 Back in August of 2013, Bart helped me figure out how to wrest control from the Verizon Actiontec FiOS router and let my Airport Extreme control my network. It was non-obvious, so he drew a diagram that I turned into a full tutorial per his instructions. The basic idea is to disable WiFi on the Verizon router, and have it simply pass out IP addresses using DHCP and send traffic straight through to the Airport Extreme. We also set the DMZ on the Verizon router to a static IP and passed that right to the Airport. The purpose of that step was to eliminate the requirement to do port forwarding on both routers if I ever needed to access something inside the network.
Back in August of 2013, Bart helped me figure out how to wrest control from the Verizon Actiontec FiOS router and let my Airport Extreme control my network. It was non-obvious, so he drew a diagram that I turned into a full tutorial per his instructions. The basic idea is to disable WiFi on the Verizon router, and have it simply pass out IP addresses using DHCP and send traffic straight through to the Airport Extreme. We also set the DMZ on the Verizon router to a static IP and passed that right to the Airport. The purpose of that step was to eliminate the requirement to do port forwarding on both routers if I ever needed to access something inside the network.
All of this worked great, I was able to pretty much ignore the Verizon router for the last three years.
 But then In Chit Chat Across the Pond #435 last April, Bart explained to us the dangers of having IoT devices on our networks. Being Bart, he didn’t just talk about the dangers, he also gave us a solution. He taught us how to use three routers instead of one to isolate our trusted computing devices on one router’s network and put the icky IoT devices on the other router’s network.
But then In Chit Chat Across the Pond #435 last April, Bart explained to us the dangers of having IoT devices on our networks. Being Bart, he didn’t just talk about the dangers, he also gave us a solution. He taught us how to use three routers instead of one to isolate our trusted computing devices on one router’s network and put the icky IoT devices on the other router’s network.
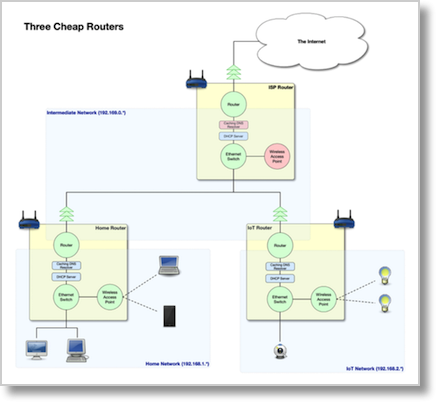
The topology he suggests is to have one router that takes the Internet traffic from the modem, and then passes it to two routers in parallel with each other. Bart was careful to explain that you could do this with three cheap routers.
I already had the Verizon router and my Airport Extreme, so this meant I had an excuse to buy the Netgear Nighthawk X8 that I’d been coveting.
What I never described was how I put the different pieces of Bart’s advice together. Isolating the IoT devices and using the three routers to do it. I realized that if I didn’t explain this, I could never tell the last bit of the TiVo story from two weeks ago. Heck, I didn’t even tell you that there was “one more thing” about the TiVos because I couldn’t without explaining the network. Plus, this gave me an excuse to make another draw.io diagram.
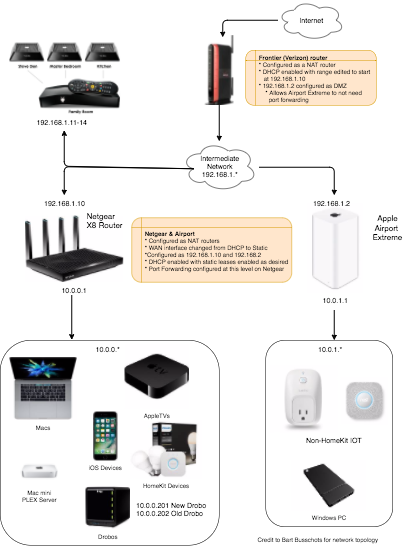
Let’s walk through the diagram to explain how all this works together. At the top we’ve got the nice little Internet cloud (which is a legal requirement for all network diagrams) which goes from the modem into the Verizon router. The Verizon router then creates an intermediate network on IP 192.168.1.X.
The Verizon router gives a static IP to the Netgear router at 192.168.1.10, and gives the Airport Extreme 192.168.1.2. Each of those routers creates its own internal network.
The Netgear router creates its network in the IP range of 10.0.0.x. Inside that network we have our Macs, including our Mac mini PLEX server, our Apple TVs, our iOS Devices, our Drobos (network attached storage) and finally any HomeKit-compatible IoT devices. We actively decided to trust HomeKit devices inside the same network with our most private data.
In parallel, the Airport Extreme creates an internal network with the IP range of 10.0.1.X. On this network, we put all non-HomeKit devices such as our Nest smoke detector and our Belkin switches. And of course that’s where we put our one Windows PC, the Kangaroo.
With this design, as Bart explained to us, any traffic sent to or from the unclean network hosted by the Airport simply cannot traverse over to the Netgear’s network. The two networks are completely isolated from each other.
I can talk to the devices on the IoT network, but only if they’re set up to talk to the Internet. For example, the Belkin switches can be controlled via an iOS app when I’m away from the house, so I can still do that, but they still can’t talk to the safe network.
Now I promised you that there was a TiVo angle to this story. As I explained in the discussion of the TiVos, our house has coax running to each room in the house, and because we have FiOS, that means we have a MoCA network, which is Ethernet over coax. We plugged the TiVos into the coax and that allowed them to talk to the Internet. But the question is, on which of my networks were the TiVos actually connected?
As I mentioned earlier, the Verizon router is connected to the modem, and that’s over coax. So when the TiVos are plugged into coax, they receive their network traffic via the Verizon router. I was able to verify that by looking in the Verizon router’s admin page where I could see all of the TiVos on the DHCP list, and all in the 192.168.1.X range.
You could probably care less where the TiVos are in my network, but I bring this up because of another question. Steve doesn’t have an Ethernet jack in his study, so he gets his network over WiFi from the Netgear. I’ve always wanted to figure out a way to easily have him be hard wired. His study does have a coax cable coming into it, which today goes into his TiVo. But what if I could put a splitter on that coax and turn it into Ethernet to go to his computer?
Well it turns out that’s a really bad idea. If I put him on coax, he’d be connected directly to the Verizon router along with the TiVos. The reason that’s a bad idea is because the Verizon router is in series with the Airport Extreme which hosts all the unclean IoT devices. That means anything creepy that was coming from the IoT devices could attack his computer, completely defeating the purpose of isolating our computers from our IoT network.
We were sad, but only for a minute. We looked back at the iperf testing we did on the Netgear Nighthawk X8 and realized Steve is currently getting 391mbps served out from that wicked fast router. The fact that he shares a wall with the room it’s in might be a contributor, but it shows that there’s no reason to put his machine at risk just for speed.
In closing on this topic I have to confess something. One of the byproducts of writing up stories like this for you is that it gives me a reference to go back to so I can remember things I’ve done. I kept looking back on podfeet.com and I couldn’t find one diagram that explains my entire network. I’ve created this post as an excuse to put it on line so I can find it later. Hope that’s ok.

Thx for your very clear explanation of SMHO network administration at its most efficient and effective! I am a 2nd semester Cisco CCENT student and (long-time member of LAPUG). I am living and breathing routing and switching this year. Its been a struggle as the Cisco material is presented without the real world specifics I need to be taught. And, as you know, the content itself can be challenging.
That said I’ve spent more time than I should have to search for real world explanations that would make all the R & S information come to life. Your real world explanation has turned on the light bulb, and I can move forward with context in my Cisco studies. BTW: I had bookmarked this link some time before I took this class and ran across it today.