I’ve got a networking adventure to tell you about that has a very surprising ending. While the specifics of the story will be recounted purely for your entertainment, there are some steps along the way that might help you in diagnosing technical problems. Remember, we have two engineers with masters degrees in the house so […]
Continue readingTag: network
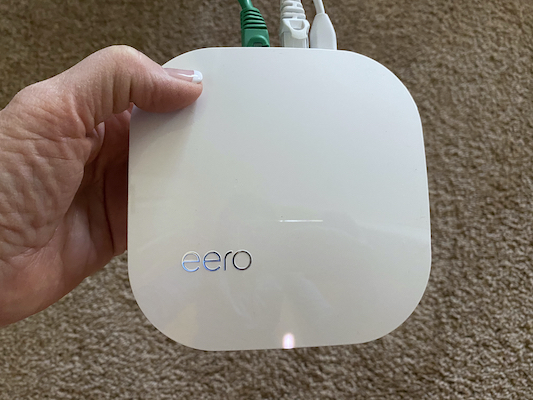
5 Stars for Eero Phone Support
Eero Pro This week in a later article, you’re going to learn about how Steve and I are having solar panels added to our home, and I hope the information I’ll give you might help you make your own decisions about solar. One part that I won’t really dwell on is that for the better […]
Continue readingTiny Tip – How to Pause 5GHz on eero Mesh to Connect IoT Devices
Internet of Things devices (IoT), are proliferating into our lives, saving us from the incredibly arduous tasks of turning off light bulbs and closing our blinds. If you’ve been playing with IoT for any length of time, you know what I’m talking about. Setting up IoT devices usually follows this generic set of steps: Launch […]
Continue readingMoving from Netgear to eero
4 years ago, I told you about my wicked cool new router, the Netgear Nighthawk X8 AC5300 tri-band router. I bought it about 3 minutes before the whole mesh router craze hit the market. A while later, I tested it against Netgear’s Orbi mesh router and the “normal” router actually outperformed the 2-unit Orbi for […]
Continue readingDiagnosing Network Problems Remotely
My mother-in-law Merlee is one of my favorite people on the planet. She’s one of the kindest, most caring people I know. But this week she made me love her even more, because of how geeky she is. A few months ago Steve’s parents moved from 2 hours away to 4 hours away. It’s not […]
Continue readingSolving Network Problems – by Helma from the Netherlands
Hi Allison, here are some tips on solving network problems. I hope they might benefit others. As many of us geeks, I have built quite an extended internal network over the years. All devices that need a static IP address have been entered into the router in the reserved IP address section. I decided to […]
Continue readingNC #614 Podfeet Redesign, Nebula Projectors, Nonda Connected Car, Crazy Network, C-me Selfie Drone, Braven Flye Earbuds, Backblaze
Announcing a new site design for podfeet – go kick the tires at https://podfeet.com/beta2. My Affinity Photo 1.5 tutorial is up at ScreenCasts Online. We hear from Anker about their new Nebula projected displays, Nonda talks about their connected car devices, I explain more about how cool our network is now that we’ve folded in […]
Continue readingCCATP #475 Bart Busschots Explains IPv6
I made a deal with Bart when he started his two podcasts Let’s Talk Apple and Let’s Talk Photography that he would never have to be on more than every other week. But this week I tricked him by asking him if he’d come on and explain IPv6 to me. His first answer was that […]
Continue reading3 Networks + MoCA + TiVos
Back in August of 2013, Bart helped me figure out how to wrest control from the Verizon Actiontec FiOS router and let my Airport Extreme control my network. It was non-obvious, so he drew a diagram that I turned into a full tutorial per his instructions. The basic idea is to disable WiFi on the […]
Continue readingTime Machine Backups from the Netgear X8 USB Port
Steve Davidson posted a great question on podfeet.com on my post about the Netgear Nighthawk X8 router: Allison, now that Apple has end-of-lifed the AirPort Extreme (my device of choice until now), I’m taking another look at the Netgear Nighthawk X8 (your endorsement has to be worth $$$ to Netgear). Besides the obvious reasons to […]
Continue reading