiction until 2015 when it snatched authority from the Federal Trade
Commission by reclassifying the internet as a public utility. The FTC had punished bad
actors in privacy and data security for years, with more than 150 enforcement actions.
One best privacy practice is offering customers the choice to “opt out”—most consumers
are willing to exchange their viewing habits for more personalized experiences, and the
Rand Pauls of the world can elude collection. Cable customers have this option now. For
sensitive information like Social Security numbers, consumers have to opt in. This
framework protected privacy while allowing innovation.
The FCC ditched this approach and promulgated a rule that, curiously, did not apply to
companies like Google or Amazon, whose business model includes monetizing massive
data collection—what panda videos you watch or which gardening tools you buy. The
rule was designed to give an edge to Twitter and friends in online advertising, a field
already dominated by Silicon Valley.
The crew pushing the rule say cable companies deserve scrutiny because it is easy to
change websites but hard to change internet-service providers. The reality is the
reverse: The average internet user connects through six devices, according to a paper
last year from Georgia Tech, and moves across locations and networks. But which search
engine do you use, whether on your home laptop or iPhone at work? Probably Google.
Plus: Encryption and other technology will soon shield some 70% of the internet from
service providers.
What this week’s tumult means for your privacy online is nothing. FCC Chairman Ajit
Pai and FTC Chairwoman Maureen Ohlhausen issued a joint statement saying they’d
work together to build a “comprehensive and consistent framework” for privacy that
doesn’t favor some tech companies over others. The interim is governed by FCC
guidelines that have been in place for years.
These details haven’t stopped headlines like “How the Republicans Sold Your Privacy to
Internet Providers.” That one ran atop a piece by President Obama’s FCC Chairman Tom
Wheeler, who continues to shore up his legacy as a partisan. The misinformation
campaign is an attempt to bully Republicans and Chairman Pai out of reversing eight
years of capricious regulation. Both deserve credit for not buckling amid the phony
meltdown.
Appeared in the Apr. 01, 2017, print edition.
Copyright ©2017 Dow Jones & Company, Inc. All Rights Reserved
This copy is for your personal, non-commercial use only. To order presentation-ready copies for distribution to your colleagues, clients or customers visit
http://www.djreprints.com.
Hi Ralson,
There’s nothing in that article that I didn’t know already, and it contains no facts that disagree with what I said on the show. It’s an opinion piece, and it expresses an opinion I flatly disagree with. I specifically addressed the distraction tactic of trying to make this about Google, and the article goes right to that flawed argument.
One thing I will add is that if it is true that these rules are meaningless, then why the big lobbying campaign to get them overturned? Also, is the best time to overturn regulations you hate not before they go into effect? Does that in any way diminish the need for such regulations?
Bottom line, you and Google have a contract where you explicitly agree to being tracked in exchange for using their services for no monetary cost. Your ISP on the other hand is a utility provider in an extremely privileged position whom you pay to provide you with a basic service. Expecting them to allow you to opt-in to them using that position of privilege to gather your personal data for their profit seems entirely reasonable to me. Repealing regulation that was in the process of introducing such basic safe-guards is clearly consumer-hostile, and hence, a bad decision in my opinion.
Bart.
Given the post by Bart, the comment by Ralston, and the response by Bart, I have to say that it is good to see democracy – the debate itself – in action, but I have to side with Bart on this one.
Yes, I am fully aware the this legislation does not directly affect me very much, but it is the principle that matters.